Trojan.Agent.TJW
Threat Scorecard
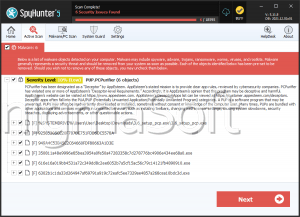
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 10,742 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 38 |
| First Seen: | May 20, 2024 |
| Last Seen: | May 28, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Agent.TJW |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
7f08fc4c7b321ad0484301da31dd439c
SHA1:
d6de7469e7553e38143beecafe38068c17546af6
SHA256:
E2F2705847381440417AE99B97A8B97CDDBC7EC63896B9AF65E090B55D0D9673
File Size:
1.95 MB, 1947136 bytes
|
|
MD5:
1f7455ea3e1bbc7a516f6b08e8e0609a
SHA1:
59ca562a9fcf05b81663e14449a09ab32cb6845c
SHA256:
757F5AAD8809C9396795AD30AEAD17BA1A80EDFDD7D7B37A93E2407826CE52B5
File Size:
1.77 MB, 1771008 bytes
|
|
MD5:
70522e52c60e3706dc12df5a787ee445
SHA1:
2fe198bdf31ca0b6ccf37868a5f3680192a6c376
SHA256:
ABF8F49D92689A7A4C5CB064902892445FB4FA7389B9A08058F7A216F8AA4B41
File Size:
1.77 MB, 1767936 bytes
|
|
MD5:
ca986a4c01b3346513b31763348845ce
SHA1:
3a97b1701e57db5d7e93b3f8d68f1ee5e0296cec
SHA256:
B9487B1E5353BD0063BA1647A9AC84125C57717F8B9390AF323EF1C7D0E5842D
File Size:
1.63 MB, 1634816 bytes
|
|
MD5:
54b114af8750d67db8587f160f76e765
SHA1:
1453df25901bd3584f0f35802d3e2c4cdd9b8e16
SHA256:
21F5F495F4306DF2F457B592A4BB3F63211403636F5A5F094981978092390F23
File Size:
1.63 MB, 1634816 bytes
|
Show More
|
MD5:
491ad0d2f02bcddafe3b9e736d2aeed0
SHA1:
4b69945e76eba69a9c0eb8307b170d8f5c342282
SHA256:
43DAD112BE3ADC8158C64DC8AEC90FA094916343D8D8831FE22201C4C7ED4CB7
File Size:
2.72 MB, 2718208 bytes
|
|
MD5:
c9e241f521c93cb0929a5e2995f5033f
SHA1:
eaf903abf14505fa88bb7c788df6b5469ceba23f
SHA256:
7B3136E4C02F4F6371E7E4F914EBF7D4C707F8FACAC1D7A28F4D993FD8AF4BB8
File Size:
3.60 MB, 3599360 bytes
|
|
MD5:
3206012036e34de7c48b1ecc2389af35
SHA1:
85ede41efcea75b0ae9ed06478c9a5656506ce00
SHA256:
541D93902BDD5A63D13176FDE263A45E7FCDC6C8B4E2250A9A0BB578C1B453E8
File Size:
2.73 MB, 2725376 bytes
|
|
MD5:
4c5b7a0493aa74fcf73ad91b8b4d0032
SHA1:
4b5954dadf158dc3a1d9adb8ceecbc7f084bda2b
SHA256:
EA0ED69C5F2557015E626DA6DFBE66174900654CD53C167D69853C516A5EC9AC
File Size:
1.77 MB, 1771008 bytes
|
|
MD5:
d6b4b4f4dd4938f75b9459ed52486331
SHA1:
b3420fc4dad318a4d60ce7cf214476abec0b296d
SHA256:
F39A710D4915F5A9BCCC44C75FCAD9D8A43CA435311E572A9B87842C67BC07BC
File Size:
1.79 MB, 1785856 bytes
|
|
MD5:
ff5e960655665e3064239dc535a7796f
SHA1:
3675b0b2253dea89631c0393a89614af35181fe9
SHA256:
BECADE38A0780F269E64775DA99F7FFB3C26A46722A6C1B3D20A80C5326D0266
File Size:
1.64 MB, 1635328 bytes
|
|
MD5:
956af069d89c8eb1b1753086c749a608
SHA1:
b975b34f6e1fa5a7b16c09dee511eb88291a25d4
SHA256:
5B525FE731C516632BF5DAB84E94E43B6248A71C4A72CC32DF8359306E067CC1
File Size:
1.76 MB, 1760256 bytes
|
|
MD5:
0076fd1144c4113c3ffd56763fa87dfc
SHA1:
32bd406a35b8161b8a6f5d8809c2ed724aba9391
SHA256:
241A3174774C9E64C934703C5D79EA5F451803C366A31B08BAAD758AE327C19E
File Size:
2.72 MB, 2722816 bytes
|
|
MD5:
5d8b098e71102effdc473c46bfd3dd84
SHA1:
041570dfbc0b97639e268eacc6146aec3100b290
SHA256:
B7201D7EC692316C1A654C3687E1F81B9CC335122EB014789D4F3F55768F1675
File Size:
1.64 MB, 1642496 bytes
|
|
MD5:
2680213d61b740b08b55050ff5e652bb
SHA1:
3a06da95986495727879c64a78524cb1956f778e
SHA256:
FA87E7A90E50E03F289C1A5327B45F2BA94E6E9FE046910149A79585C4F0DECD
File Size:
2.30 MB, 2296832 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have security information
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- dll
- HighEntropy
- WriteProcessMemory
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 391 |
|---|---|
| Potentially Malicious Blocks: | 124 |
| Whitelisted Blocks: | 255 |
| Unknown Blocks: | 12 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Agent.TJW
- GameHack.FD
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Shell Execute |
|
| Anti Debug |
|
| Process Manipulation Evasion |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\d6de7469e7553e38143beecafe38068c17546af6_0001947136.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\59ca562a9fcf05b81663e14449a09ab32cb6845c_0001771008.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\2fe198bdf31ca0b6ccf37868a5f3680192a6c376_0001767936.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\3a97b1701e57db5d7e93b3f8d68f1ee5e0296cec_0001634816.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\1453df25901bd3584f0f35802d3e2c4cdd9b8e16_0001634816.,LiQMAxHB
|
Show More
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\4b69945e76eba69a9c0eb8307b170d8f5c342282_0002718208.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\eaf903abf14505fa88bb7c788df6b5469ceba23f_0003599360.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\85ede41efcea75b0ae9ed06478c9a5656506ce00_0002725376.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\4b5954dadf158dc3a1d9adb8ceecbc7f084bda2b_0001771008.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\b3420fc4dad318a4d60ce7cf214476abec0b296d_0001785856.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\3675b0b2253dea89631c0393a89614af35181fe9_0001635328.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\b975b34f6e1fa5a7b16c09dee511eb88291a25d4_0001760256.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\32bd406a35b8161b8a6f5d8809c2ed724aba9391_0002722816.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\041570dfbc0b97639e268eacc6146aec3100b290_0001642496.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\3a06da95986495727879c64a78524cb1956f778e_0002296832.,LiQMAxHB
|