BKDR_SIMBOT.EVL
BKDR_SIMBOT.EVL is a backdoor Trojan that is spread via an infected MS PowerPoint document, which is delivered via an infected .PPT file, found as BKDR_SIMBOT.EVL, attached to particular email messages. The malicious .PPT file drops another malicious file named 'Winword.tmp'. 'Winword.tmp' encompasses an inserted Flash file, which exploits a Flash Player vulnerability known as CVE-2011-0611 to download BKDR_SIMBOT.EVL onto the victim's PC. BKDR_SIMBOT.EVL is spread by TROJ_PPDROP.EVL. BKDR_SIMBOT.EVL executes instructions from remote cybercriminals, taking over the corrupted machine. BKDR_SIMBOT.EVL connects to a particular URL to transmit and obtain information. BKDR_SIMBOT.EVL downloads the copies of itself by generating a specific file onto the affected computer. BKDR_SIMBOT.EVL inserts the codes into the processes such as svchost.exe and services.exe. BKDR_SIMBOT.EVL generates the certain registry key so that it can load automatically whenever you boot up Windows. BKDR_SIMBOT.EVL runs the certain instructions from remote cybercriminals.
Table of Contents
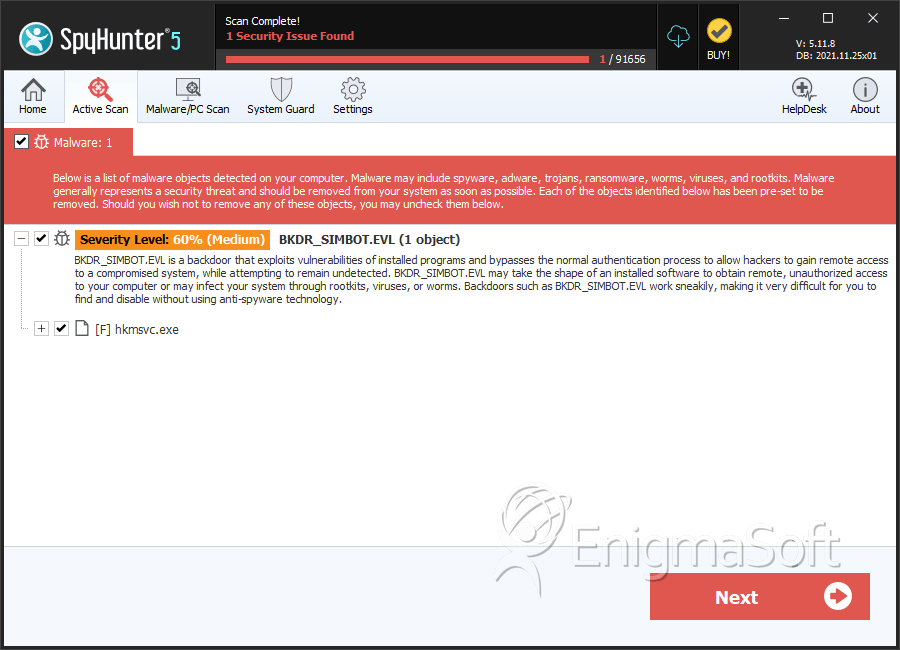
SpyHunter Detects & Remove BKDR_SIMBOT.EVL
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | %UserProfile%\Local Settings\{random filename}.exe | ||
| 2. | hkmsvc.exe | 996376a04c664c6e762f78e98b505b92 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.