Booster.exe CPU Miner
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 53 |
| First Seen: | October 23, 2017 |
| Last Seen: | December 30, 2020 |
| OS(es) Affected: | Windows |
The Booster.exe CPU Miner is a program that is used to mine crypto-currencies that rely on the blockchain technology such as Monero, Bitcoin, Litecoin and Siacoin. Tools like the Booster.exe CPU Miner are useful to users who are interested in making a profit from renting processing power to digital currency markets. However, the Booster.exe CPU Miner is deployed by Trojan-Droppers, and hacking remote computers manually. The Booster.exe CPU Miner is used by Black Hat hackers to make a profit from using the CPUs of the infected machines. The Booster.exe CPU Miner may be promoted to users as a free program dubbed 'PC Booster,' which is supposed to improve your machine's performance. Needless to say, the marketing pitch is just a trick intended to convince users to install the Booster.exe CPU Miner.
The miner at hand is observed to run as 'booster.exe' in the Task Manager and feature the app description 'VsGraphics Desktop.' The same description is associated with a legitimate process by Microsoft dubbed 'VsGraphicsDesktopEngine.exe' that is responsible for rendering visual elements on the desktop. It is likely that the programmers behind the Booster.exe CPU Miner used the string 'VsGraphics Desktop' to confuse users and dissuade them from terminating the 'booster.exe' process. That simple trick gave the threat authors good chances of keeping the Booster.exe CPU Miner operational on more devices for longer periods. Additionally, 'booster.exe' may feature a startup entry in the MSCONFIG utility and boot with Windows every time the user runs it on the PC. Reports from security analysts suggest the Booster.exe CPU Miner is programmed to use as much as 25% of available processing power, which allows it to maintain a low profile compared to similar apps such as the Systemcore.exe CPU Miner and the VPNTop CPU Miner. The presence of a CPU Miner on the system can be detrimental to its performance, and you might not fancy the idea of helping hackers make a profit using your hardware. The Booster.exe CPU Miner can be removed along with related Trojan-Droppers using a trusted anti-malware solution.
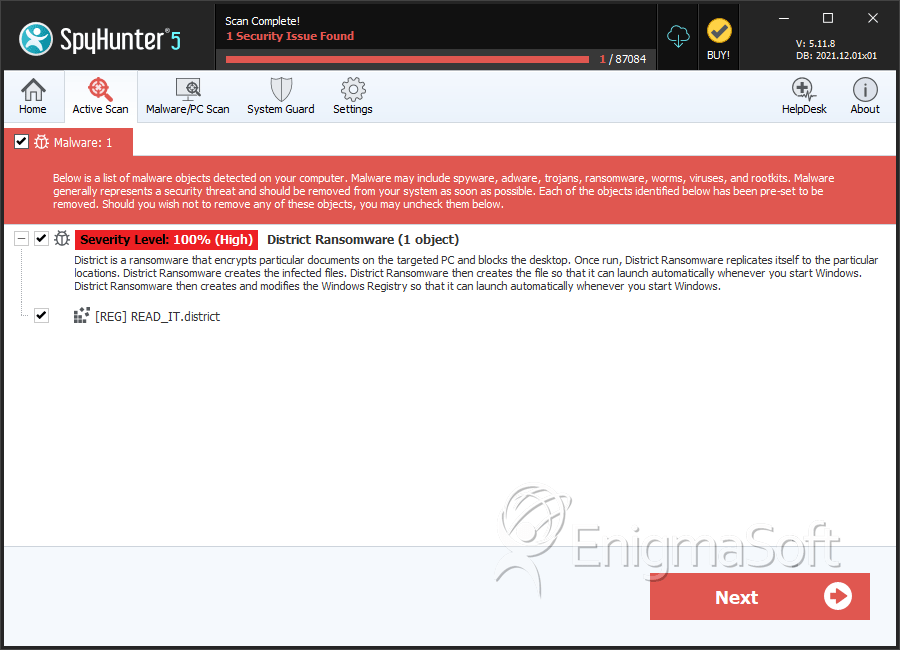
SpyHunter Detects & Remove Booster.exe CPU Miner