Trojan.Nanocore
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 10,004 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 22,681 |
| First Seen: | July 27, 2015 |
| Last Seen: | May 27, 2026 |
| OS(es) Affected: | Windows |
Trojan.Nanocore is a dangerous threat that leverages remote access tool/remote administration tool (RAT) functions to attack a vulnerable computer. The Nanocore threat is usually identified as sneaky malware that may load on a computer where it runs in the background undetected. Such an action is a common characteristic of Trojan horse threats, and its ability to connect to remote sources or hackers is the RAT side of its source code.
Nanocore may load on a computer and then seek out data stored on the infected computer’s hard drive where it may transmit or allow a remote attacker to access the data. Such actions may take place all without any indication to the computer user, which makes Nanocore extremely dangerous.
In most cases, Nanocore will spread primarily through spam campaigns leveraging spam email attachments that otherwise look like harmless files in the for of either PDFs, MS office documents, photo files, or even executable files. Unsuspecting computer users may receive a spam message containing Nanocore that appears to be an enticing email from an alleged trusted source.
When loaded, Nanocore may hide under an unsuspecting file running within the Windows operating system. Simply stopping the process of the Nanocore file and deleting it may not completely eliminate the Nanocore threat from an infected system.
Those who may suspect their system encountering Nanocore will want to promptly utilize an antimalware resource to safely identify the Nanocore threat and allow it to be automatically removed from the infected system. Prompt removal of Nanocore will help ensure that personal data is not stolen and exploited, which can lead to many other issues, such as Identity theft.
Table of Contents
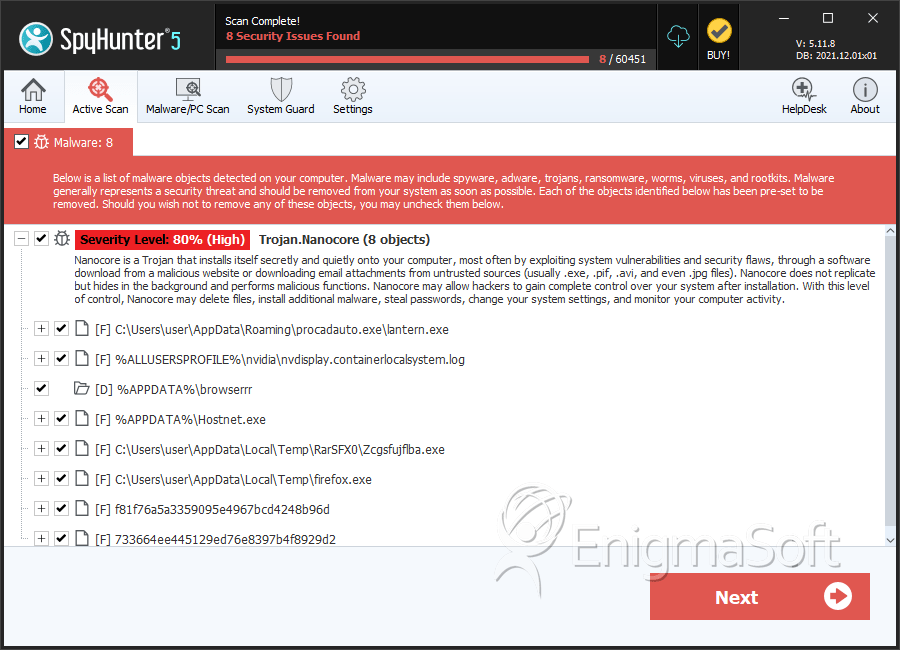
SpyHunter Detects & Remove Trojan.Nanocore
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | lantern.exe | 0b9673f415a57e85be632b45caf3277b | 3 |
| 2. | nvdisplay.containerlocalsystem.log | bf5c83624d7c6da5e0de6f5a7c523429 | 2 |
| 3. | Hostnet.exe | 1ed4196a7a4780dd900d57d5d1cfdebd | 1 |
| 4. | Zcgsfujflba.exe | 6d0f7f521401804aef80442913fce369 | 1 |
| 5. | firefox.exe | c4426ddc844a2acd9f0c9a1706eb6253 | 1 |
| 6. | f81f76a5a3359095e4967bcd4248b96d | f81f76a5a3359095e4967bcd4248b96d | 0 |
| 7. | 733664ee445129ed76e8397b4f8929d2 | 733664ee445129ed76e8397b4f8929d2 | 0 |
| 8. | file.exe | 6d9e987b193c1b78aaddaa86b17e0a58 | 0 |
Registry Details
Directories
Trojan.Nanocore may create the following directory or directories:
| %APPDATA%\browserrr |
Analysis Report
General information
| Family Name: | Trojan.Nanocore |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
