Chr0mium Browser
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 148 |
| First Seen: | February 29, 2016 |
| Last Seen: | June 6, 2022 |
| OS(es) Affected: | Windows |
Some computer users have reported that their Web browser was changed to the Chr0mium Browser automatically. The Chr0mium Browser looks and acts like Google Chrome, but it may redirect computer users to a 'password manager' website and other unwanted content as part of a tactic that may be used to obtain their online passwords or expose them to unwanted content. It is highly likely that the Chr0mium Browser also has the capacity for tracking the computer users' online activities, expose them to unwanted advertisements, and deliver possibly unwanted components to their computers.
Table of Contents
What’s the Purpose of the Chr0mium Browser?
The Chr0mium Browser exhibits behavior that makes it very likely that the Chr0mium Browser, and is used to collect the computer users' online passwords and important information such as credit card numbers or online banking information. As part of its tactic, the Chr0mium Browser may change the users computers' shortcuts on the Task Bar, Desktop, and Start Menu, leading to the Chr0mium Browser instead of to their default Web browser, in most casesGoogle Chrome. However, since the icons and appearance of the Web browser are the same, computer users will rarely be aware that they are using the Chr0mium Browser instead of their preferred Web browser. Because of this, make sure that all online passwords and private data have not been compromised, and that no threats have been installed on an affected computer after removing the Chr0mium Browser and restoring the default Web browser.
The Misleading Tactics Used by the Chr0mium Browser
The Chr0mium Browser is a bogus version of Google Chrome. The purpose of the Chr0mium Browser is to make computer users believe that they are using Google Chrome instead of this fake Web browser. Computer users may be prompted to enter their password information, in a fake 'password manager' Web page or some phishing website. The Chr0mium Browser takes over a computer silently, replacing all instances of Google Chrome with its own links and content. However, Google Chrome will not be removed from the affected computer; it will simply not launch as the default Web browser when computer users try to load a Web page. Malware analysts have encountered numerous fake versions of the Google Chrome Web browser that may be associated with questionable free programs such as fake PDF managers and similar low-quality apps.
How the Chr0mium Browser may Trick Computer Users
When the Chr0mium Browser is installed on a PC, it will pretend that the Chr0mium Browser is the Google Chrome Web browser. The tactic is simple to understand: if computer users think that the Chr0mium Browser is Google Chrome, they will not falter when it comes to entering their credit card number, online banking information, or similar data into a Web page. Other possible uses for fake versions of the Google Chrome Web browser include delivering unwanted content or components to computer users such as numerous advertisements, Web browser extensions and affiliate marketing links. Computer users should make sure that their Web browser is effectively still Google Chrome, especially if they are observing odd behavior. Google Chrome also should show up in the Task Manager as 'Chrome.exe' (the Chr0mium Browser may appear as the 'Chr0mium.exe' or 'chrbr.exe').
Dealing with the Chr0mium Browser
The first step in dealing with the Chr0mium Browser is to remove this fake Web browser completely. Computer users should uninstall this Web browser manually, deleting its files and Registry keys and using the Windows Control Panel to remove the program completely. It also may be necessary to remove all shortcuts created by the Chr0mium Browser and create new shortcuts that lead to the default Web browser instead. As part of the uninstallation process, computer users should use a reputable anti-malware application that is fully up-to-date to scan the affected PC for possible threats or other infections that may have been the result of the Chr0mium Browser infection on their computers.
SpyHunter Detects & Remove Chr0mium Browser
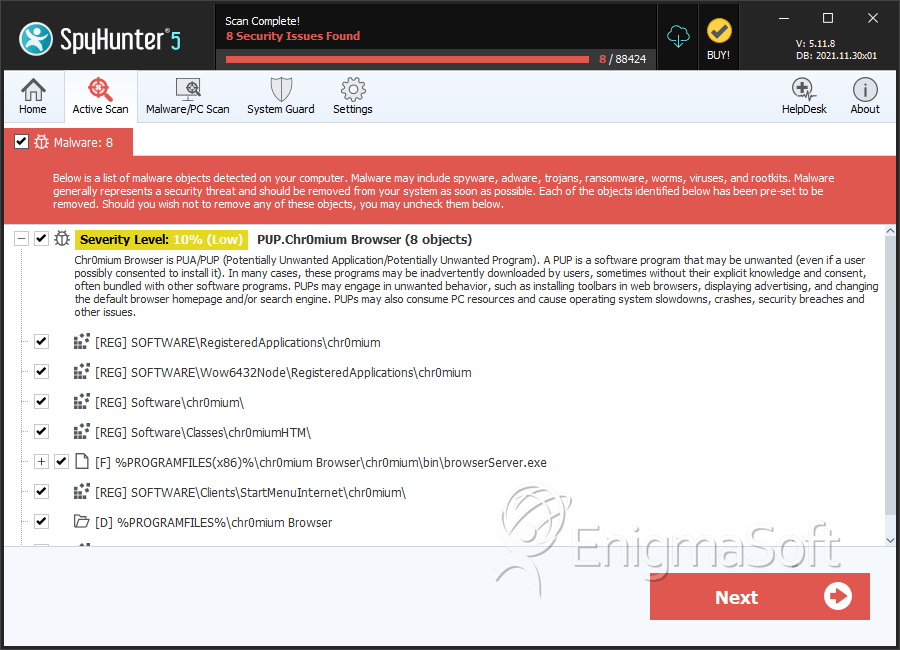
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | browserServer.exe | 9b499c3477930879b2cd23f1330585d8 | 21 |
Registry Details
Directories
Chr0mium Browser may create the following directory or directories:
| %PROGRAMFILES%\chr0mium Browser |
| %PROGRAMFILES(x86)%\chr0mium Browser |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.