BKDR_ZAPCHAST.HVN
ESG security analysts have identified BKDR_ZAPCHAST.HVN as version 3.3 of the DarkComet Trojan. This infamous malware infection allows criminals to gain complete access to the victim's computer system from a remote location. If your computer system has been infected with BKDR_ZAPCHAST.HVN, it is highly likely that criminals can see what you type on your keyboard and have access to your data. BKDR_ZAPCHAST.HVN is distributed by the BKDR_METEO.HVN Trojan, which is disguised as a fake encryption package for Skype (which is completely unnecessary considering that Skype already includes a robust encryption component by default). If you have had contact with a supposed encryption package for this popular VoIP application, your computer system may have been exposed to BKDR_ZAPCHAST.HVN.
Table of Contents
BKDR_ZAPCHAST.HVN and the Syrian Armed Conflict
BKDR_ZAPCHAST.HVN seems to be targeted at a group of people that care desperately about making sure that their Skype conversations are not tampered with or eavesdropped, the rebel faction in the Syrian armed conflict. Like many of the people involved in the Arab uprisings, the Syrian rebels heavily rely on social networks (like Twitter and Facebook) and on online messaging like Skype and Google Chat. One of the reasons that BKDR_ZAPCHAST.HVN is suspected to be associated with an attack against the Syrian rebels is the fact that the fake Skype encryption package is hosted on a server that has been involved in previous online attacks against the Syrian rebel forces.
The DarkComet Trojan is a RAT, that is, a Remote Administration Tool. What this means is that criminals can use this malware infection to take charge of the infected machine from a remote location. Although version 5.0 of this Trojan has already been released and BKDR_ZAPCHAST.HVN is only version 3.3 of the DarkComet Trojan, BKDR_ZAPCHAST.HVN is still considered to be a severe threat to a computer system's security. One of the main dangers of BKDR_ZAPCHAST.HVN is the fact that BKDR_ZAPCHAST.HVN can remain undetected on the victim's computer system, working in the background to gather information about the victim's activities. Some of the ways that BKDR_ZAPCHAST.HVN can be used to attack a machine include manipulating the infected computer system's files (including deleting, editing, duplicating, or uploading these files), blocking essential system components in order to impede access to the infected computer system, recording all activity on the infected computer's keyboard, or taking screenshots of the infected computer system's monitor.
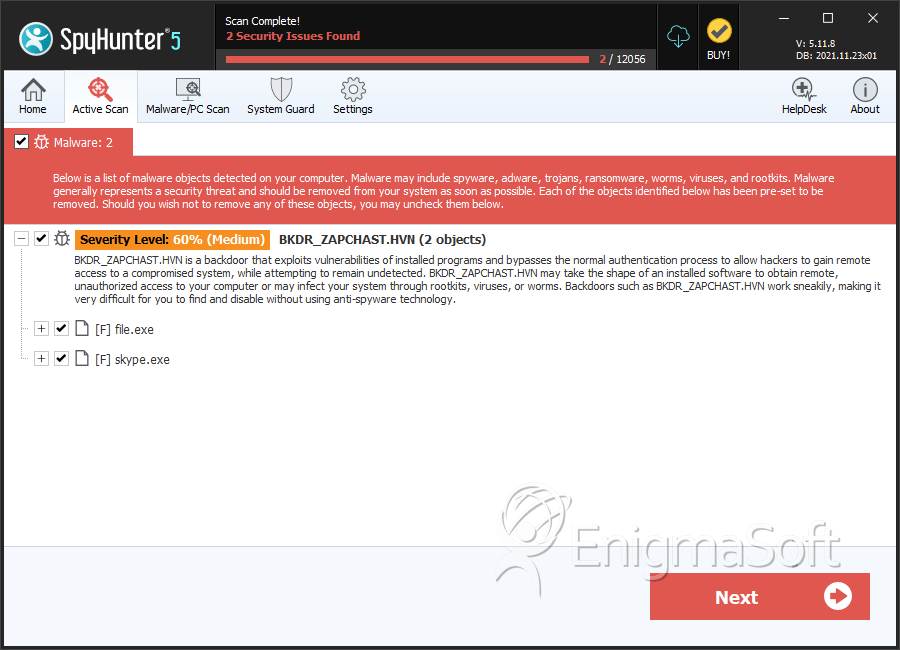
SpyHunter Detects & Remove BKDR_ZAPCHAST.HVN
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | c3bac6f3697349b2ef8adde52e7e8a48 | 0 |
| 2. | file.exe | c0efb93d434be914b635285263ea29e2 | 0 |
| 3. | skype.exe | 09172745ccf3d8e3defdc470452dbe67 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.