Bundespolizei Ukash
Bundespolizei Ukash Image
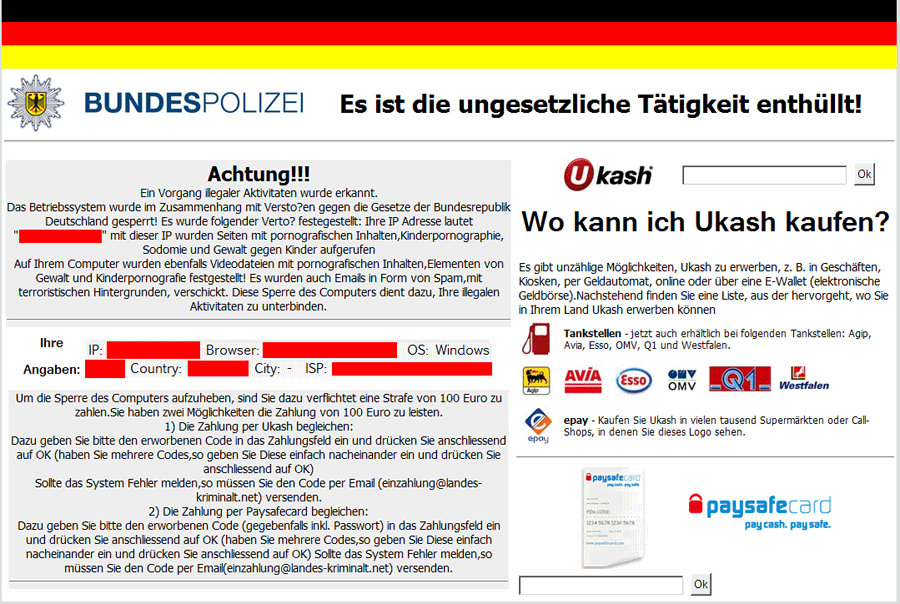
Bundespolizei Ukash, known by various names, is one of the many known variants of the so-called Ukash Virus. This infection is actually a ransomware Trojan with a Winlocker component designed to block access to Windows and then force victims to pay a ransom using the Ukash or PaySafeCard money transfer services. Bundespolizei Ukash is the German variety of a ransomware attack that has been known to target numerous countries all around the world. ESG security researchers recommend ignoring the Bundespolizei Ukash Trojan's message or paying the ransom that this Trojan demands. Instead, Bundespolizei Ukash infections should be removed with the help of a strong, fully-updated anti-malware program.
Table of Contents
The Bundespolizei Ukash Scam
Like the many other Ukash Virus variants, the Bundespolizei Ukash Trojan will take over the victim's computer system with a simple Winlocker component. This Winlocker blocks access to the victim's computer's Desktop, Task Manager, Command Line, Registry Editor and other Windows components that could conceivably be used to remove this threat. After blocking the victims' access to their own files, Bundespolizei Ukash will demand a ransom by blocking the entire screen with a threatening message. This message will claim that the infected system was used for illegal purposes, such as viewing and distributing child pornography. By claiming to have been installed by the Bundespolizei (the main German federal police agency), this message, written entirely in German, will demand the payment of a one-hundred euro 'fine.' ESG security researchers suspect that the many variants of the Ukash Virus will change depending on the victim's IP. While the Bundespolizei Ukash Virus attacks computer systems located in Germany, ransomware attacks claiming to be messages from the Metropolitan Police attack computer systems in the United Kingdom. Dozens of variants of the Bundespolizei Ukash, corresponding to several countries in North America and Europe have been detected since 2011.
The main difficulty associated with the removal of the Bundespolizei Ukash Virus is regaining access to the infected system. In fact, the actual removal process is not particularly difficult and can be handled by most anti-malware applications that have been properly updated. To bypass the Bundespolizei Ukash infection, ESG malware analysts advise booting up Windows using an alternate boot method such as starting up from a network drive or from a Windows CD.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %AppData%\HEX-5823-6893-6818\jusched.exe |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.