Backdoor:Win32/Noancooe
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 85 |
| First Seen: | October 16, 2015 |
| Last Seen: | November 6, 2020 |
| OS(es) Affected: | Windows |
As its name suggests, Backdoor:Win32/Noancooe is a backdoor trojan that is built to run on 32-bit Windows systems. Malware researchers add that Backdoor:Win32/Noancooe can run on 64-bit versions of Windows as well and uses DAT files to store its malicious code and an executable to run as a stand-alone process. The Backdoor:Win32/Noancooe trojan is similar to Papras and Tidserv and might place its code repository in the hidden system folder AppData and install its main executable in the Temp folder under the Windows directory to sidestep security scans. The Backdoor:Win32/Noancooe trojan does not replicate itself and is designed to enter a registry key in Windows to run as a startup program and allow third parties to connect to your PC every time you turn it on. The Noancooe backdoor trojan may inject code into already running processes like your Internet browser, email client and torrent client that are allowed to send and receive data over your Windows Firewall uninterrupted. That way the Backdoor:Win32/Noancooe malware can stay undetected and mask its process in the Windows Task Manager. The Backdoor:Win32/Noancooe trojan can allow its operators to delete, download, run and install files on your machine as well as spread other malware in your computer network. The Backdoor:Win32/Noancooe malware is seen to use ports 53 and 9500 to connect to its 'Command and Control' servers and receive instructions. Malware researchers note that the Backdoor:Win32/Noancooe trojan can hijack digital certificates and upload data from your computer to third-party cloud storage that is operated by cyber crooks. Needless to say, the Backdoor:Win32/Noancooe trojan should not be underestimated and installing a trusted anti-malware should be your first action to prevent data loss and further damages to your Windows system.
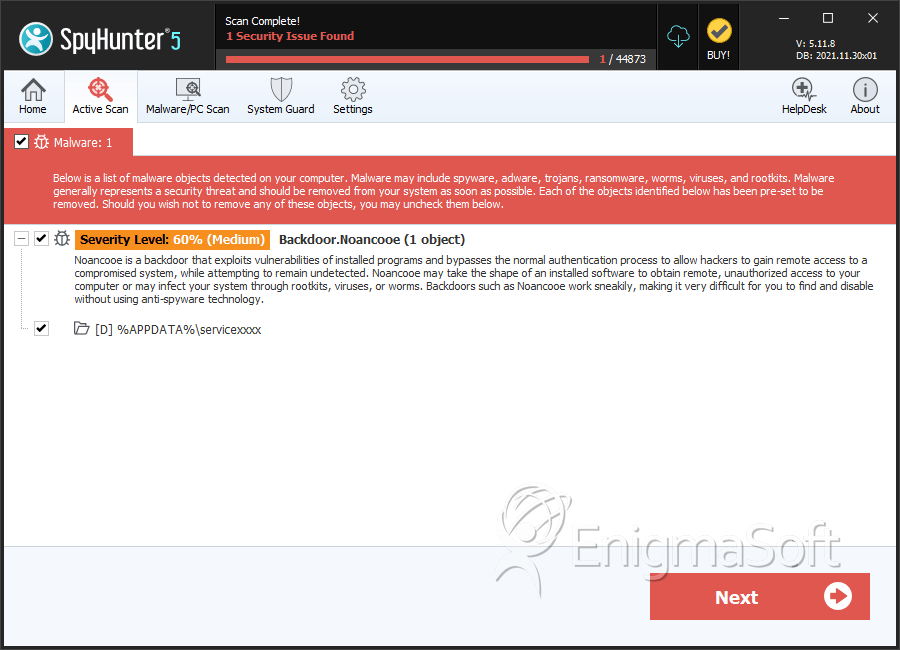
SpyHunter Detects & Remove Backdoor:Win32/Noancooe
Directories
Backdoor:Win32/Noancooe may create the following directory or directories:
| %APPDATA%\servicexxxx |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.