Carbanak
Carbanak is a banking Trojan that is used to take money from computer users. PC security analysts have observed a rash of attacks involving Carbanak recently, which had been inactive for some time. Carbanak has re-emerged with a new code signing certificate from Comodo that has allowed Carbanak to increase its attacks in recent days. PC security analysts have reported that Carbanak has been used to carry out attacks against banks and businesses all around the world. Computer users and businesses should protect their computers from Carbanak with the help of a reliable security program that was recently updated with the latest threat definitions.
Table of Contents
The Creators of Carbanak are Updating It Consistently
Carbanak also goes by the alias Anunak. Carbanak was discovered and analyzed for the first time in February of 2015. It was originally estimated that the people responsible for Carbanak had managed to gain access to about one hundred banks all over the world and were responsible for collecting up to one billion USD! Carbanak gained lots of attention in February, but since then had remained largely inactive, making sporadic attacks, but nothing as spectacular as those enormous heists. However, Carbanak infections have evolved gradually in order to always stay ahead of firewall and security software updates.
Comparing the Newest Version of Carbanak with Its Predecessor
The newest versions of Carbanak use a specific communications protocol that make it more difficult to isolate and intercept these infections. The newest variants of Carbanak have been spotted again, attacking the same types of financial institutions as the widely publicized attacks in February. Carbanak uses predefined IP addresses to communicate with its Command and Control servers (before Carbanak would use randomly generated names and addresses.) Carbanak also includes a new proprietary protocol that Carbanak uses during its attack for internal communication and management of its plug-ins.
Carbanak hides on the victim's computer by infecting a memory process, svchost.exe, allowing Carbanak to remain undetected even on the victim's Task Manager. Carbanak has a modular Framework that allows Carbanak to adapt to different situations quickly or be customized before specific attacks to prey on victims' specific weaknesses. Carbanak is also threatening because Carbanak uses a legitimate code signing certificate in order to prevent being intercepted by security software. Comodo, which issued the Carbanak certificate, is a legal business located in Russia. At this point, it is especially obvious that Carbanak is based in Russia. In fact, one of the Carbanak servers has been traced to Russian security forces. PC security analysts consider the possibility that the people responsible for Carbanak have registered real businesses for the only purpose of having some kind of legal outlet and base to help them carry out their Carbanak-related attacks. One billion dollars can hardly go unnoticed, and registering a legitimate company with its own bank accounts to use for their operations may allow the people responsible for Carbanak carry out their transfers and launder their ill-gained profits.
Dealing with Carbanak
The best way to prevent Carbanak from gaining access to your computer or your company's network is to instill good online security practices. This means educating computer users so that they will avoid opening unknown email attachments or clicking on unknown embedded links. Strong security software that is fully up-to-date should always be in use – make sure that firewalls and similar software are not turned off to improve performance since a single Carbanak breach may compromise an entire corporate network. Finally, if you suspect a Carbanak infection, you should safeguard all bank accounts and avoid accessing it from the potentially infected computer until Carbanak has been cleared.
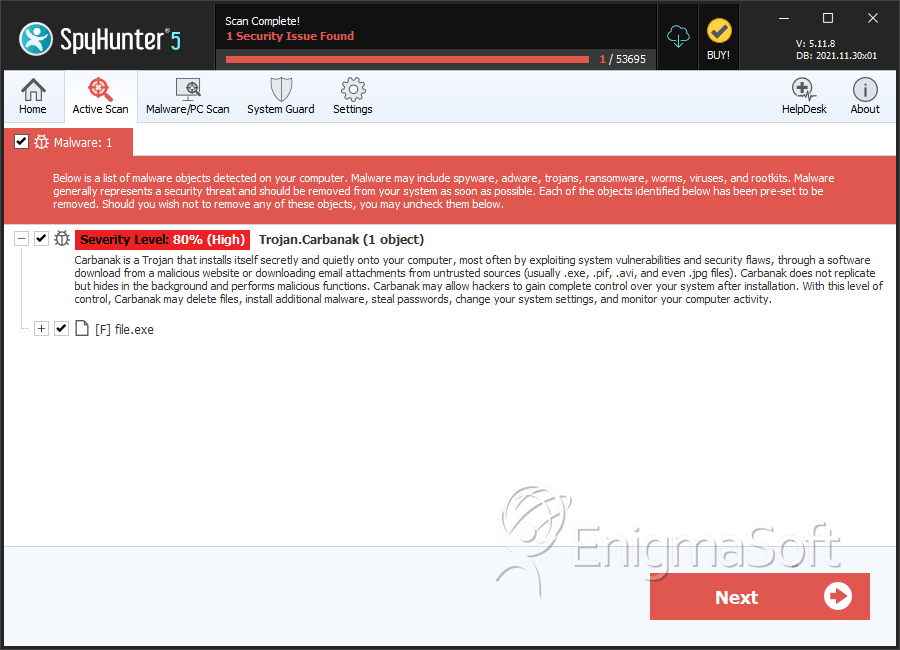
SpyHunter Detects & Remove Carbanak
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | a2643fe61f4b65704cfe1ebc55e2b301 | 0 |