00c7c183854655a60cb29dacd81474d0
SHA1:
cb765589ad4e9fd8f984a3217d31c62639432b4b
SHA256:
D22486FD8AA97B7CBF49110B23D603B419E53279D321889D262F58BF989EBEF6
File Size:
249.79 KB, 249789 bytes
|
|
MD5:
36c6a4f22db81a306509267d10858885
SHA1:
8f1702d169a069da64c10937f0011e654cf11b96
SHA256:
80EF9EEDC352C5B849C01E9265E9AA606E0B92C3643ACA148ED25A9618754FD4
File Size:
495.13 KB, 495128 bytes
|
|
MD5:
cf367f586eec6ee8e2ed1330426cb3d0
SHA1:
fd63b6f63f31be1502453dc8cf22ec8c7352d7c1
SHA256:
922EE33BBDF0BBDE2DE20D51161CBDD1D7ACD87BB35B2B2D4839FDCC337B3220
File Size:
3.08 MB, 3079168 bytes
|
|
MD5:
829d3d69613e5fd6fae72698f0344e75
SHA1:
2876b7fde017322bea3939aa14bd0a9f58ffc29f
SHA256:
3DF253EB882AB2CA863152C93FD971F953AB2700FFACDB9C387378C0B560F82B
File Size:
249.79 KB, 249791 bytes
|
|
MD5:
1842269b1b6a4b72cfeb2674833f990b
SHA1:
1704c10209c4b82db3078ec7b9e887978ebefb3b
SHA256:
356CA2D0DCAB18E5321B091384F15483DAC1B53716D6E0A21EEEA254EDBC465B
File Size:
207.36 KB, 207360 bytes
|
Show More
|
MD5:
cc214d61ebb2b63d738e64cba831722e
SHA1:
0387a2073cab7fbd99cd9c9c951b9afa6ba1097c
SHA256:
0737463D0ED8ADDD2C9ADF17C3289E48EA012750B5F826DA5B33DA8408341E3C
File Size:
207.87 KB, 207872 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have resources
- File doesn't have security information
- File has TLS information
- File is .NET application
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
Show More
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.File Traits
- .NET
- 2+ executable sections
- dll
- HighEntropy
- No Version Info
- ntdll
- RijndaelManaged
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 374 |
|---|---|
| Potentially Malicious Blocks: | 291 |
| Whitelisted Blocks: | 83 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- MSIL.NanoCore.A
- Trojan.Downloader.Gen.M
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\program files (x86)\smtp subsystem\smtpss.exe | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete,LEFT 262144 |
| c:\users\user\appdata\local\temp\tmp2461.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\tmp2481.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\roaming\bfeb5820-9643-42ad-a79f-071dff4d8e64\run.dat | Generic Write,Read Attributes |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\software\wow6432node\microsoft\windows\currentversion\run::smtp subsystem | C:\Program Files (x86)\SMTP Subsystem\smtpss.exe | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| User Data Access |
|
| Anti Debug |
|
| Encryption Used |
|
| Process Shell Execute |
|
| Network Winsock2 |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
"schtasks.exe" /create /f /tn "SMTP Subsystem" /xml "C:\Users\Cjmdlqhx\AppData\Local\Temp\tmp2461.tmp"
|
"schtasks.exe" /create /f /tn "SMTP Subsystem Task" /xml "C:\Users\Cjmdlqhx\AppData\Local\Temp\tmp2481.tmp"
|
