Adware.Dealply.FB
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 9,130 |
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 2,887 |
| First Seen: | July 24, 2009 |
| Last Seen: | May 2, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Aliases
3 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| Sophos | Troj/Zlobie-Gen |
| Panda | Suspicious file |
| AntiVir | ADSPY/Toolbar.A.2 |
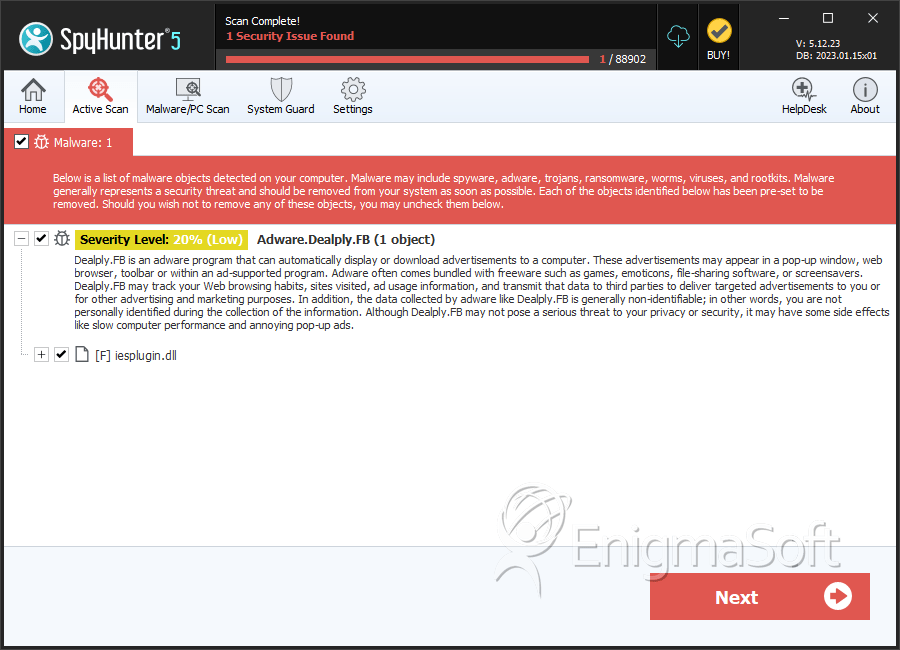
SpyHunter Detects & Remove Adware.Dealply.FB
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | iesplugin.dll | 9dbf91dee96498efd8f25fd78ff500e8 | 0 |
Analysis Report
General information
| Family Name: | Adware.Dealply.FB |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
ec304a9f0ac27bf041085f41c9fbdf0e
SHA1:
d7a73fa9e8a7a95e68a4cfd74824ec7a13685671
File Size:
633.86 KB, 633856 bytes
|
|
MD5:
a0a8a8cadeaac08a191081f4b50e9786
SHA1:
cd45b81f10ca3bfc637832158e21e1d1b812ff29
File Size:
291.84 KB, 291840 bytes
|
|
MD5:
5e805c7cb29a3d360ab90c95aeb564e9
SHA1:
62c66f57c8466fdc333a8657f89771a8957f42fe
SHA256:
D00A22ECDBA35D0D8BCFEEE260077F61B95A6004541AA3A38A162A06C222EAB9
File Size:
284.16 KB, 284160 bytes
|
|
MD5:
67c928cee09608f6597dec40437ad732
SHA1:
eb88a24d5787306330f25c097f0242d05fa8aab9
SHA256:
A613E986EAE81872681152F2A2E18F6F14B1210C6E14AA07C26A6ECEC82DB000
File Size:
852.48 KB, 852480 bytes
|
|
MD5:
4cc8a12f4c545923f61bf7497b498344
SHA1:
48ea087dd52918ed861670ef073b4902352a374d
SHA256:
C864224BE6D21867C8A64E6337FF18ED6564831464A72B95D6DFA7DA637CF7A7
File Size:
344.58 KB, 344576 bytes
|
Show More
|
MD5:
5af8006d3313b8ae89e55b06d3e0365c
SHA1:
6980aa8cce72678c2962566953fc58f7742d13a5
SHA256:
EC0A78B2926D915BBA410E5434944340AC1E333D29D6F329E985C6D36AA09184
File Size:
601.09 KB, 601088 bytes
|
|
MD5:
6a808c6aa34674ee845f071ff2b9ffc8
SHA1:
5d969b121b0b95254a4793c594cf643c6ab83f95
SHA256:
A1E3B056025FEA4F47225CC0E0C5EE9B3CE785590F6D939E2EE47D25988ADE11
File Size:
288.26 KB, 288256 bytes
|
|
MD5:
3e5b1cd37314a70d74561f33917534c1
SHA1:
6697cf344a8cc705ae79ec61e3bda41b3a447394
SHA256:
93B1980FB058FF4F2CC6E0B35C34C9A7F0C79265A3D90C37DC05D39B787424A9
