PUP.Gamehack.GAGE
Table of Contents
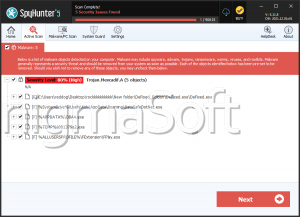
Analysis Report
General information
| Family Name: | PUP.Gamehack.GAGE |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
be14627bbf1fcc7c59dcd4b65b6658cb
SHA1:
3d43ce365f5db2310c9c145ad0bf517fd5d18e51
File Size:
2.40 MB, 2404352 bytes
|
|
MD5:
c22f656c5a33dd3d826f5587cccfd4ed
SHA1:
897eace504ba1886009409dc83e6b97a97ca47d1
File Size:
5.92 MB, 5922816 bytes
|
|
MD5:
b33482614177d96046247208b5c111b4
SHA1:
c2940aa37733046a8eaecdff965873d2bf87b287
SHA256:
35C45EA2D57ABE1DF456AF3715A7A4E51A771AF7157FA0D9F01BC0FC81C26DE1
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
ad55cf8950afb823c4f19a799f433636
SHA1:
582300b98dda19b127d9646ea3c8ed8b1e34bced
SHA256:
E77FB55602982BD7350066F9B5BF58CB4B02F384B833365A6DDC93859CD01249
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
4b1e25722924bdc422ccdbc803079daf
SHA1:
cdf2ce97c1da49c69f4f1d8ce22a9e87fcb1e4f3
SHA256:
945F480AB3B95F2A4DCC5FD238712B87B6096FE3FCD90D9798968D3C87C2B3ED
File Size:
5.65 MB, 5650710 bytes
|
Show More
|
MD5:
a4a27b4793a1c650c6cd680f97b30ca4
SHA1:
9ffa1ae1b8e6608aaf68307c924f2749f390bdbf
SHA256:
28AE371C597214B417EB9A777F21E11ABACC2C5D95A20E3990C4EB691DB08AE0
File Size:
5.49 MB, 5485568 bytes
|
|
MD5:
56423484c6a1d770a6c83b632561dd7e
SHA1:
013fcb0fa70d3faceb5ce9350c3f108c809bc55b
SHA256:
2C092014E8279C7A52AAEADFD29EC2D92C821CB2A7071538901568F45363B146
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
252ecdf273ceb65f637fc44793404436
SHA1:
3f5570c411d6a44bfab68b588b53edda7be5e707
SHA256:
178194C871825D9C9468058E11436BEC6597C1906B860A8DA55D1B622E2E1441
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
be15b95098db42d95bd75bec78a4a053
SHA1:
82788d5a78214678fa6edf05d53710d9696c1082
SHA256:
F5E547B2511D2A4E23DFF36C76E507367C9C8F0043333F7064F7B2D32182ACF6
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
05ef421df3a432949ddf1a61f7fa2ba5
SHA1:
62ba6b99c737d3473f7290ec236e6272025dd560
SHA256:
FFF7BFEA3938711997D8E73595A6946D2B66BC81A86877D2302190B4AE608E4A
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
632c8db6a722f68b2c8fd2510e94e805
SHA1:
db3a9dbb8f2d42997c4dbffe9604a3bf910aa52b
SHA256:
751929934864A8543164D5086A84747D410D5F61666ED488F65ED7A90A123187
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
753160b8c9da7bba7e1f2ae32cf396d7
SHA1:
0db394ce7cf41dbfaa678191e4031f55953b11c4
SHA256:
401969C15AB13B231E069BAF4009441A4843099E9D58B973E1950C3C05ED9621
File Size:
4.20 MB, 4202496 bytes
|
|
MD5:
6e32dc46aff82dd62db01d698c6a4331
SHA1:
71b5d64345af7a0787f02d18b788736da2761c8e
SHA256:
F2EEA268CED7BD251D0495631CE2DD6D70140AE70F4DA61361C0092F8891FA50
File Size:
2.89 MB, 2885632 bytes
|
|
MD5:
45c4cd8efc855e97c23b9b8c396a6dd5
SHA1:
e16d33cd71737e762382e9bcdc44fc563b32260c
SHA256:
3A2C06E4AEE34D25BAA205681652D839FCF7D98391E19329DE2B32BEB24F2C9E
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
bb30cf4b0fe486649c06f48277cad487
SHA1:
c09980f7aa403b8acf57c0959f70f990bd5aaad1
SHA256:
BEE3CECF5CB13FBED931274C3AB7FAADE3A1E3924121AB7689C302E889738146
