Trojan.MSIL.Krypt.EEBD
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
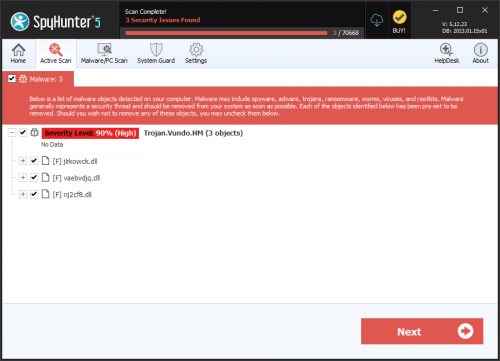
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 4,492 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 2,018 |
| First Seen: | July 10, 2021 |
| Last Seen: | April 14, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.MSIL.Krypt.EEBD |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
31b6a9a088e5dedd175408b94445b785
SHA1:
8ac459e6c9ce8aec14b592e18d2aff22d4864732
SHA256:
065CAA396E7C12066050D41E73BED5C5E608572B146E3884A5CAFEB335E94E5E
File Size:
308.22 KB, 308224 bytes
|
|
MD5:
f3755a3844cb357ad16f2de444bdbe2f
SHA1:
7f23b77e4f6d0876d9cd39d687ead204144985ca
SHA256:
F9A1D4F0E90A77E571B869C50F1C67F7074AA0F02403FD678467B6C83D89704C
File Size:
492.02 KB, 492016 bytes
|
|
MD5:
ac5f030d2e85600667764673df872d3a
SHA1:
80064f13f364c2083e168410b0b6da0a001fa7b2
SHA256:
86A78AD2599FA9B36F0BCD09F0CC6F2ADD0C2D013A42B449ED66D48B0DD0630E
File Size:
492.02 KB, 492016 bytes
|
|
MD5:
aa0012e7024e4b592b6b3a64a7ade95c
SHA1:
d005e9372a49fcd76d2279e9223b3ffec4f205ff
SHA256:
58691FA5A3A400F7E690A73F038DFE0D7726CF7F554BDC6B2CB99A193A498993
File Size:
521.22 KB, 521216 bytes
|
|
MD5:
348d350b101abc03bfa606f6fd6df6a6
SHA1:
370d9a78550c81bb0e751805617a6217d6aa20d2
SHA256:
536DEFA45735165E5B5F58C1C2A062CA0DEF1616D5826D5602AC0D6624EFC884
File Size:
495.10 KB, 495104 bytes
|
Show More
|
MD5:
dc918305a9c93a6c3cc7e651427ab875
SHA1:
d4a41998784ff62392aa0975f8b96a47e2e6c2e9
SHA256:
4C2D1427CD6FD78DEBDD0E2C195384B6127261D446C62A3CB85A97334A41F459
File Size:
591.36 KB, 591360 bytes
|
|
MD5:
530ea55e483888c90a07af23d8eaad8c
SHA1:
71b8323d847c7b460ecc8cd79ae3cde5f6aae8f5
SHA256:
E8E188D7A6A69946F7BE5B934EDCCC68EE229D4AE71EBD0045484DE0640B4E6B
File Size:
634.88 KB, 634880 bytes
|
|
MD5:
e8e0f7040dfe371a6adf210871f77ead
SHA1:
d9edef6c263d242ef46242744ffaf1d6b34b707d
SHA256:
421DB99136B0553A119729EF536E58CE8A8BE7A9C7A882124622E986FAA76E8A
File Size:
1.30 MB, 1301384 bytes
|
|
MD5:
8abac070ab68f5c5c829dead03e1b369
SHA1:
818ff49d634d2eac59cc902bdca0b94cddb2f1f3
SHA256:
7DBADDBD11D8C575EFE5E341E80CB146E5609D81EB816A70F1ADBDA525DF4DB8
File Size:
569.34 KB, 569344 bytes
|
|
MD5:
55aae602a6102ad3d20c29a3aeeee40b
SHA1:
519b1f2f457e3d562315f73f04c52b6d2304d43d
SHA256:
85FDD735883A3B7190F88637A90FB99753AB9E0095BE15462731E4D638DA4178
File Size:
673.79 KB, 673792 bytes
|
|
MD5:
4a4f6c43442a23b57711092eb1608bde
SHA1:
2e761b4fe4c1b32a4024489edf3e288b9c26cecf
SHA256:
79757833B8F03E206BBFC53AF04FAE68FE77AD22BB2127C9A43F7335428FF92E
File Size:
425.47 KB, 425472 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is .NET application
- File is 32-bit executable
- File is 64-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version |
|
| Comments |
|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Legal Trademarks | LukasSoft! |
| Original Filename |
|
| Product Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| For Ecopetrol | For Ecopetrol | Self Signed |
| Phil_Pilcrow | Phil_Pilcrow | Self Signed |
File Traits
- .NET
- HighEntropy
- x64
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 117 |
|---|---|
| Potentially Malicious Blocks: | 7 |
| Whitelisted Blocks: | 46 |
| Unknown Blocks: | 64 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| User Data Access |
|
| Anti Debug |
|
| Encryption Used |
|
| Syscall Use |
Show More
|