PUP.Gamehack.GLB
Table of Contents
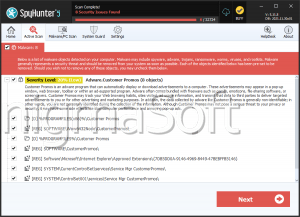
Analysis Report
General information
| Family Name: | PUP.Gamehack.GLB |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
a476040d2dec43a2095ccd17dcfd3f8f
SHA1:
411694f470b1a1945a912eb9dca7786f940ff31a
SHA256:
6F53216B77127802520A96C7813CAA1561BDF6310EE12E2282B0D4089CF7A766
File Size:
2.45 MB, 2447360 bytes
|
|
MD5:
579150959d85f69faa921bb5c784e87f
SHA1:
adac66fdc70430a5d90d45e2573f4887a051676f
SHA256:
D34C56F63B363514D8E6A9E86D8343684398EA783CC4CA54CDD6AFA9B8423D71
File Size:
2.44 MB, 2441216 bytes
|
|
MD5:
779662aaa21c8ab9ba620070f7299cfc
SHA1:
f19b869912503af2dd7b9301fcba400c4ac5647e
SHA256:
9611FCC75E057C6C0FA2CABD4B010323F17B89932C82F9A40DE83F5F0406670E
File Size:
1.85 MB, 1849344 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have security information
- File has TLS information
- File is 64-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.File Traits
- 2+ executable sections
- GetConsoleWindow
- imgui
- JMC
- No Version Info
- x64
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 3,071 |
|---|---|
| Potentially Malicious Blocks: | 296 |
| Whitelisted Blocks: | 2,523 |
| Unknown Blocks: | 252 |
Visual Map
0
0
0
0
x
?
0
0
0
0
0
x
0
?
0
0
?
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
0
?
0
?
?
x
?
0
0
0
x
0
0
x
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
?
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
x
0
0
0
0
0
0
0
0
0
0
x
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
?
x
x
?
?
0
x
?
?
0
0
0
?
0
?
?
?
?
0
0
0
0
0
0
0
x
?
0
0
0
0
0
0
0
x
0
0
x
0
x
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
x
x
?
0
0
0
0
0
0
0
0
0
0
x
?
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
?
0
0
0
0
?
0
?
?
0
?
x
0
x
x
x
0
?
0
0
?
?
x
?
x
x
x
x
0
0
x
?
?
x
x
?
?
x
?
x
0
?
x
0
x
?
?
?
?
?
?
?
?
?
?
?
x
?
?
x
?
?
x
?
?
x
x
0
x
?
x
x
0
x
?
x
?
x
x
?
?
?
x
?
x
x
x
?
?
?
?
x
?
?
?
?
?
?
?
x
x
?
?
x
?
?
?
?
?
0
?
0
0
0
x
0
0
0
?
?
?
0
0
x
0
?
0
0
?
0
0
0
0
?
?
?
?
0
?
0
?
?
0
0
?
?
0
0
?
0
0
?
0
?
?
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
?
0
0
0
?
x
x
0
0
0
0
x
0
0
x
x
0
0
0
0
0
0
0
0
0
0
0
?
x
0
x
0
0
0
x
x
x
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
x
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
0
0
?
?
0
0
0
0
0
0
0
x
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
0
0
x
x
0
?
0
?
?
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
x
?
0
0
0
0
?
x
?
0
0
0
?
?
0
?
?
?
?
0
0
?
0
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
x
x
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
?
0
0
0
0
0
x
?
0
x
0
?
?
0
?
0
0
0
0
0
x
?
?
?
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
x
0
0
x
0
x
0
0
0
x
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
x
0
0
0
0
0
0
0
x
?
?
x
?
0
x
x
0
0
0
0
0
0
x
0
0
0
0
?
?
0
0
0
0
?
x
?
?
?
?
?
0
?
?
?
x
?
?
x
0
x
0
?
0
0
x
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
x
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
?
x
0
?
x
0
0
0
0
?
?
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
x
0
?
0
0
?
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
?
0
0
0
0
x
0
0
x
?
0
0
0
0
0
0
0
?
0
x
x
0
?
?
?
?
0
0
x
?
0
0
0
x
?
0
0
x
x
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
?
x
?
x
x
x
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
x
0
0
0
0
0
0
?
0
0
0
x
x
0
0
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
?
x
0
0
0
0
0
0
0
0
0
x
0
0
0
x
0
0
0
0
0
0
0
0
0
0
x
?
0
0
?
x
0
x
0
?
0
0
0
0
0
0
0
0
0
x
0
0
0
0
?
0
0
x
0
0
0
0
0
x
0
x
x
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
?
?
?
0
0
0
0
0
0
0
0
?
?
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
x
?
?
x
x
x
x
?
?
0
?
0
x
0
x
0
?
?
x
0
x
x
0
?
0
0
0
x
0
x
0
x
x
x
?
0
x
x
x
x
x
x
x
?
x
x
0
x
x
x
x
x
x
x
x
?
x
x
0
?
x
0
0
0
0
?
x
x
0
0
0
x
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
?
0
0
0
x
0
0
0
x
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
x
x
x
x
0
x
x
x
x
0
0
0
x
x
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
x
x
?
0
0
0
x
x
0
0
x
x
x
0
x
0
0
x
0
0
0
x
x
x
x
0
0
0
0
0
0
0
0
0
0
0
x
x
0
x
0
?
x
x
0
x
0
0
0
0
0
0
...
Data truncated
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Agent.KFF
- Clipbanker.DO
- DllInject.LF
- Downloader.Agent.LH
- Gamehack.GLB
Show More
- Gamehack.SBG
- MSIL.CsgoHack.PA
- Trojan.ShellcodeRunner.Gen.AN