Cherchi.biz
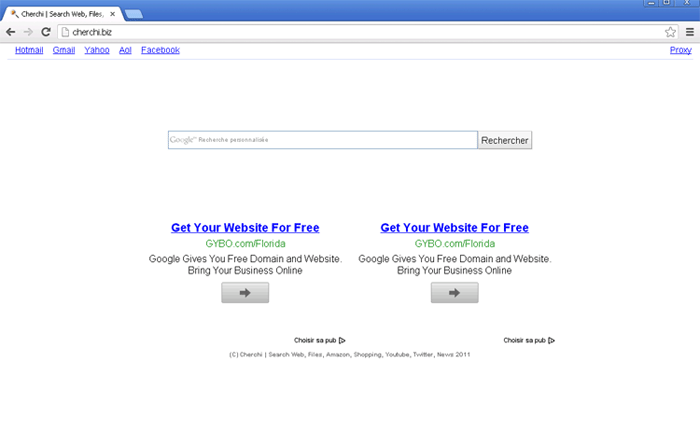
Cherchi.biz Image
ESG malware researchers have observed variants of browser hijackers that are spread using JavaScript Trojans or bundled along with freeware programs (it is essential to note that it is often not the freeware developers at fault but unscrupulous third parties that will take a popular freeware application and bundle it along with their 'helpful' toolbar, which is actually a browser hijacker and a potentially unwanted program). Cherchi.biz is a website associated with these kinds of browser hijackers. If your computer's browser is forcing you to visit Cherchi.biz, this is a sign that your machine has become infected with a dangerous browser hijacker. Since browser hijackers associated with Cherchi.biz take the form of Trojans that affect how your computer establishes an Internet connection, it is important to take immediate action to remove these threats from your computer.
Most computer users would not visit Cherchi.biz on their own. In fact, it is highly likely that the vast majority of Cherchi.biz's traffic comes from computer users that do not have a choice but to visit Cherchi.biz because of the presence of a browser hijacker on their computer. In the case of Cherchi.biz, this website is promoted by forcing computer users to visit Cherchi.biz repeatedly against their will. While there are numerous symptoms associated with browser hijackers, the two most common of these involve forced redirects to the Cherchi.biz website, often after searching on Google or clicking on a link, and changing the victim's homepage to Cherchi.biz without permission (ensuring that the victim visits Cherchi.biz as soon as the affected web browser is launched.
To stop Cherchi.biz redirects, it is not enough to reinstall your web browser. This is because browser hijackers associated with Cherchi.biz will often infect your computer on a deeper level. Instead, ESG malware analysts decidedly advise PC users to use a reliable anti-malware product daily updated to scan your computer and remove any browser hijackers that may be causing problems with your web browser. To prevent future infections and to stay away from unsafe online content such as pornography or file sharing websites, the use of a real time anti-malware scanner and a strong firewall is decisive.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.