ABK Downloader
The Tick APT (Advanced Persistent Threat) is a hacking group, which is best known for its reconnaissance campaigns. This hacking group does not tend to target regular users. Instead, it often goes after high-profile targets that catch their attention. Among their most well-known operations is the campaign they launched against several big corporations located in Japan. The name of the campaign was ‘Operation ENDTRADE.’ One of the tools from the hacking arsenal of the Tick APT that was utilized in the aforementioned campaign is the ABK Downloader. This is a Trojan downloader, which the attackers used to plant additional threats on the infected systems.
The Tick APT uses mostly phishing emails as an infection vector when propagating the ABK Downloader. The emails in question would be crafted carefully to appear legitimate and believable. The bogus emails would often contain a corrupted attachment or a link to a file that is housed on a server managed by the attackers. The corrupted document used in the propagation of the ABK Downloader would use two known vulnerabilities – CVE-2018-0798 and CVE-2018-0802. Both vulnerabilities are in regards to the Microsoft Equation Editor service. Users who failed to update their Microsoft Office package may be at risk of cyber attacks like the ones launched by the Tick APT.
Most APTs would make sure that their threats are capable of avoiding sandbox environments. Usually, the threat would look for certain processes or drivers, which are linked to the presence of malware debugging software. However, the creators of the ABK Downloader have used a different technique. The Tick APT has boosted the size of the ABK Downloader to 50MB artificially. Most anti-malware applications are designed to disregard files, which are equal to or larger than 50MB. This may help the ABK Downloader remain under the radar of any anti-virus tools that may be present on the victim’s system.
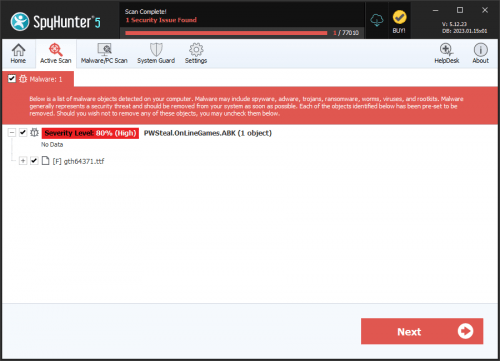
If the ABK Downloader runs on the infected computer as intended, it will fetch a secondary payload. The Tick APT may use different secondary payloads in different campaigns depending on what the end goal of the operation is.