PUP.Gamehack.GACC
Table of Contents
Analysis Report
General information
| Family Name: | PUP.Gamehack.GACC |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
d819808480e9b9f1d7e20b06379e38c4
SHA1:
e01e3f4448205a397ce640c56eb9bdc74985b5a8
SHA256:
9C0AE5D4C840E3C5E3A6DA40B44CFCC0375DB7428968636EA681663D5681EEFD
File Size:
775.68 KB, 775680 bytes
|
|
MD5:
565243ce45f79348db686ac9235947ba
SHA1:
81566fa2ad8e24f919b99ac21e43da89fd7fbf78
SHA256:
296DEED88CF732FE8BD03027086DCC2B04BB8252B33BD2D2A919A1AFC81DE911
File Size:
347.65 KB, 347648 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have security information
- File has TLS information
- File is 64-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- imgui
- No Version Info
- WriteProcessMemory
- x64
Block Information
Block Information
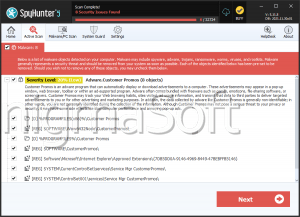
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 1,253 |
|---|---|
| Potentially Malicious Blocks: | 173 |
| Whitelisted Blocks: | 1,051 |
| Unknown Blocks: | 29 |
Visual Map
0
0
0
0
0
0
0
0
x
x
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
?
?
?
?
?
x
?
?
?
?
0
x
?
x
x
0
?
?
?
?
?
?
0
0
?
?
x
?
?
0
x
x
x
?
?
x
?
?
?
?
x
?
0
?
x
0
x
x
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
?
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
x
0
0
0
0
x
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
1
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
x
0
x
0
x
x
x
0
0
0
0
0
0
x
1
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
x
0
0
0
0
x
0
0
0
x
0
0
0
0
0
x
x
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
0
x
0
x
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
1
x
0
0
x
0
0
0
0
0
0
0
x
x
0
x
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
1
0
0
0
1
0
0
1
0
0
0
1
0
0
1
0
0
1
0
0
1
0
0
1
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
x
0
0
x
0
0
x
0
x
0
0
0
0
0
x
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
x
x
x
0
0
x
x
0
0
0
x
x
0
0
0
0
0
x
x
0
x
0
0
x
0
x
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
x
x
0
0
0
x
x
x
0
x
x
0
x
x
0
x
x
0
x
x
x
x
0
x
x
0
x
0
0
x
x
0
x
0
0
0
0
0
0
x
0
x
x
0
x
0
0
x
x
0
x
0
0
0
0
0
0
x
0
x
x
0
x
0
0
x
x
0
x
0
0
0
0
0
0
x
0
x
x
0
x
0
0
x
x
0
x
0
0
0
0
0
0
x
0
x
x
x
x
x
x
x
0
0
0
0
x
x
x
x
x
x
x
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
2
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
1
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Agent.TRG
- Gamehack.GACC
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\downloads\config\config.json | Generic Write,Read Attributes |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
65 additional items are not displayed above. |
| Keyboard Access |
|