Backdoor.Hupigon.ise
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 4 |
| First Seen: | July 24, 2009 |
| Last Seen: | January 10, 2022 |
| OS(es) Affected: | Windows |
Backdoor.Hupigon.ise is a nasty Trojan classified as backdoor. Backdoor.Hupigon.ise usually spreads through browser security holes and via spam email attachments. Once executed, Backdoor.Hupigon.ise gives an attacker full, unfettered access to your computer and any data stored on it. The intruder then may download, upload and run random files, control your computer and retrieve user sensitive information, including financial data as well. Backdoor.Hupigon.ise has the ability to download and install other spyware. Backdoor.Hupigon.ise is configured to run on every Windows startup automatically. We recommend to get rid of Backdoor.Hupigon.ise as soon as it has been detected.
SpyHunter Detects & Remove Backdoor.Hupigon.ise
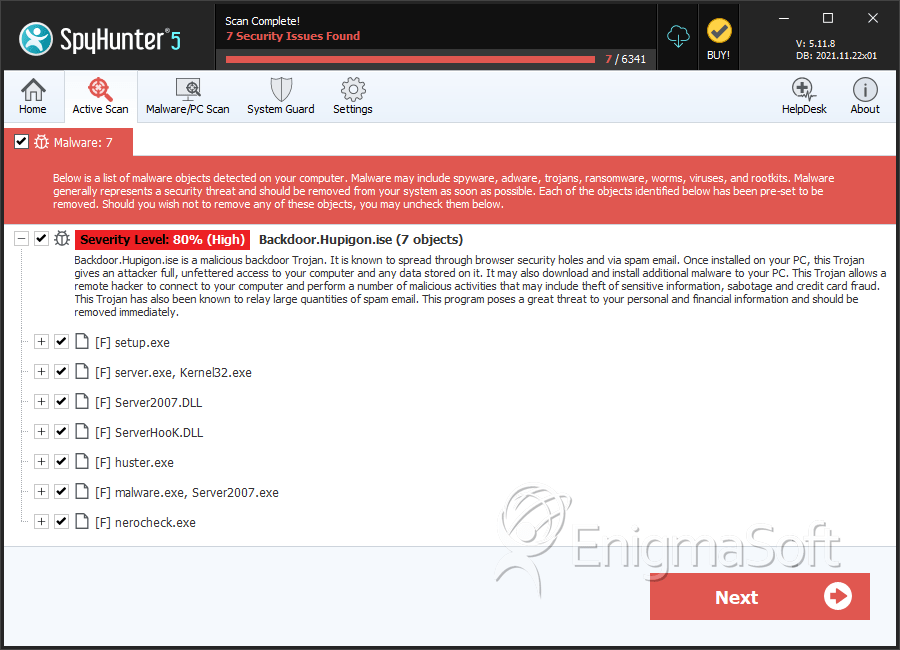
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | malware.exe | 55bc32b94e1c5944b0837236fbff6306 | 2 |
| 2. | setup.exe | 7298fa36a8ca4dffa1b901fc126040b9 | 0 |
| 3. | server.exe, Kernel32.exe | f885e2a5fa5b98933ca6e8ce226f3ec7 | 0 |
| 4. | Server2007.DLL | 2b48b0f4869b61aab7013008a9a65b6f | 0 |
| 5. | ServerHooK.DLL | 345cd8d847a4f0e9b38ab57679a52eb7 | 0 |
| 6. | huster.exe | 674a8703bc27f9e2bf74424aa908f040 | 0 |
| 7. | malware.exe, Server2007.exe | 07ec3a35ca4f009dd73216099d458d1c | 0 |
| 8. | nerocheck.exe | d8163e5ee365262c9402a543ef413909 | 0 |

