Trojan.Ekstak.DH
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
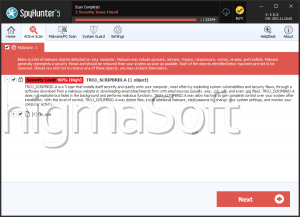
| Popularity Rank: | 10,734 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 33,390 |
| First Seen: | July 26, 2021 |
| Last Seen: | January 8, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Ekstak.DH |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
9223dc3e15767f8b6f7c284a3efafb13
SHA1:
715efca4a26d4f948809bf9dd64860ede314dde6
SHA256:
2FAE493AD5B0CA0A15C84D57D3438FBCD1016E87DD7770795D0D5BC28DCA3EA0
File Size:
2.68 MB, 2678783 bytes
|
|
MD5:
744040819b80efa04538c551c82b652f
SHA1:
d37ce74ef8b75cb1e3cc21ec12da509537329f17
SHA256:
05857ACB60C0A7D89CA4BB84416BA90EC7C07EEFA36A0C774A7B0C9BABB8523B
File Size:
1.59 MB, 1589243 bytes
|
|
MD5:
c42489605c55e9afa1b21acba572af59
SHA1:
02753362a6db383c897e4814ae7b9fde528eecae
SHA256:
4C75207FEF3CB194FC9B87924C5028A8DCA311883048EB96750896D97BF0FECF
File Size:
2.31 MB, 2314230 bytes
|
|
MD5:
e0f89fc11a329ced108edc45c8885875
SHA1:
b8a5eab523806e178b0eb90733cf1a8999d0c340
SHA256:
82224D3331A093C0A3077B22043C2D17BCDF7DFB84D976CDC6646BE1489E8265
File Size:
2.16 MB, 2161145 bytes
|
|
MD5:
f26c76e6afa3464fe3d5bb4ff8ad27f3
SHA1:
5398fa7d337ccdfdaff4755aa9104b7d5e3186a7
SHA256:
F41C706F47C0255C08F1E9842B097AD5BDC9E8F832B7AC0F94B33C8AE9CE1995
File Size:
3.50 MB, 3502080 bytes
|
Show More
|
MD5:
2b89c29a8d3cb3cf54b3f60cd1be85a6
SHA1:
89cc501a00a7070bc413923b125e396e79886d40
SHA256:
5B1B5C275E060C1E078C91074C01EAEBADA7E9E2B7D9BCAD8B7E681169B89F5A
File Size:
2.99 MB, 2985848 bytes
|
|
MD5:
d48d2c30864a805e80da30047f608482
SHA1:
42b42131ec0e767d26c1e135dd1237e3b16bada8
SHA256:
EDA85736E7D2C3600FC67AC2666014FDE452EA7E5C8CA2F265E3E8A161592876
File Size:
2.70 MB, 2695167 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | S.M.A.R.T. Assistant |
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright | MaxLim |
| Legal Trademarks | Exff F. Ronif |
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- 2+ executable sections
- HighEntropy
- Installer Version
- No Version Info
- VirtualQueryEx
- WriteProcessMemory
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,374 |
|---|---|
| Potentially Malicious Blocks: | 77 |
| Whitelisted Blocks: | 1,282 |
| Unknown Blocks: | 1,015 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Network Winsock |
|
| Keyboard Access |
|