Traffic Exchange
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 56 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 1,074,009 |
| First Seen: | November 11, 2016 |
| Last Seen: | January 11, 2026 |
| OS(es) Affected: | Windows |
The Traffic Exchange software from Microleaves Ltd may be promoted to PC users as a type of shopping enhancer that connects the users to ad publishers directly. The Traffic Exchange application can be installed on Windows-powered computers for free, and you may be lead to believe that the Traffic Exchange provides betters deals on your favorite online shops. PC users may be invited to install the Traffic Exchange program and benefit from personalized discounts, promotions, limited-time deals and exclusive offers. The Traffic Exchange application from Microleaves Ltd is classified as a Potentially Unwanted Program (PUP). The Traffic Exchange software is known to promote questionable computer support companies, invite users to install unreliable cybersecurity tools and run from 'C:\Windows\fvxeupdate.exe.' The program at hand may drop files in the following locations:
C:\Microleaves\Online Application Installer\prerequisites\Traffic Exchange.exe
C:\Microleaves\Online Application Installer\prerequisites\aipackagechainer.exe
C:\Program Files (x86)\Microleaves\Online.io Application\Online-Guardian.exe
C:\Program Files (x86)\Microleaves\Traffic Exchange\Online-Guardian-v2.exe
C:\Windows\System32\Tasks\Online Application Updater
C:\Windows\System32\Tasks\Online Application v2 Guard
C:\Windows\System32\Tasks\Online Application v2 OG
The Traffic Exchange program may add scheduled tasks in Windows and connect to ad servers every five minutes. The ads by Traffic Exchange may be presented in pop-up windows, floating ad boxes and may show up as hyperlinked text on pages. Security scanners may mark the Traffic Exchange software as 'PUP.Optional.OnlineIO' and 'Adware.TrafficExchange'. The content loaded by the Traffic Exchange in the browser might include links to phishing pages and insecure pages. It is advised to consider the Traffic Exchange for removal with a trusted anti-malware utility.
Table of Contents
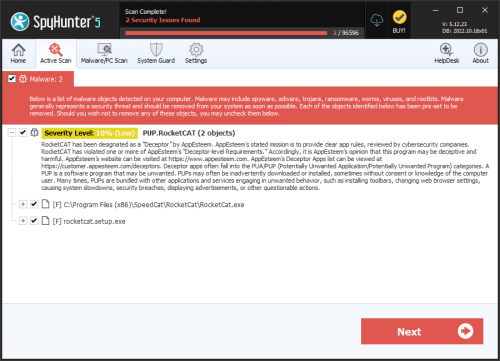
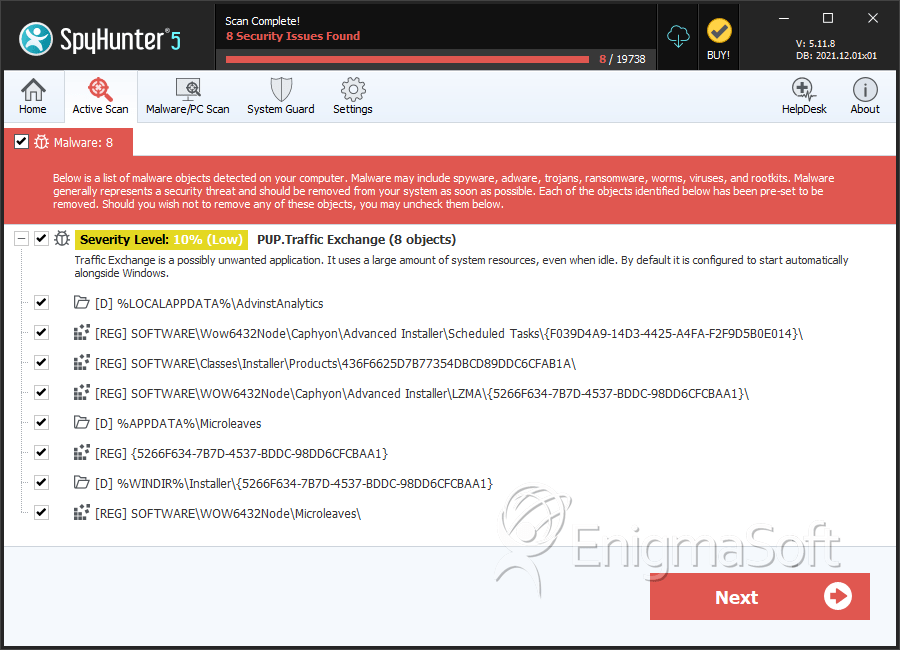
SpyHunter Detects & Remove Traffic Exchange
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | aipackagechainer.exe | 625151080b293da9ccb7f2100e43255f | 6 |
| 2. | Online-Guardian-v2.exe | b62f3eee71d915df81c040007955b6b9 | 4 |
