2048 Puzzle Game
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 3,945 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 118 |
| First Seen: | April 21, 2021 |
| Last Seen: | May 17, 2026 |
| OS(es) Affected: | Windows |
The 2048 Puzzle Game browser extension is not to be associated with the legitimate portal h[tt]p://2048game[.]com/ that offers users to play a sudoku-like game for free. The 2048 Puzzle Game browser extension is published by h[tt]p://2048-game[.]review that takes advantage of the popularity accumulated by h[tt]p://2048game[.]com/ in October 2017. The 2048 Puzzle Game extension from h[tt]p://2048-game[.]review appears to be installed by 86 607 users (at the time of research), but has only two reviews that gave it a five-star rating on:
h[tt]ps://chrome.google[.]com/webstore/detail/2048-puzzle-game/bjjkmbkbhggaclclhhkahddjkfpbabcm
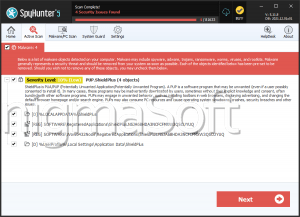
The 2048 Puzzle Game extension from h[tt]p://2048-game[.]review is considered a Potentially Unwanted Program (PUP) that may lead users to believe they are enjoying content from h[tt]p://2048game[.]com/. Computer security analysts note that the 2048 Puzzle Game extension is an ad-supported program designed to change your default search provider to h[tt]p://2048-game[.]review/?type=comoima&q=[KEYWORD] and load promotional offers on all pages you browse on the Internet. You can find out more about its marketing functionality by reading the Terms of Use, EULA and Privacy Agreement published on 2048-game.review/ext/2048/terms.html, 2048-game.review/ext/2048/eula.html, and 2048-game.review/ext/2048/privacy.html. When you have the 2048 Puzzle Game extension running in the background, your search requests via the Omnibox and search bar are redirected via h[tt]p://2048-game[.]review/?type=comoima&q=[KEYWORD] to:
h[tt]ps://search.yahoo[.]com/yhs/search?hspart=skylikes&hsimp=yhs-newtab&p=[KEYWORD]&type=comoima
The page listed above offers access to a customized Yahoo search engine that loads promotional content from a set list of affiliates. That way, the operators of h[tt]p://2048-game[.]review can redirect users to a paid content and claim affiliate revenue from Yahoo. The advertisements generated by 2048 Puzzle Game may not be verified and include links to phishing pages. Users who install the 2048 Puzzle Game extension agree that they can't seek responsibility for damages that resulted from following links displayed by the 2048 Puzzle Game extension. Therefore, you may consider the 2048 Puzzle Game app for removal.
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Downloader.Agent.NA |
|---|---|
| Signature status: | Self Signed |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
9f3504ab95f1aed7dc3a8bfa970ecd4e
SHA1:
5cc473c3aa002b23d35298deef9f32ce04ec5276
SHA256:
BF391A850A4C5E56570D2033CEF6CF81D713DC072E6371F159243306E75D1C12
File Size:
2.72 MB, 2716832 bytes
|
|
MD5:
c57cbde6a0f0771fae3c2370d261b866
SHA1:
904ee0c270ad81ec40990b31d13eb5ee954f96da
SHA256:
1A8AD57027AB4E103919D6575D79A7F9E03E30E153C368E32936C5F4DBE97CF8
File Size:
1.21 MB, 1205624 bytes
|
|
MD5:
35a50cf3b454390d5a08754f621c0a65
SHA1:
2064f1ed7e83be3410325a64f34b22a614661a30
SHA256:
CE2DB8910AD76A43A38D35A60C73FEB92DBDE77DAB4D7C13E5B8B88C071989AD
File Size:
1.26 MB, 1263512 bytes
|
|
MD5:
82328c291b95a81aaf244898bf95ff94
SHA1:
865d8590fec1d51773fa2a020b05aa4cd078a47b
SHA256:
7544B971F09023707D5E50A271045E8A79D77D6BD765341DACDA917BA1E00209
File Size:
1.26 MB, 1263512 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File has exports table
- File has TLS information
- File is 64-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
|
| Company Short Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Last Change |
|
| Legal Copyright |
|
| Official Build | 1 |
| Original Filename |
|
| Product Name |
|
| Product Short Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Better Cloud Solutions LTD | COMODO RSA Extended Validation Code Signing CA | Self Signed |
| Lavasoft Software Canada Inc. | Entrust Root Certification Authority - G2 | Root Not Trusted |
File Traits
- HighEntropy
- Installer Version
- WriteProcessMemory
- x64
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,286 |
|---|---|
| Potentially Malicious Blocks: | 390 |
| Whitelisted Blocks: | 1,891 |
| Unknown Blocks: | 5 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Downloader.Agent.NA
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| \device\namedpipe\crashpad_5064_uuobzvprpskkvdux | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| \device\namedpipe\crashpad_5064_uuobzvprpskkvdux | Generic Read,Write Data,Write Attributes,Write extended,Append data,LEFT 524288 |
| c:\users\user\appdata\local\temp\webnavigatorbrowser_installer.log | Read Attributes,Synchronize,Append data |
| c:\users\user\appdata\local\webnavigatorbrowser\user data\crashpad\settings.dat | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| Anti Debug |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
c:\users\user\downloads\5cc473c3aa002b23d35298deef9f32ce04ec5276_0002716832 c:\users\user\downloads\5cc473c3aa002b23d35298deef9f32ce04ec5276_0002716832 --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\Vggtqzls\AppData\Local\WebNavigatorBrowser\User Data\Crashpad" --annotation=plat=Win64 --annotation=prod=WebNavigatorBrowser --annotation=ver=2.1.2.1 --initial-client-data=0x2c0,0x2c4,0x2c8,0x2bc,0x2cc,0x7ff6697d58f0,0x7ff6697d5900,0x7ff6697d5910
|