Backdoor.Briewots.A
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
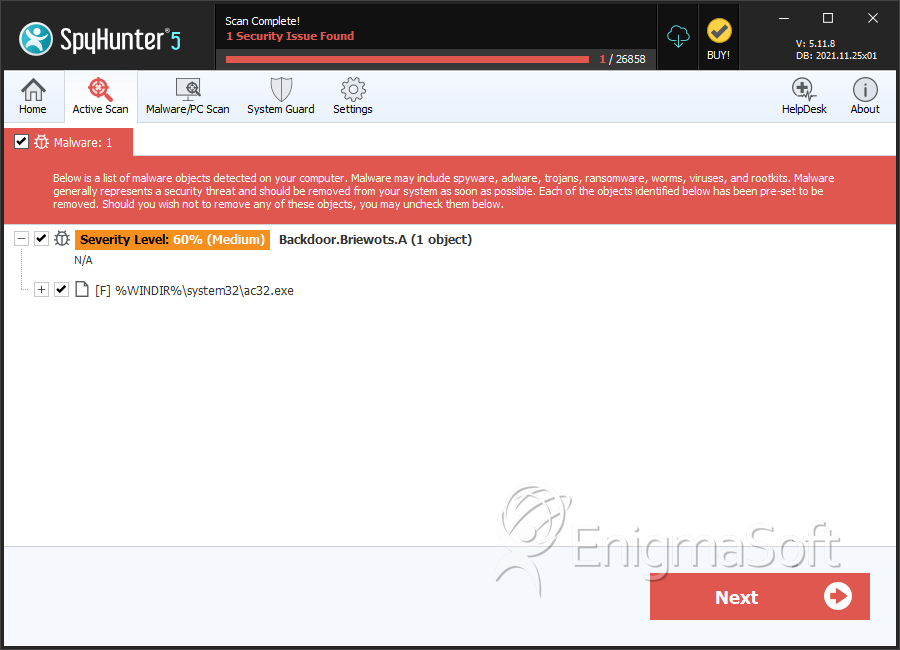
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 15 |
| First Seen: | July 4, 2011 |
| Last Seen: | December 25, 2020 |
| OS(es) Affected: | Windows |
Backdoor.Briewots.A is the detection for a malicious program and Trojan stalking PC users to open a backdoor and give a hacker remote access. Although its primary goal is to open a backdoor, chances are you unknowingly let Backdoor.Briewots.A inside the front door. Trojans use guises that fool PC users and get them to click blindly on infectious links and attachments. Trojans can also be grouped along with other malware and hidden in the download of freeware.
In addition to opening a backdoor, the Trojan will also carry out other malicious activity, such as opening a port and reporting its findings. A survey of the system will reveal system data that is vulnerable and can help plan future attacks. Vital data will be stolen out of the browser cache and email addresses off the hard drive. A connection to a remote server could serve up more malicious programs, including a rogue security program. Instead of awaiting the Blue Screen of Death due to draining and overload of system resources, the PC user should aggressively find and remove malware, including Backdoor.Briewots.A.
Some malicious programs use a rootkit to mask file names so they appear the same as legitimate OS files and confuse those seeking to remove them. Deleting wrong files could corrupt your system and you might lose valuable data. What is recommended is the use of a stealth anti-malware program to sort out the confusion and permanently erase all malware hidden on your system. Additionally, a stealth anti-malware program can better guard your system going forth.
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Panda | Trj/CI.A |
| AVG | BackDoor.VB.MAJ |
| Fortinet | W32/VB.NVF!tr.bdr |
| Ikarus | Trojan-Downloader.Win32.VB |
| AhnLab-V3 | Backdoor/Win32.VB |
| Antiy-AVL | Backdoor/Win32.VB.gen |
| McAfee-GW-Edition | Heuristic.BehavesLike.Win32.Downloader.A |
| AntiVir | BDS/Briewots.A.1 |
| DrWeb | Trojan.Click1.59522 |
| BitDefender | Backdoor.Generic.681828 |
| Kaspersky | Backdoor.Win32.VB.nvf |
| Avast | Win32:Malware-gen |
| NOD32 | a variant of Win32/TrojanClicker.VB.NJT |
| K7AntiVirus | Backdoor |
| McAfee | Generic BackDoor!dly |
SpyHunter Detects & Remove Backdoor.Briewots.A
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | ac32.exe | ffb81a1afef298fec167cab7d6724950 | 9 |
| 2. | ac32.exe | 0454448cf743acd55ca3883de84f6ede | 2 |
| 3. | ac32.exe | 55923460fa3f73a123deb0299499b8fc | 2 |
| 4. | ac32.exe | 4255e902898eedba5427cb91056a0b65 | 1 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.