BackDoor.Andromeda
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 60 % (Medium) |
| Infected Computers: | 3,390 |
| First Seen: | May 24, 2012 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
BackDoor.Andromeda Image
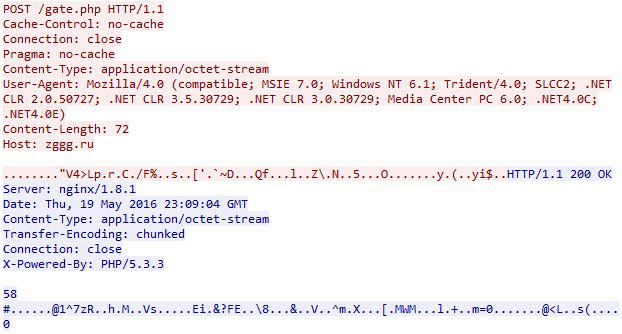
ESG security analysts have been informed about numerous Trojan attacks centered primarily in Central and Eastern Europe involving Backdoor.Andromeda. Like most backdoor Trojans, Backdoor.Andromeda is only the first in a multi-component malware attack designed to wreak havoc on a victim's computer system. However, although Backdoor.Andromeda's primary purpose is to open a back door into the victim's computer system, this malware infection also has spyware capabilities, the ability to get into to an alien server and to download and set up other malware, as well as the ability to relay information to a remote attacker.
Most infections with Backdoor.Andromeda are acquired from malicious email attachments, although this malware infection may also invade a computer system as a result of an attack website exploiting known vulnerabilities in the victim's computer system. ESG malware researchers consider that Backdoor.Andromeda is a severe threat to a computer's security. Because of this, it is extremely important to delete Backdoor.Andromeda immediately with a reliable anti-malware application and to ensure that other malware has not managed to infect the victim's computer system due to Backdoor.Andromeda's backdoor.
Table of Contents
Backdoor.Andromeda Enables other Dangerous Trojan Attacks
The main purpose of Backdoor.Andromeda is to create a backdoor into the infected computer system. 'Backdoor' simply refers to an unauthorized opening in the infected computer's security. By using this opening, a criminal can connect to the infected computer and install other malware or take out sensitive information, much like an unguarded back door can allow a robber to sneak into a building. Backdoor.Andromeda has been involved in various other malware attacks that can be installed on the victim's computer thanks to Backdoor.Andromeda's backdoor. There's a bundle of Trojans that are often installed by using this unauthorized security breach. Among these Trojans, ESG malware researchers have identified a spam bot, that is, a Trojan designed to take over the infected computer's email client in order to send out spam email; an IRC bot, which is a malware infection that enables criminals to take over the infected computer system by sending it commands via IRC; and a browser hijacker, a Trojan that changes the infected computer's HOSTS file in order to redirect its online activities.
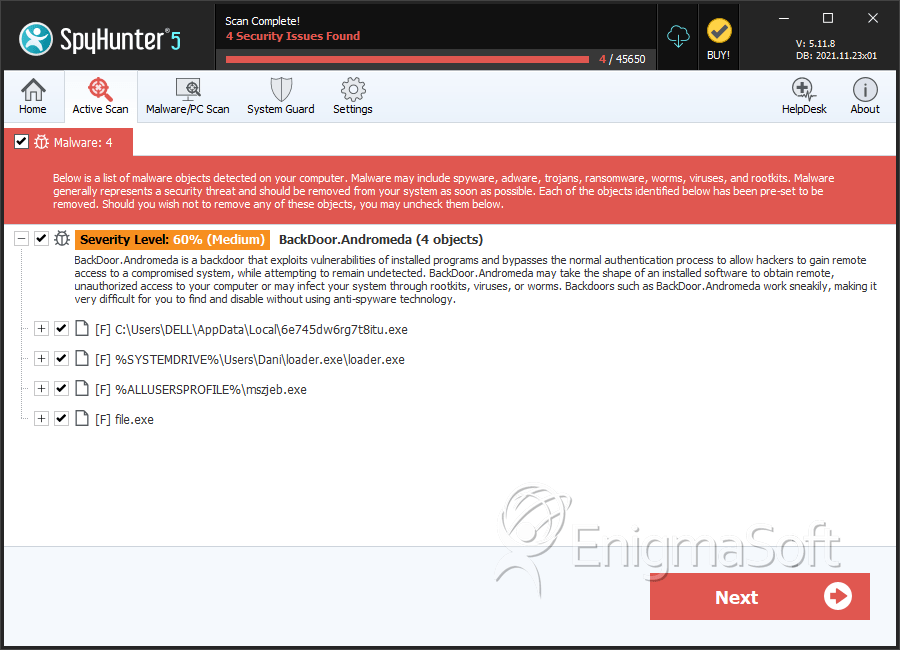
SpyHunter Detects & Remove BackDoor.Andromeda
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | 6e745dw6rg7t8itu.exe | bc90c938bc1170444a691cdc04ec733e | 3,361 |
| 2. | loader.exe | 40c0c45bd9741ef0f9d2ff972d0b8d75 | 19 |
| 3. | mszjeb.exe | 0e9c6292025426164fc32f2413a84846 | 3 |
| 4. | file.exe | f7d45793226820996c9b3642f644bebb | 0 |
