Buhtrap
Small and medium businesses have become one of the favorite target groups of cybercriminals – cleverly executed attacks businesses that fall into this category may provide them with access to the financial data of employees and customers, as well as with the opportunity to continuously steal valuable data from the infected system. One tool that has been frequently involved in such attacks is Buhtrap – the first campaigns involving this particular malware strain were seen in 2014, and since then this threat has undergone through several reworks that have modified its behavior and abilities.
The most recent Buhtrap has seen a large number of infected computers daily, and threat experts have determined that the attackers are focusing on businesses based in Russia. One of the propagation campaigns linked to Buhtrap relies on the Yandex.Direct advertising portal to deliver malicious ads that claim to lead users to a download page for a rich collection of document templates – something that many employees may be interested in, especially if they are part a part of the financial department (likely to be Buhtrap’s primary target.)
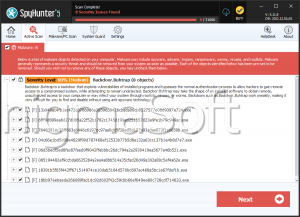
While in the past the Buhtrap has been linked to activities typical for banking Trojans, this particular campaign has been using it as a basic backdoor and downloader – once initialized on a system, it can establish a connection with the attacker’s server and wait for instructions. The Buhtrap downloader has been used in combination with all sorts of malicious tools that appear to be a part of the toolkit of the attackers.
One of the Buhtrap campaigns was also used to deliver a file-encryption tool that mimics the behavior of ransomware and is being labeled ‘Filecoder.Buhtrap’ by many security products. This basic ransomware piece was only observed in this particular campaign, and there is still no information about the demands of the attackers, or if it is possible to decrypt the locked files for free. However, the information available is that the Filecoder.Buhtrap does not need an Internet connection to work, and it is capable of terminating applications that may prevent it from accessing and encrypting files.
Protecting your company from threats like this one requires training all employees to avoid browsing suspicious websites, or to download files from unknown sources. In addition to this, all company computers are to be protected by a trustworthy antivirus program that gets regular updates.