Backdoor.Win32.Agent.aksn
Table of Contents
Backdoor.Win32.Agent.aksn and Email Phishing Scams
The Backdoor.Win32.Agent.aksn Trojan is associated with Troj/Inject-QL, a malware duo that can give a hacker unauthorized access to its victim's computer. Backdoor.Win32.Agent.aksn made headlines in fall of 2011 when Backdoor.Win32.Agent.aksn was used in a series of email phishing scams aimed at certain important companies. In an ironic twist, a malicious email associated with Backdoor.Win32.Agent.aksn will try to convince its victims that it has been sent by the IT department of the company in question. This message will claim that a malware infection has been detected and that, consequently, some data may have been lost or stolen. The message's subject will be 'IT Notice' and it will go into detail about a virus infection that has erased certain files and infected some computers in the affected company. ESG security researchers strongly recommend ignoring this email, as it is designed to infect its receiver with the Backdoor.Win32.Agent.aksn Trojan.
How this Fake IT Notice Links to Backdoor.Win32.Agent.aksn
This fake IT notice contains an embedded link that is supposedly meant to take the victim to an anti-malware program to stop the imaginary virus from attacking. This link is quite believable because the criminals behind this scam have found ways to disguise it so that it will appear to come from the company under attack. In fact, this link reroutes the victim to an attack website containing Backdoor.Win32.Agent.aksn and its dastardly partner in crime Trojan.Inject.ql. According to ESG security researchers, the link embedded in the email appears to take the victim to an executable file simply titled as 'antivirus' with a .exe extension which appears to reside on the company's server. Actually, this link goes through another malicious website. The aforementioned malicious link will usually look something like this: www.companyname.com/download/antivirus.exe which, while superficially convincing, is actually a link to a known attack website.
Distinguishing the Backdoor.Win32.Agent.aksn Email from the Real Thing
In a state of panic about a possible loss of data and malware infection, a computer user may become inattentive, missing details in the email that point to its true source. Simply taking the time to read the text carefully will reveal poor English, bad grammar and spelling and unnatural-sounding language. Remember, most Trojan infections will have a social engineering aspect, a facet which takes advantage of human nature. To avoid becoming a victim of Backdoor.Win32.Agent.aksn, ESG security researchers recommend contacting the supposed source of any email before clicking on unexpected email attachments.
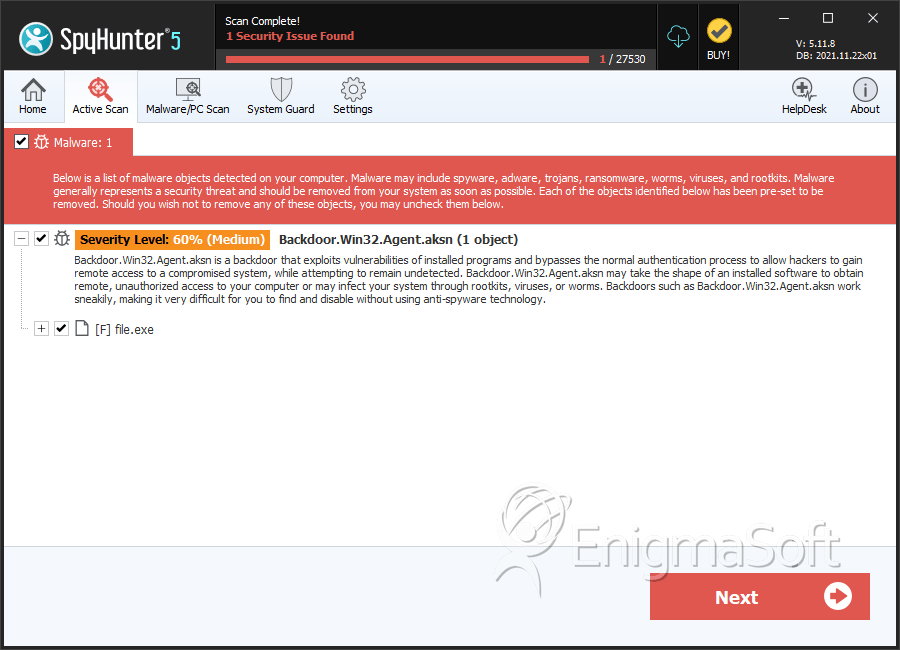
SpyHunter Detects & Remove Backdoor.Win32.Agent.aksn
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 590205e14bcc536da286eb3537cff392 | 0 |
| 2. | file.exe | d11a307b899d58d96903df4783e01b30 | 0 |