File Size:
529.92 KB, 529920 bytes
|
|
MD5:
3eddc5e638324c31be411f95a6118a3b
SHA1:
1696b26c7bc94276d929c1ab570e2e34f54966ce
SHA256:
F87B83C5A8B53778375093573909F8B38872839DEAB571C44572172F198A5247
File Size:
537.09 KB, 537088 bytes
|
|
MD5:
85b322022d29afde8c3d37f55ac80d63
SHA1:
bd27fbcbc913de9076dc8635997118727dbaf08d
SHA256:
8A8E4E0A79E5456769D16DE22F01A0FF7EB73B5D8B5104C3F7A80272FB2132C6
File Size:
365.57 KB, 365568 bytes
|
|
MD5:
24f14bdab325046ac1f74eb42eca7944
SHA1:
15aca6ec11e9a0b02a59e056362f68cfeb22861e
SHA256:
F25F05FF0FF68E037B55721AF582A72842B9F5E278CBD49DFF5FD7D6F882CBA6
File Size:
489.47 KB, 489472 bytes
|
|
MD5:
3fb9232eaf9c0d9b4186127b8d7977c7
SHA1:
5ad8f06fce6a60ba8c9694ec0b703e6dc6e70de6
SHA256:
485B980BB0B9DFF1BE0E32024A4D1F3FDE8927BAC25F12BC92C07A0156E7C9A3
File Size:
177.66 KB, 177664 bytes
|
|
MD5:
238e6141244ed9e62f4f87be71789ada
SHA1:
e43f6956c6f0912d971f46d2cf177e7e1a7ced14
SHA256:
93CAD1F3D7178ECF42D9395D003C025946AF6777CC6609CE8E0A3991B19E1329
File Size:
184.83 KB, 184832 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has been packed
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
Show More
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright | Gebalisocoro Ltd. All Rights Reserved |
| Legal Trademarks |
|
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- HighEntropy
- No Version Info
- packed
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 942 |
|---|---|
| Potentially Malicious Blocks: | 4 |
| Whitelisted Blocks: | 927 |
| Unknown Blocks: | 11 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Agent.HJG
- BadJoke.TH
- BadJoke.XA
- Banker.GF
- Banload.NB
Show More
- Banload.XA
- Banload.XN
- Gamehack.PDFA
- Injector.DFF
- Injector.FGGA
- Injector.FHBA
- Injector.GDSA
- Injector.KFE
- Injector.KS
- Kagee.A
- Lamer.B
- Nanobot.MB
- Proleeg.A
- ScriptExpert.A
- Trojan.Downloader.Gen.FD
- Trojan.Downloader.Gen.KL
- Trojan.Downloader.Gen.MK
- Trojan.Filecoder.Gen.BM
- Trojan.Kryptik.Gen.FJ
- Trojan.Kryptik.Gen.MM
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Anti Debug |
|
| User Data Access |
|