Appround.net
Appround.net Image
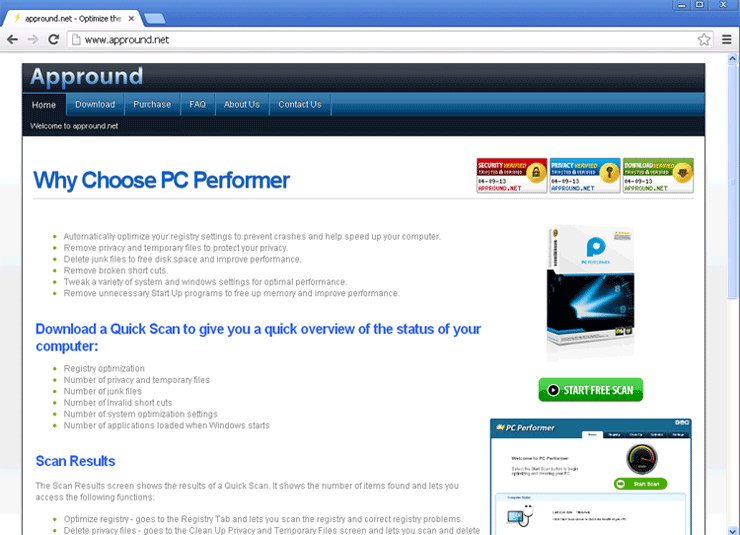
Appround.net is used to distribute a defragmenter known as PC Performer. There have been reports of Web browser redirects to the Appround.net website, often occurring after the computer user is led to a search engine displaying sponsored search results. Appround.net will appear as a pop-up window in the case of browser hijacker infections, often opening in a new tab in the infected computer's Web browser. If the Appround.net website is appearing on your Web browser as a pop-up window, it is highly likely that your computer has become infected with a browser hijacker, often referred to colloquially as the 'Google Redirect Virus'. ESG malware analysts advise using a reliable anti-malware tool to analyze your machine and remove any browser hijackers responsible for Appround.net pop-ups.
The main problem with Appround.net is that the program it distributes, PC Performer. These kinds of defragmenters offer to boost the performance of a computer. In fact, they do the opposite, weighing down the victim's PC with unwanted software and deliberately causing problems on the infected computer. They harass the computer user with a number of error messages and alarming notifications, all meant to scare inexperienced computer users into thinking that there are severe problems with their computer. The goal of these kinds of programs is to persuade PC users that it is necessary to upgrade to a 'full version' of the defragmenter.
The main cause of Appround.net pop-ups are browser hijackers, usually in the form or a Web browser toolbar. Because of this, it is important to remove any Web browser extensions or toolbars that may have been installed recently. Once this has been done, it will be essential to revert the affected computer's settings (especially Web browser preferences) to their defaults, since these browser hijackers tend to make unwanted changes. Finally, ESG security researchers strongly advise getting the assistance of a renowned anti-malware solution to scan the infected machine in order to ensure that the browser hijacker has not exposed the victim to additional, more dangerous malware.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.