Altrusica application
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 186 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 8,944 |
| First Seen: | July 28, 2025 |
| Last Seen: | May 23, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
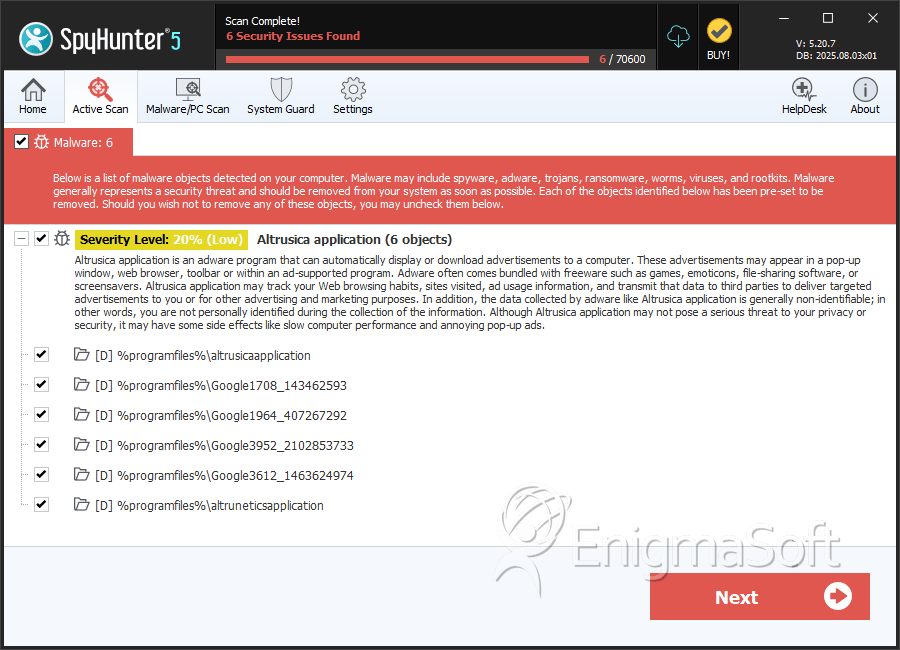
SpyHunter Detects & Remove Altrusica application
Registry Details
Directories
Altrusica application may create the following directory or directories:
| %allusersprofile%\Altisik |
| %localappdata%\Altruistics |
| %programfiles%\AlmaruricsApplication |
| %programfiles%\AlrosticsaApplication |
| %programfiles%\AltburicsApplication |
| %programfiles%\AltisikApplication |
| %programfiles%\AltsuricsApplication |
| %programfiles%\Google1708_143462593 |
| %programfiles%\Google1964_407267292 |
| %programfiles%\Google3612_1463624974 |
| %programfiles%\Google3952_2102853733 |
| %programfiles%\altruneticsapplication |
| %programfiles%\altrusicaapplication |
Analysis Report
General information
| Family Name: | Altrusica application |
|---|---|
| Signature status: | Self Signed |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
eba026c67052c26ec3b2be68f8e6f8e0
SHA1:
ee59b39ae162b9c9be63574b1c4c480b48afbc18
File Size:
1.65 MB, 1653832 bytes
|
|
MD5:
a8dbf4f4093e8fdb33869c68d3645c4e
SHA1:
816869512df5ed8acdf503e17b8b87e4838f78c8
SHA256:
4304BCB8C7C20DC6E747B26779BC3C128819FB8A3745CC9E762E1B91DD73EB18
File Size:
6.66 MB, 6659160 bytes
|
|
MD5:
bb9b939b63799fecffd1eb78deb88c94
SHA1:
fd8120d35d3541145fa794986d3ab8e27ffc28b2
SHA256:
FC557E15FFD82684867AB207B9528231719A4C04F0D65F25B754E2BB1B3CF29D
File Size:
251.48 KB, 251480 bytes
|
|
MD5:
73ab998b58804620c732f00fc74bfc70
SHA1:
e24f533263cb8cfdd785b841fd975bcca302f16f
SHA256:
DDD1C2DFFD9979DD66936C080C5D82657F76BEC11D39B051DA0C3A22916AA0A6
File Size:
3.85 MB, 3846232 bytes
|
|
MD5:
554dbcb8128e1b017e1f5743177ebf47
SHA1:
6598383602d50f823550515c706d6c2634627fd9
SHA256:
A90F253C15FF29EBB747815C1BCFCDC28DF19E855ACB345FFD1F669A9AD19B9C
File Size:
1.65 MB, 1653848 bytes
|
Show More
|
MD5:
8d32fa79d39fa4eb51d11c586f15c064
SHA1:
9c3dca69e7fdaada905a759f666ed3b315f13146
SHA256:
72E0A328751A9A7217047C2FD94398D3BF255A3A657F0A26F9438520614A29FC
File Size:
2.32 MB, 2320984 bytes
|
|
MD5:
6300fca640b7025c560cdbc68be2d496
SHA1:
a6611caf1c1c4d1dd98105cd43858599f60ea658
SHA256:
6B6BE36242B1F1C1850AEEFC8FA96A0044CEDD0ECF58316967555D9FB90B0587
File Size:
4.16 MB, 4163160 bytes
|
|
MD5:
807a6df8de4a43dafe0991fd890321ef
SHA1:
abb2ea571f2205e4b25deacc6881a333c2de82ae
SHA256:
B925CBBF186ABDF7D3FDD8579DEEBB9C169BF5179E716A0F806E2C40797329CE
File Size:
927.74 KB, 927744 bytes
|
|
MD5:
cb5c054bbc75627f50013acd14d1f54e
SHA1:
d1d24b6fcbb6dc2efebe419687aea9341501c825
SHA256:
E2E5407D7EFCC2E547301F1D2735699A7E6EA813FBB2E3DF0AC6D5CD3F30124E
File Size:
1.65 MB, 1653848 bytes
|
