Black TENGU Ransomware
Protecting computers, phones, and business networks from malware is no longer optional. Modern threats can lock critical files, steal sensitive information, interrupt operations, and cause serious financial damage within minutes. Ransomware families such as Black TENGU Ransomware demonstrate how cybercriminals combine encryption and data theft to pressure victims into paying.
Table of Contents
Black TENGU Ransomware: Threat Overview
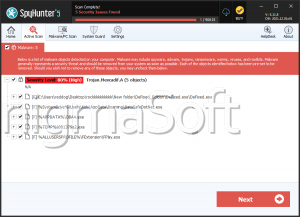
Black TENGU is a sophisticated ransomware strain identified by security researchers. After gaining access to a compromised device, it encrypts stored files so they can no longer be opened normally. During the encryption process, it appends the '.TENGU' extension to affected files. For example, a file named '1.png' becomes '1.png.TENGU,' while '2.pdf' is renamed to '2.pdf.TENGU.'
This renaming behavior is a common indicator of ransomware activity, signaling that the original data has been transformed into an unreadable state. Victims are then left unable to access personal documents, databases, images, archives, and other important files.
The Ransom Note and Double-Extortion Pressure
Black TENGU also drops a ransom note named '_README_TENGU.txt.' According to the message, attackers claim they infiltrated the victim's network, stole confidential data, and encrypted files across the system. The note promises a decryption tool after payment and states that stolen information will supposedly be deleted once the ransom is paid.
The message further warns victims not to attempt third-party decryption or self-recovery, claiming this could permanently damage files. It directs communication through email addresses such as 'tengulocker@cyberfear.com' and 'tengunlocker@onionmail.com', along with a Tor-based chat portal.
This tactic reflects a growing trend known as double extortion. Attackers do not rely only on encryption; they also threaten to leak stolen data publicly unless payment is made. This creates additional pressure on organizations handling customer records, financial documents, or proprietary information.
Why Paying the Ransom Is Risky
Although victims may feel trapped, paying a ransom carries significant risk. Criminal groups often make promises they do not keep. Some victims never receive a working decryption tool, while others are targeted again after showing willingness to pay. Even when files are restored, stolen data may still be sold, leaked, or retained for future blackmail.
The safer recovery path is typically restoring clean backups after the malware has been fully removed from affected systems. Incident response teams should also investigate how the intrusion occurred to prevent reinfection.
How Black TENGU Likely Spreads
Like many ransomware families, Black TENGU may rely on multiple infection channels. Threat actors often use deceptive delivery methods that trick users into launching malicious files or visiting unsafe websites.
Common distribution techniques include:
- Fraudulent emails containing harmful attachments or links
- Fake software updates, tech support scams, and malicious ads
- Exploitation of outdated or unpatched software vulnerabilities
- Pirated software, cracks, key generators, and unofficial download pages
- Infected USB drives, compromised websites, and peer-to-peer sharing networks
Malware payloads are frequently disguised as normal ZIP archives, PDFs, scripts, Office documents, or executable files.
Best Security Practices to Strengthen Malware Defense
Strong prevention combines technology, awareness, and disciplined maintenance. Systems should always run reputable security software with real-time protection enabled. Operating systems, browsers, plugins, and business applications must be patched quickly because known vulnerabilities are often used for ransomware deployment.
Reliable backups are one of the most effective defenses. Important data should be copied regularly to offline or cloud locations that cannot be directly altered by malware. Backup restoration should also be tested so recovery is possible during a real emergency.
Email caution remains essential. Unexpected attachments, urgent payment requests, password reset messages, and unfamiliar links should be treated with suspicion. Organizations benefit greatly from user awareness training that teaches staff how phishing attacks work.
Access control is equally important. Users should avoid working with administrator privileges unless necessary, and remote access tools such as RDP should be secured with strong passwords and multi-factor authentication. Network segmentation can reduce the ability of ransomware to spread across multiple devices.
Recommended protective habits include:
- Keep all software updated and remove unsupported applications
- Maintain multiple backups, including at least one offline copy
- Use strong passwords and enable multi-factor authentication
- Install trusted endpoint protection and firewall defenses
- Avoid pirated software and unverified downloads
Final Assessment
Black TENGU Ransomware represents a dangerous modern threat that combines file encryption, extortion messaging, and possible data theft. Its use of renamed files with the '.TENGU' extension and a dedicated ransom note shows a deliberate campaign designed to pressure victims quickly. The strongest defense is proactive security: patched systems, cautious users, strong authentication, segmented networks, and dependable backups. Organizations and individuals that prepare in advance are far more resilient when ransomware strikes.