Trojan.MSIL.Bulz.S
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
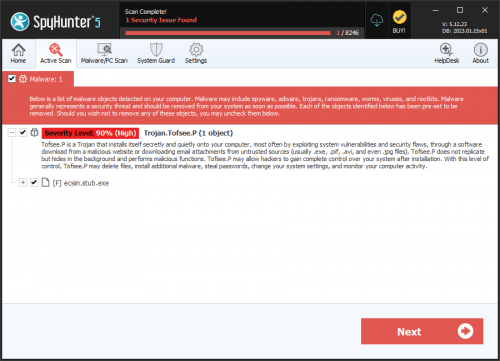
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 6,960 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 260 |
| First Seen: | November 17, 2021 |
| Last Seen: | April 19, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.MSIL.Bulz.S |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
96c295e7b032ac242abc59a8b6a1c938
SHA1:
fe6e449b6a13b8f4ccc0a03c221996fb62146e63
SHA256:
4EAE6A2AC9DF0BAB1615CABEA8EAE4F77272987FC52E48F580DD58694ED7D939
File Size:
186.37 KB, 186368 bytes
|
|
MD5:
0738e7f05467d775a4a5a2a5b91978eb
SHA1:
55edca4272903a0b294795657a428bc1b2a91a66
SHA256:
F3E8BC5A2FCBF0C430D60FD20C07E7E7C3611D90969F4BD5D7A965D2466B3AD5
File Size:
227.33 KB, 227328 bytes
|
|
MD5:
ead30f738742d98bc66e783f529f6503
SHA1:
b4008091637891a6cf42f752c13952ed838eb850
SHA256:
129BF41D1A3E5352A2DB3E7EB518580AE365401DCD078B8CECCB4471419214C4
File Size:
3.12 MB, 3123712 bytes
|
|
MD5:
a64474f814dde17fd190614da0292ed5
SHA1:
6a242f269a6541d51b9fd65c15402335e277d595
SHA256:
E947DF4CD7CD0A2F8044603ADDD586CEB700A2ADEA14344F6EC44EC485B75833
File Size:
3.70 MB, 3700224 bytes
|
|
MD5:
cfee8b573ce5932451ae5feaad399808
SHA1:
42817f3c1b5aea77151b52f19b5f2cafd7ef0480
SHA256:
7A5FEA4E4BE34DA78525225C2AF9C475B5FC9EC64AFD61994F99EACE1AFDC603
File Size:
522.24 KB, 522240 bytes
|
Show More
|
MD5:
6a8834bc848ff826f39ab96307bf3833
SHA1:
1520c58ebde256cbc43d573aa5cc71eae67ffd95
SHA256:
4C39610C28BE30FE5EB36EAEBB103ABE51852AF23C30E95CAC6E306C1F476B71
File Size:
216.58 KB, 216576 bytes
|
|
MD5:
90f33e9fb45bf049fd2c39061d854cf4
SHA1:
d950a31a35c3b94b9da9d49895b7392f1373556a
SHA256:
BF0C1DD821DDCB400C094834236ADB34F7B9121C27A0DEF6A4D6013A4376B539
File Size:
206.34 KB, 206336 bytes
|
|
MD5:
1f0bdc0204d01a8608cbcd677077b5ce
SHA1:
e8797bfab5be72c5b9885d129344b28cabeba862
SHA256:
35EC8813728F830EC726BFF3DCAC78E3BA43B614231FE2C73649273587EA93F5
File Size:
226.30 KB, 226304 bytes
|
|
MD5:
78348f75da7c3986a43c66b8beaf48de
SHA1:
5aa05429de7834627bf083d1af69430a895dd125
SHA256:
7F05558329C48D9B24B715A369F6178734C2117ECF577E52423252A501E8507A
File Size:
975.36 KB, 975360 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have security information
- File is .NET application
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version |
|
| Comments |
|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Legal Trademarks |
|
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- .NET
- dll
- HighEntropy
- Reactor
- Reflective
- RijndaelManaged
- WriteProcessMemory
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 164 |
|---|---|
| Potentially Malicious Blocks: | 20 |
| Whitelisted Blocks: | 53 |
| Unknown Blocks: | 91 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\programdata\isolated storage\a513bf6e\59fd041e | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\programdata\isolated storage\a513bf6e\90424e7e | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\software\microsoft\windows nt\currentversion\notifications\data::418a073aa3bc1c75 | RegNtPreCreateKey | |
| HKCU\cid\{b1159e65-821c3-21c5-ce21-34a484d54444}\a513bf6e::0 | RegNtPreCreateKey | |
| HKCU\cid\{b1159e65-821c3-21c5-ce21-34a484d54444}\a513bf6e::1 | RegNtPreCreateKey | |
| HKCU\cid\{b1159e65-821c3-21c5-ce21-34a484d54444}\a513bf6e::3 | RegNtPreCreateKey | |
| HKCU\cid\{e4580f81}\a513bf6e::0 | RegNtPreCreateKey | |
| HKCU\cid\{e4580f81}\a513bf6e::1 | RegNtPreCreateKey | |
| HKCU\cid\{e4580f81}\a513bf6e::3 | RegNtPreCreateKey | |
| HKCU\cid\{d3558e25-821f3-72c3-8a52-54a482a54739}\a513bf6e::2 | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| User Data Access |
|
| Anti Debug |
|
| Encryption Used |
|