File Size:
1.96 MB, 1960960 bytes
|
|
MD5:
2439e6a5e9aeeb4a3a71dd13c32c21de
SHA1:
38c12f3001a9443859377a4543f61d444a8909db
SHA256:
8AD4BA94710D8CC63D1A863527DCFC3E13FF7155205856955628468E3589E712
File Size:
9.71 MB, 9705984 bytes
|
|
MD5:
27eb68c2e5edab53b422fb2daa2664a6
SHA1:
ef9af7f0f8f00c1d12d8cdf759a0b08e7e843c24
SHA256:
B9CBC4EA4002A202EA77EA60E0BDA818CA957F96F3D0CDFAA79B1EEB40280DFD
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
6d8b5d394dd568be654dc3e321bb663c
SHA1:
7ffb0d429749f0b05ca6f4bae98bdc4367aca580
SHA256:
275FFEB147B11CF1395D9F6B6220DB4B9F0018FA9A6C99C8B8443C8B4231D3BD
File Size:
817.15 KB, 817152 bytes
|
|
MD5:
127681320226541b05f8fcfa118485b3
SHA1:
0364991b295f8b14e0796e06b0387a65286befa4
SHA256:
D622C4CB1B1752E2BE8CB492A342BA490B547B18998F1692F6910C258FA34C87
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
5c0433a8ba0bc7c5202806ffe78d04f9
SHA1:
79c0019eddb5744f095c5ce3bf6f5e1264a55f3c
SHA256:
C1CC40E2AC7DC84032C3D356FF0EC25863F975747D2734570DB7B70636AAEAF1
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
0d95f0e97e017267e34788fbd496523e
SHA1:
67698da2900066c43db98a671a981711161df5b2
SHA256:
EFD7BE03C4199C729F832BEC484F81BC4147578AE1550514900DB517F986E628
File Size:
2.45 MB, 2454528 bytes
|
|
MD5:
0c76fd7af17cac5bc543a2cabd351bba
SHA1:
04c8f0280ca00a9a8a32ded4efcfb596366c6609
SHA256:
EC193EB99ADA2E68734331C440FF442EA6E835042E4A3A6114376E18125D47E3
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
df7fd680de0253723ce3a13db0c5b945
SHA1:
caf7db040fb8c77be5fb236b4da6110e54575ebc
SHA256:
CDA406C45D6BEDA13839B182D313BD1101F6A745E81A1C29359A544B87376184
File Size:
816.64 KB, 816640 bytes
|
|
MD5:
c80752851400854432420ace23988c5e
SHA1:
c2b43977aef88592a5d353a4699e0bf0e1c2aa25
SHA256:
B564FC55F5AD5BB99C40441CB9BDDFA41B4A222DB2D11E22EFB9A51BA400F89A
File Size:
3.19 MB, 3189248 bytes
|
|
MD5:
a1788f6739ec08cc2f752b13297638ff
SHA1:
6bbdc52e1e4d72424179bedbf3c603ff16371e30
SHA256:
EDEADE56E6A19D5D123BDCA41D693180A21B1708C112098930777164C6ABB550
File Size:
816.64 KB, 816640 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has TLS information
- File is .NET application
- File is 32-bit executable
- File is 64-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
Show More
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version | 1.0.0.0 |
| Comments |
|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Legal Trademarks | VISON SECURYT |
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- dll
- imgui
- x64
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 969 |
|---|---|
| Potentially Malicious Blocks: | 8 |
| Whitelisted Blocks: | 961 |
| Unknown Blocks: | 0 |
Visual Map
0
0
x
0
0
0
0
0
0
x
x
0
0
x
0
0
0
x
0
0
0
0
0
0
0
x
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Downloader.Agent.BTAS
- Gamehack.GAGE
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
112 additional items are not displayed above. |
| User Data Access |
|
| Anti Debug |
|
| Encryption Used |
|
| Other Suspicious |
|