|
MD5:
1160f77a59dff7a44b55bfa86b1b1d5a
SHA1:
19294c325c85f62122bea52b2a4be93d6c168a5d
SHA256:
0123F8FB26AB932F1F352479599DFEF3E893D7B62B9700DAC5205681794FD888
File Size:
1.65 MB, 1653848 bytes
|
|
MD5:
fc9b2dd89d3108437541fb141b6f2fc9
SHA1:
bd6c71f5efd781ab6c38364e129807d03208d1a8
SHA256:
58A9A880797167EC2B6A66B211FCD2C1F45A45209A6A32689D8DBEBE00793DE8
File Size:
1.65 MB, 1653848 bytes
|
|
MD5:
b84d96f0c11d9dd6129cb31cdf2dcb3a
SHA1:
cd4018f36135b25889cb33804c6c38aeb4c66447
SHA256:
D7DE437E382982D2F88EF1AB94EA72336D48E47D3BCD6D96550639DCFFD13EF1
File Size:
3.37 MB, 3370584 bytes
|
|
MD5:
d9579cbc6d6a7017617655d0688ca257
SHA1:
abf669c315b7ae3fff687cf51d64170719c03b25
SHA256:
85045F062CB6B3B7E55A12E74DB464681D8B452C94231D26B24B5B4C88394E07
File Size:
2.31 MB, 2314328 bytes
|
|
MD5:
5a74b48dfb892a12e8fb2585c0f03bb6
SHA1:
164f9b9001f50beaa7ac2514f64ac83f042e815a
SHA256:
B81BAE64AAF38C1391F25AA75A8BE2AD90643FC443F4DF22712EF94E8F47BEAF
File Size:
928.26 KB, 928256 bytes
|
|
MD5:
f59a45b7a79c337f914d5c425e918e83
SHA1:
f48657bb4fa59cea161b12a5cc3ef9a9c62b968e
SHA256:
24EA27EB1E2D888C9C937EF770C106EF69A43BA9A717E515588E1146EBC470ED
File Size:
1.65 MB, 1653848 bytes
|
|
MD5:
4589994e46ab75256cf7d98357561e9b
SHA1:
f47ee5db4663f3de8f6ee680c69a37b611a7fcb2
SHA256:
A362D60022057C9FEED1BA88CCEC93B81A7A36C21F3749AC0C63447AF8BC1DB8
File Size:
3.33 MB, 3329112 bytes
|
|
MD5:
01c174d18741a27c90c388d8de84a26b
SHA1:
b24f07c375ad74cbf662cc49315af1bc3260055e
SHA256:
F1BDB4BD11FDCA4459BE9BFAE80B301F281F5B3E8BAB79CC1151B03EAA91E536
File Size:
2.31 MB, 2314328 bytes
|
|
MD5:
c677cc8b5c2a46c7dc58cbb5ae0b8575
SHA1:
b7199de47b7ec60b1da49abf37dc1204db399ffd
SHA256:
1595AE1C4A579339AE800AC419492DFB65E18433903A4901D611E22165915ECE
File Size:
1.65 MB, 1653848 bytes
|
|
MD5:
1abf02f1ceb647ddc64b4183eb788666
SHA1:
895dd9c7adf5f14412df51fa5f34f3976a5b1d9c
SHA256:
C18320833D69A177FE683326E29F48F523349841F73530A25256FF9EF8584515
File Size:
941.06 KB, 941056 bytes
|
|
MD5:
b038f096cc08dae87361f23093ee8362
SHA1:
5d22d2d81c5b0f6c5ef5042bf722afc0315b0b97
SHA256:
DF71A5A573DC65C3442A1B268E381EA212D1B003D6F3BFAE05C1726B50562FF3
File Size:
1.65 MB, 1653848 bytes
|
|
MD5:
c4dcad331454cd7e1350c20327c31068
SHA1:
16216eda8a093cfea277976b944de49dd08c1373
SHA256:
38026A7B87D94DEB6BCF95802739A0BE7C37025923AA5CF52E0E3AAF332DA9AE
File Size:
928.26 KB, 928256 bytes
|
|
MD5:
cef0dd9dffa0ca423d3790d31d9cf203
SHA1:
88d4357edc5c9230d24c6e6841a30599811d0545
SHA256:
D7A1EBE635CCA1E414DE019BA32436B1840AAF166978F5B16B292FB764E3556B
File Size:
928.26 KB, 928256 bytes
|
|
MD5:
fc8a1d058d7a7d46df8e12613ff1b673
SHA1:
4cdb9f8f9b9c8322144567f6a000b31b17e7dd42
SHA256:
E7395A099234952C8CF6435E7A76497FE08AC1BE6DD7BE3EC937D0683BC8A502
File Size:
941.06 KB, 941056 bytes
|
|
MD5:
3eaa1a9da601fccf2cdbc44d3092946a
SHA1:
7e37fa40ca9483a09ed8dea3ca7e74d9ce572b9e
