Backdoor: Win32/Kirts.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
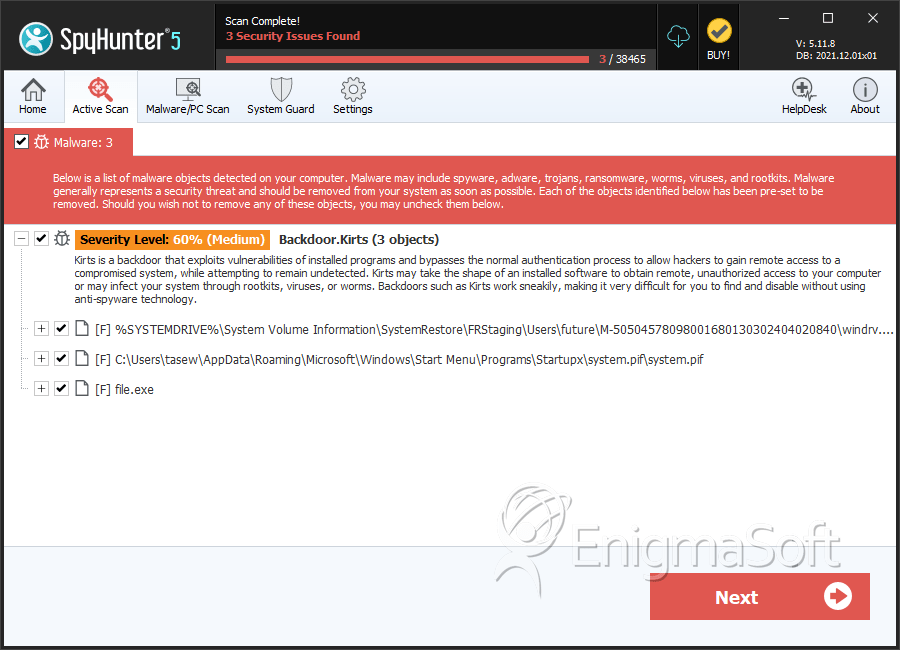
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 69 |
| First Seen: | May 5, 2016 |
| Last Seen: | November 15, 2021 |
| OS(es) Affected: | Windows |
PC users that are presented with a security alert involving the Backdoor: Win32/Kirts.A should not overlook the detection. The Backdoor: Win32/Kirts.A malware is a Backdoor-Trojan that may be used by a third-party to deploy threats on your machine and compromise the security of networks you are part of. The Kirts Backdoor-Trojan has many versions that are labeled following the model Backdoor: Win32/Kirts.[letter indicating a new version]. The Backdoor-Trojans in the Backdoor: Win32/Kirts family of threats are packed as batch files (.BAT file extension) and are loaded with a CMD script that is used to issue commands to the Windows core directly. The Backdoor: Win32/Kirts malware may be spread among users via spam mail, and you should not download and open RAR files that are attached to spam emails. The Backdoor: Win32/Kirts.A malware is designed to connect to remote servers and download CAB files with additional binary and instructions.
The Backdoor: Win32/Kirts.A malware may open ports on your system to enable its operations, and network administrators may wish to make sure that their firewall is filtering all connections. The Kirts Backdoor-Trojan may use ports 80, 23, 119, 411,412, 591 and 6881 to download malware and allow remote access to your system. The Kirts cyber threat may install a corrupted digital certificate on your OS to bypass code signing policies and modify your file system without raising alarms. The Kirts Backdoor-Trojan may use the files puwuladrur.bat, authrootstl.cab and mscoree.dll to support its activity and run from the Temp directory on the Windows partition. The Kirts Backdoor-Trojan utilizes code injection to hide its operations and is hard to detect with basic run-time analysis. Security analysts note that the variants of Backdoor: Win32/Kirts may be identified as Gen:Variant.Zusy.189561, MSIL/Injector.OZF and Trojan.Win32.IRCbot.aanp. A trusted anti-malware suite can clean computers that are infected with the Backdoor: Win32/Kirts malware and prevent unauthorized access.
SpyHunter Detects & Remove Backdoor: Win32/Kirts.A
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | windrv.exe | 28d296c7d96eb576fc91efd3e98d284c | 40 |
| 2. | system.pif | 7219807ecbd2eed997ad4873dbd2bef8 | 9 |
| 3. | file.exe | d1f2ef4fb056ec1ab0a8c6a4b3cd5055 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.