CoreBot
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 14,574 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 3,667 |
| First Seen: | September 1, 2015 |
| Last Seen: | August 26, 2023 |
| OS(es) Affected: | Windows |
CoreBot is a new information gathering threat that was recently discovered by PC security researchers. According to their reports, CoreBot is a sophisticated threat attack that is designed to collect sensitive data such as passwords or online banking data. PC security analysts were impressed by CoreBot's modular design that allows CoreBot's creators quickly and easily add new mechanisms to CoreBot's arsenal. This type of design also allows those people using CoreBot to adapt CoreBot for the type of threat campaign that they are attempting to wage effortlessly. CoreBot receives its name because its compiled file is named 'core'. CoreBot may not be detected by security software or receive some kind of generic name if they have not been recently updated. On the surface, CoreBot looks similar to other information-collecting threats. However, there are certain mechanisms in CoreBot that make it an interesting new threat.
Table of Contents
CoreBot and Other Information Fetching Threats
Generic threats may be regarded as less threatening than elaborate attacks because they are less targeted. However, in the case of an information-collecting threat, the opposite is true. Generic threats may gather passwords without discriminating, meaning that it poses a great threat to victim's accounts. A targeted attack may be designed to gather only a banking password. However, a generic information stealer may compromise the victim's email password, software keys, data saved on the affected drive, bank account information, online wallets and other data. One additional issue with generic information stealers is that they may have the capacity to download and install other threats on the victim's computer. By using these types of attacks, third parties may gather large amounts of data using different botnets and then sell it or trade it on underground forums to people who may find ways to make money with the information.
How CoreBot may Infiltrate a Computer
CoreBot may enter a computer with the help of a dropper. A dropper is a threat component that may deliver a Trojan to a targeted computer. The dropper will essentially launch a svchost process, deliver the CoreBot file and then execute this corrupted file. After the dropper completes its task, it deletes itself from the victim's computer. CoreBot's most interesting feature is how well its modular system is executed. CoreBot will download its plug-ins from its command and control server and then load advertisements them. CoreBot will do this right after it has ensured that CoreBot will persist on the affected computer, loading whenever Windows starts up. The main plug-in that CoreBot currently uses is called Stealer, and it allows CoreBot to collect passwords. CoreBot is currently not capable of intercepting information in real time; rather, CoreBot collects passwords that have been stored on the victim's Web browsers, FTP clients, mail clients and other applications. CoreBot also may collect private certificates, making it particularly threatening.
Dealing with CoreBot and Similar Threats
It is nearly impossible for a large organization to avoid threats. In most cases, threats are installed by computer users themselves and, in the case of a large organization, it may be an employee that opens a corrupted file in a phishing email message or visits an attack website resulting in a threat attack that may quickly spread throughout a network. Increasing employee awareness of these types of attacks through education and training is a great way to prevent CoreBot attacks. Computer users also should ensure that a strong security application that is fully up to date is used to protect computers from attacks. A strong anti-spam filter is also essential in preventing compromised email messages from arriving into an inbox in the first place. Although CoreBot is currently in its initial stages, its unique design makes CoreBot likely that new, more threatening plug-ins and modules will be developed for this threat.
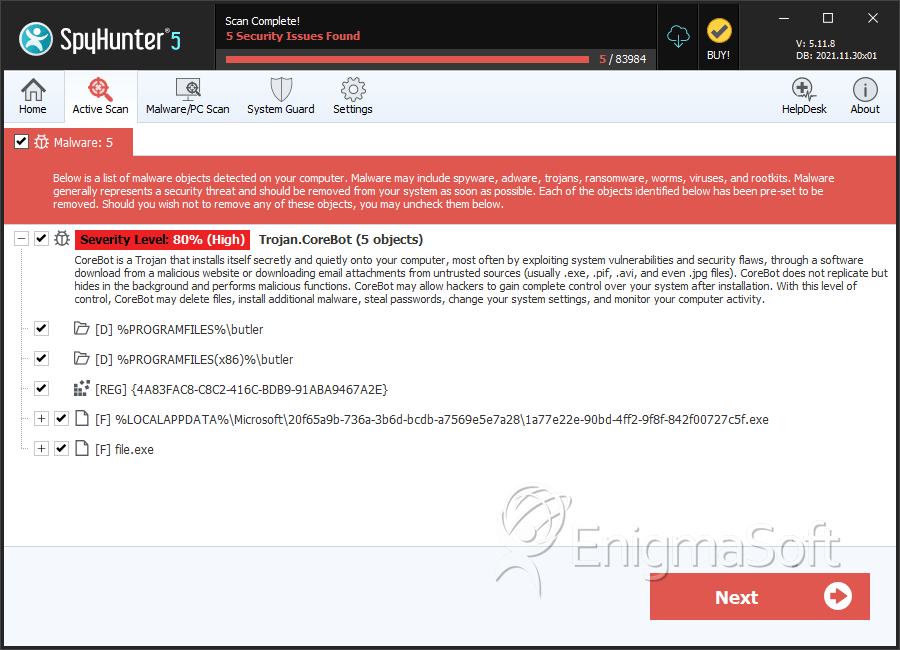
SpyHunter Detects & Remove CoreBot
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 1a77e22e-90bd-4ff2-9f8f-842f00727c5f.exe | 067ef28f3f65d287701062ae63e8411d | 1 |
| 2. | file.exe | ce890607d0f0581a1afc9b3a8f6e012d | 0 |
| 3. | file.exe | 89464e2f384c5d96d052b398ad3ae7b4 | 0 |
| 4. | file.exe | 33ddcae9c1db266101b9e12fec97ec38 | 0 |
| 5. | file.exe | a85495108f27c122c3922db8ba27fa21 | 0 |
Registry Details
Directories
CoreBot may create the following directory or directories:
| %PROGRAMFILES%\butler |
| %PROGRAMFILES(x86)%\butler |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.