Backdoor.Infexor
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
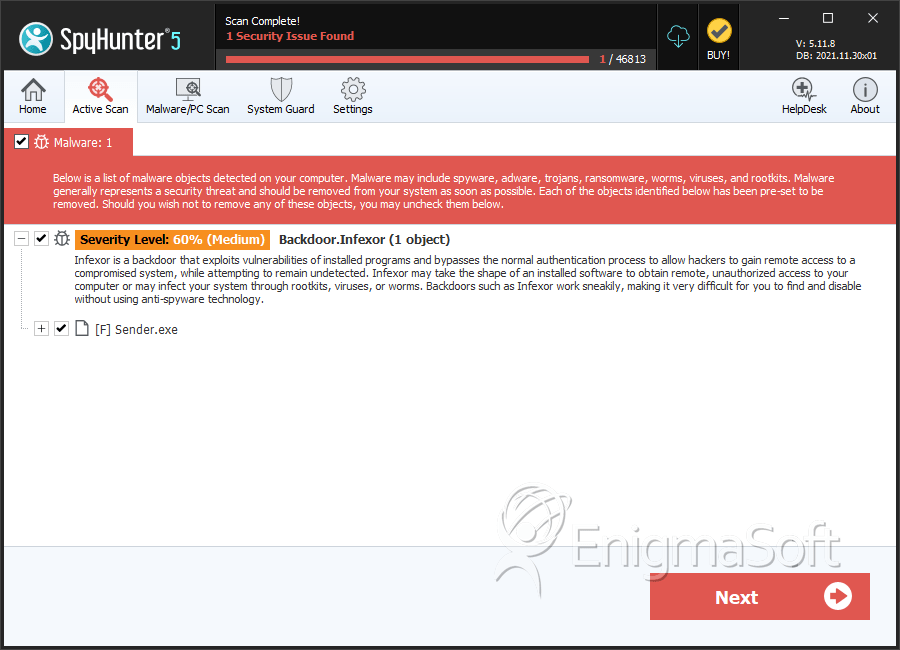
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 35 |
| First Seen: | December 1, 2009 |
| Last Seen: | July 12, 2020 |
| OS(es) Affected: | Windows |
Backdoor.Infexor is a name associated with a backdoor Trojan that was first spotted in March 2013. AV developers have been tracking the development of Backdoor.Infexor for five years at the time of writing. The Backdoor.Infexor Trojan may infiltrate systems when users visit compromised Web pages and click on corrupted advertisements. The cyber-threat at hand is configured to run a hidden instance of the Internet Explorer in the background and communicate with 'Command and Control' servers via port 8080. The malware can download files and inject code into already running legitimate processes. We have seen the Backdoor.Infexor Trojan connect to the hxxp://tanatossite.narod[.]ru address and obtain instructions on what to do.
Threat actors can use Backdoor.Infexor to stop programs, open network ports, delete and upload files from infected machines. The Backdoor.Infexor malware can run on the latest Windows versions, and it may create hidden folders under the ProgramData directory on the primary system drive. Researchers have noticed that Backdoor.Infexor can corrupt the Windows internal tools like wowexec.exe, ie4uinit.exe, sysocmgr.exe, ntbackup.exe, ctfmon.exe defrag.exe, savedump.exe and gpresult.exe to facilitate its operations. Regular PC users may not notice the activity of Backdoor.Infexor and you should run a reliable anti-malware suite to make sure there are defenses in place for threats like Backdoor.Infexor.
Detection names used by AVs for Backdoor.Infex
BDS/Agent.glnya
BackDoor.Generic14.CLCY
Backdoor.Infexor!Hmt22WUXgB8
Backdoor/Win32.Infexor.gen
TROJ_GEN.R1DC1II
Trojan.Generic.5048032
Trojan.Generic.5048032 (B)
Virus.Win32.Asim.c (v)
Win32.Suspicious.H
Worm/Win32.IRCBot
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Symantec | Trojan Horse |
| Sophos | Mal/Generic-A |
| Panda | Trj/CI.A |
| NOD32 | Win32/Infexor.C |
| McAfee-GW-Edition | Heuristic.BehavesLike.Win32.Backdoor.M |
| McAfee | Generic BackDoor!bav |
| K7AntiVirus | Backdoor.Win32.Infexor.cy |
| Ikarus | Virus.Win32.Misa |
| Fortinet | W32/Infexor.CY!tr.bdr |
| DrWeb | Trojan.Click.27555 |
| Comodo | Heur.Suspicious |
| CAT-QuickHeal | Backdoor.Infexor.cy |
| BitDefender | Trojan.Generic.2580433 |
| AVG | BackDoor.Generic11.AMWX |
| Avast | Win32:Trojan-gen |
SpyHunter Detects & Remove Backdoor.Infexor
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | Sender.exe | 12da5935b5c01e157f648273b839965d | 0 |