SHA256:
848E69B5044E25B217E1C5AA6AE723CAB04A0C04DAEF198E749788810D16C07E
File Size:
1.66 MB, 1660688 bytes
|
|
MD5:
c547c0de8b2ad731817f3e825d6d39e3
SHA1:
8e844e5da78f9f6cdc0e11ead4633e268d7fc94d
SHA256:
937A16C8B760948408EE073485F5F56CA1FE1085513C50FB87C636155C2A721F
File Size:
941.06 KB, 941056 bytes
|
|
MD5:
289345b90f4b2cd9d52155e7e12a9f29
SHA1:
d433414232c98540774d2aa5f852e0449823dc0d
SHA256:
59EE0BC7FD3D6208D9D0B1C4F71A1FE3A8DAEBF258FF1DE2BFA4886613FD1CCF
File Size:
1.66 MB, 1660688 bytes
|
|
MD5:
521078c6707ae5b4254f0d70c6a562a0
SHA1:
b7857d4c29214d74a2354531cec17070a315ccb1
SHA256:
3E46008A31422A3678E860A0F6B6E5B2C0A12588A86303E528FAD4DB87A26C09
File Size:
3.08 MB, 3076608 bytes
|
|
MD5:
79da2031d4d9568152d97e4a438bce80
SHA1:
2c90251aa7e35104eff4a068446c0dc3c7d2ba33
SHA256:
FB6C33D613C26CEAC03D996CADE0389B366BDA12AF6FAF72F190558A0781AF6D
File Size:
1.66 MB, 1660688 bytes
|
|
MD5:
27cfbefad9734726f8c57357a60ae9b1
SHA1:
7af8c3a358ee0d1e117e1424cd1aeb4abe14e9b9
SHA256:
728A9238240C92FF084857E26A4DA70FF29F4BACFEB5AA966E3A304D9AED1318
File Size:
941.06 KB, 941056 bytes
|
|
MD5:
1cae62757f3b13c09a0958f1e47387ed
SHA1:
2e43b25bdf1da9f394158b0f005b99b3fb0c19c0
SHA256:
18A05CADA2D731BBC99648047A812B47344EB5F2D4282CB1D4B21A06EE3E98B5
File Size:
1.66 MB, 1660664 bytes
|
|
MD5:
a05d3ff9484dd6e61ae184f6f73a43c1
SHA1:
37d315106d3fc06a1fb878353f2bc6c860d75567
SHA256:
1F7DCCDEA570457F48032D3DA97F7278C3053E61FD6EBCC0956E065EE60B634B
File Size:
941.06 KB, 941056 bytes
|
|
MD5:
e07878da363c6b636b0c2a9e71467356
SHA1:
8f4d80fdebc42fc438f4a275b746c550c9d38f04
SHA256:
3E9C56C57790E6FD1FB1DC2ADB7160EE50841C50CC4517928E9B807295F749AC
File Size:
941.06 KB, 941056 bytes
|
|
MD5:
b502ab30ebe005094631df1bbac4ef9f
SHA1:
919f994d80a7ca1049d84636d9df9d59ba45ba2f
SHA256:
98F055B07C1BE6D393C86A119D74F83D09E622A426D18792238F796EEE398D35
File Size:
927.74 KB, 927744 bytes
|
|
MD5:
2ded23897adf16f741aa04162975e52e
SHA1:
da42d36d86ea47202694181a1aceace056f2a238
SHA256:
8E4DCEC84702E1ABB9BD5138820497C5531A6B113AF44EB6711AAF1A9C803C60
File Size:
941.06 KB, 941056 bytes
|
|
MD5:
a623519ec2ed6daf04ada01a6ad12db0
SHA1:
0af6d959f3ad541dffc3dc0c1d4ab335166d4707
SHA256:
C6A44988E8AEC422F1509C48D746FCD0AD1B1CD1AF86BE80DDBB242CD33143C7
File Size:
928.26 KB, 928256 bytes
|
|
MD5:
7a15b465baa62dc99cf2605e3bc2a109
SHA1:
5c9aa04f29ae02454159deeb430dce557ba54acd
SHA256:
6AF596C18536FDCBE6168F3154A1F85E6ECB4EB3D099662425BFEEEA17AB14D9
File Size:
927.74 KB, 927744 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has exports table
- File has TLS information
- File is .NET application
- File is 32-bit executable
- File is 64-bit executable
Show More
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version |
|
| Comments |
|
| File Description |
Show More
|
| File Version |
Show More
|
| Internal Name |