| 3. | Online-Guardian.exe | b1956bcc37f7b28bc8ad2efd16060c87 | 2 |
| 4. | OnlineGuardian-v2.exe | f4d0dd1537ebebd0a8daa73f60e160be | 1 |
| 5. | Online-Guardian-v2.0.9.exe | ab0e97b4881076a20461f49bcafa1d57 | 1 |
| 6. | Online Application Updater.exe | 016ce1783d079384774fb3ffee95c169 | 1 |
| 7. | file.exe | 1ae34060ed111aec2e3c914270ef6131 | 0 |
Registry Details
Directories
Traffic Exchange may create the following directory or directories:
| %ALLUSERSPROFILE%\Microleaves |
| %APPDATA%\Microleaves |
| %HOMEDRIVE%\AppData\Roaming\Microleaves |
| %HOMEDRIVE%\Users\Default\AppData\Local\AdvinstAnalytics |
| %LOCALAPPDATA%\AdvinstAnalytics |
| %PROGRAMFILES%\Microleaves |
| %PROGRAMFILES%\Online-IO |
| %PROGRAMFILES%\Online.IO |
| %PROGRAMFILES(x86)%\Microleaves |
| %PROGRAMFILES(x86)%\Online-IO |
| %PROGRAMFILES(x86)%\Online.IO |
| %USERPROFILE%\Local Settings\Application Data\AdvinstAnalytics |
| %WINDIR%\INSTALLER\{52F7BE5C-2C3B-4C7B-A96D-F19B9EC1992D} |
| %WINDIR%\INSTALLER\{F0847AE0-465A-4D7B-A555-AABB43B550F0} |
| %WINDIR%\Installer\{438465C5-D78D-4958-B31D-60374B5042F4} |
| %WINDIR%\Installer\{5266F634-7B7D-4537-BDDC-98DD6CFCBAA1} |
| %WINDIR%\SysWOW64\config\systemprofile\AppData\Local\AdvinstAnalytics |
| %WINDIR%\System32\config\systemprofile\AppData\Local\AdvinstAnalytics |
| %WINDIR%\system32\config\systemprofile\AppData\Roaming\Microleaves |
| %WINDIR%\syswow64\config\systemprofile\AppData\Roaming\Microleaves |
Analysis Report
General information
| Family Name: | PUP.Traffic Exchange |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
2b668b082327c837962c025b4fe39cf9
SHA1:
4b290fec2aea3d2dab28b78f7a4d86a16673c912
SHA256:
C05B5B66C6101E7A7532D8086BEB4682DB80535FB02839CA02A4140F5EA701F8
File Size:
1.11 MB, 1114431 bytes
|
|
MD5:
f5d11eaf8ebfb21bceffa953b25b4bd7
SHA1:
3408787835b53960b24b35d07ec5cda39f091f23
SHA256:
C473CAB817FF208075C4D0D7A387E0FA868C6CF736E8E0B3968AC2B73617DCF5
File Size:
862.26 KB, 862262 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | AdvancedWindowsManager |
| File Description | Windows Updater 5.0.4 |
| File Version |
|
| Internal Name |
|
| Legal Copyright | Copyright (C) 2022 AdvancedWindowsManager |
| Original File Name | Windows Updater.exe |
| Original Filename | TJprojMain.exe |
| Product Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Microleaves LTD | DigiCert Global G3 Code Signing ECC SHA384 2021 CA1 | Hash Mismatch |
File Traits
- x64
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Other Suspicious |
|