Backdoor:Win32/Htbot.C
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 31 |
| First Seen: | January 13, 2016 |
| Last Seen: | January 20, 2019 |
| OS(es) Affected: | Windows |
The Backdoor:Win32/Htbot.C malware is a Backdoor Trojan that is involved in spear phishing attacks and might appear as a module for the SQLite platform to managing databases. The Backdoor:Win32/Htbot.C malware is designed to exploit the Network Location Awareness service of Windows to recognize connected devices and provide its operators with detailed information about the infected computer. The Win32/Htbot.C Backdoor Trojan can run on 32-bit and 64-bit architectures and allow remote code execution on Windows XP, Vista, 7, 8 and 10. The Backdoor:Win32/Htbot.C malware is similar to other Backdoor Trojans like 0Access and Unskal and might disable components of the Windows Firewall to enable its operations. The Win32/Htbot.C Backdoor Trojan might use a corrupted file named svchostcenter. exe to establish an Internet connection to its 'Command and Control' server and receive instructions.
The Backdoor:Win32/Htbot.C malware is known to use UDP port 53 to receive commands and experienced network administrators may recognize suspicious Internet traffic via UDP port 53. Additionally, the Win32/Htbot.C malware may execute the Shellcode and allow its handlers to exploit vulnerabilities in applications that the infected user has installed. Victims of Backdoor:Win32/Htbot.C may be targeted with ransomware like CyberLocker and KRIPTOVOR that are favored by many. The Backdoor:Win32/Htbot.C malware may place its files in the LocalAppData folder and write a registry entry in Windows to be executed every time you turn on your PC. Files like winsmss.exe and winlogon-svc.exe may be used by Backdoor:Win32/Htbot.C to maintain its functionality and allow third parties to manipulate your files and system settings. Therefore, you should install a renowned anti-malware shield to prevent remote access to your OS and delete the binary associated with Backdoor:Win32/Htbot.C.
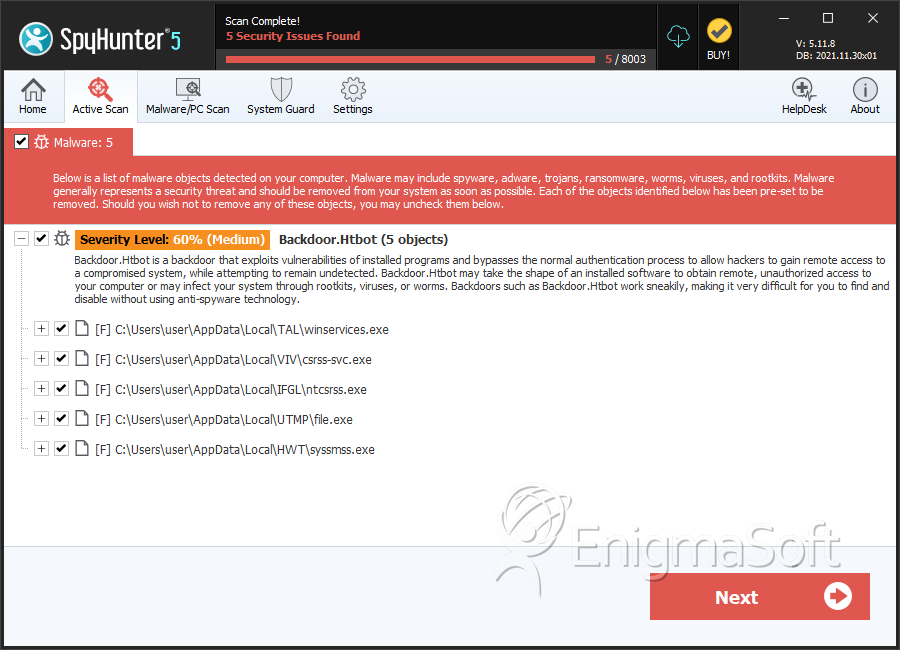
SpyHunter Detects & Remove Backdoor:Win32/Htbot.C
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | cb32390630702f15390054188e6a74c4 | 9 |
| 2. | winservices.exe | f119da0710d065129503a4769e91c038 | 1 |
| 3. | csrss-svc.exe | adb71c6295691df7d46fa0c16a22e10e | 1 |
| 4. | ntcsrss.exe | 6dda76bbee2758db5e5b92f619a9bf34 | 1 |
| 5. | file.exe | 64b2457c7474fa3fc4cadb0e5cded4ce | 1 |
| 6. | syssmss.exe | 2154ffef4fb8f077eff54d19e12db0b9 | 1 |
| 7. | file.exe | f9684678fc5fcb2c6d9bdc29029d068a | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.