Show More
|
| Legal Copyright | AltisikSoftware |
| Original Filename |
|
| Product Name |
|
| Product Version |
Show More
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Turn Urge | Affair Will | Hash Mismatch |
| Turn Urge | Affair Will | Self Signed |
| Whereas Attorney | Dazzle Cushion | Hash Mismatch |
| FutDevSigner | FutDevSigner | Hash Mismatch |
| FutDevSigner | FutDevSigner | Self Signed |
Show More
| FutMiaSigner | FutMiaSigner | Hash Mismatch |
| FutMiaSigner | FutMiaSigner | Self Signed |
| PelmoDevGroup | PelmoDevGroup | Self Signed |
| Footprint Merit | Wallpaper Mug | Self Signed |
File Traits
- 2+ executable sections
- dll
- Inno
- InnoSetup Installer
- Installer Manifest
- Installer Version
- VirtualQueryEx
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,898 |
|---|---|
| Potentially Malicious Blocks: | 16 |
| Whitelisted Blocks: | 2,488 |
| Unknown Blocks: | 394 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- AltrusicaApplication.A
- Injector.AK
- Lumma.GFD
- Rugmi.IA
- Sheloader.A
Show More
- Sheloader.C
- Stealer.KF
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
31 additional items are not displayed above. |
| User Data Access |
|
| Encryption Used |
|
| Anti Debug |
|
| Process Shell Execute |
|
| Process Manipulation Evasion |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\abb2ea571f2205e4b25deacc6881a333c2de82ae_0000927744.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\164f9b9001f50beaa7ac2514f64ac83f042e815a_0000928256.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\895dd9c7adf5f14412df51fa5f34f3976a5b1d9c_0000941056.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\16216eda8a093cfea277976b944de49dd08c1373_0000928256.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\88d4357edc5c9230d24c6e6841a30599811d0545_0000928256.,LiQMAxHB
|
Show More
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\4cdb9f8f9b9c8322144567f6a000b31b17e7dd42_0000941056.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\8e844e5da78f9f6cdc0e11ead4633e268d7fc94d_0000941056.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\7af8c3a358ee0d1e117e1424cd1aeb4abe14e9b9_0000941056.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\37d315106d3fc06a1fb878353f2bc6c860d75567_0000941056.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\8f4d80fdebc42fc438f4a275b746c550c9d38f04_0000941056.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\919f994d80a7ca1049d84636d9df9d59ba45ba2f_0000927744.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\da42d36d86ea47202694181a1aceace056f2a238_0000941056.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\0af6d959f3ad541dffc3dc0c1d4ab335166d4707_0000928256.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\5c9aa04f29ae02454159deeb430dce557ba54acd_0000927744.,LiQMAxHB
|
