BKDR_POISON.BLW
BKDR_POISON.BLW is a dangerous backdoor Trojan that is part of a multi-component malware attack associated with a zero-day vulnerability in the Java Runtime Environment, version 1.7. Zero day is a term used by PC security researchers to refer to exploits found in a program's code before release that have gone undetected by the program's developers. These exploits are quite valuable to malware creators because they can be used to deliver malware that is highly destructive before a program's developers have a chance to patch their program or release a security update. These zero day vulnerabilities often give criminals the ability to carry out malware attacks unopposed for a lengthy window of time during the period in which software developers release a fix to the vulnerability in their software. The BKDR_POISON.BLW backdoor Trojan gives criminals a high level of control over an infected computer, making this a dangerous malware infection that should be dealt with immediately.
Table of Contents
Understanding the Java-Based Malware Attack Leading Up to BKDR_POISON.BLW
The BKDR_POISON.BLW infection is the final step of a multi-component malware attack. This attack initiates with a malicious script contained on an HTML website. This script forces the victim's computer to visit an attack website where a malicious Java applet is loaded. Finally, that Java applet forces the infected computer to download and execute BKDR_POISON.BLW, contained in an executable file that is disguised as a fake update for Adobe Flash Player. These kinds of fake updates, video codecs or media players are common disguises for backdoor Trojans like BKDR_POISON.BLW. The result of this elaborate attack is a backdoor on the infected computer. This is a term that PC security researchers usually use to refer to an unauthorized opening in the infected computer's security. By using this opening, criminals can upload and download data on the infected machine without alerting the victim or the infected computer's security software.
Unfortunately, a BKDR_POISON.BLW infection will usually have very few symptoms, if any at all. However, malware that may be installed using this threat's backdoor will usually cause symptoms on the victim's computer. Since the approach to installing BKDR_POISON.BLW's backdoor on the victim's computer involves Java scripts and applets, disabling Java script for non-essential tasks is probably the best precautionary measure you can take to protect your machine. ESG malware analysts also advise staying away from unsafe websites and maintaining your security software fully updated.
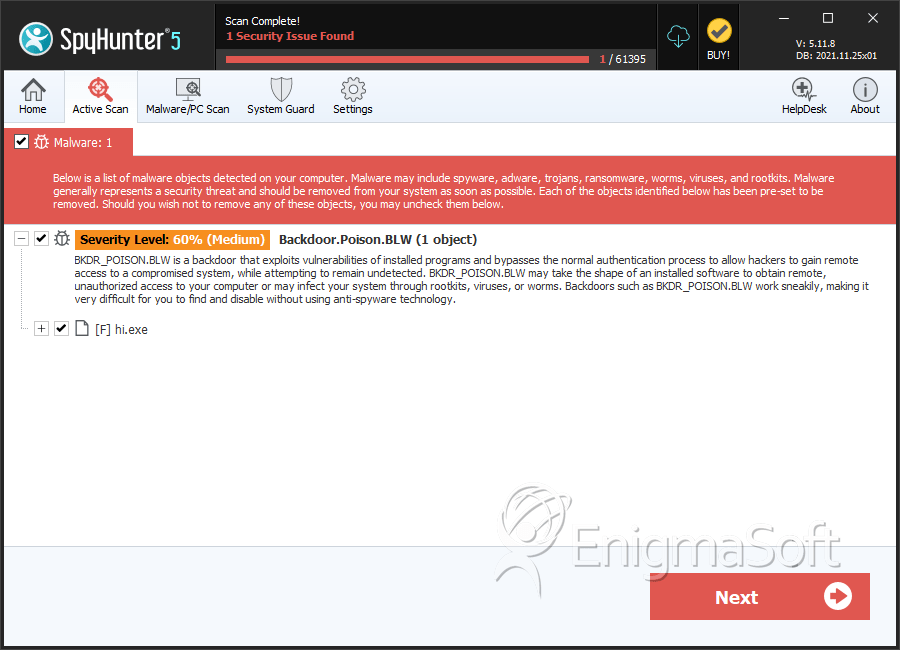
SpyHunter Detects & Remove BKDR_POISON.BLW
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | %System%\mspmsnsv.dll | ||
| 2. | hi.exe | c85c0441042b8195eff435453188a04b | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.