PUP.DllInject.FSA
Table of Contents
Analysis Report
General information
| Family Name: | PUP.DllInject.FSA |
|---|---|
| Signature status: | Self Signed |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
c18dce1610625b6f48d5ecb30aa0c012
SHA1:
9b8884465c1794c3c167dc9bd1197754fec728c1
SHA256:
853A3893ACC3033A5237D6B2AAC32510D278A85F5AA016E69B3945E0C2194A9B
File Size:
1.30 MB, 1304328 bytes
|
|
MD5:
bfa1e574ef788bde08a09ffc636a75ab
SHA1:
ad7dd488098033820b488a537f8a99709dff920d
SHA256:
FDA037638538CC1D9202DB5041E68CF02063742256F3D7E6138B3BC0C48A0189
File Size:
1.30 MB, 1301768 bytes
|
|
MD5:
3285b05fc0a63716daf4c2555f402ae9
SHA1:
561e5fb82726fe53f8f4912ad8cd0bfaa5ad1c66
SHA256:
393555AD54F4193F1E363CD770F3FD7BEC8A724831040568D4A76C0110206DCD
File Size:
1.30 MB, 1304328 bytes
|
|
MD5:
82c0ef4d010d0d503c93eac5c2c9810d
SHA1:
43f4a07de81c03a97d8c673379550c0ea0ba5ccb
SHA256:
C3AAC472158849B80FCFF95E6DA6CBA4C6F9C0CC7A307F6BD8112CDF0D22B053
File Size:
1.31 MB, 1308424 bytes
|
|
MD5:
8ed9d3023ceb0f2309f2b87e6c079d63
SHA1:
c54e925ed5134d016da967aebbbc8469eb6f99b5
SHA256:
E01FC41C619FBCE47C1D383A737CA200EB6A7E8FBA2F581DDF0D5904255176EA
File Size:
1.31 MB, 1308936 bytes
|
Show More
|
MD5:
f8b8cc1764a39e580a6559cf2498793a
SHA1:
bc887089e4a28a87143e19b7f9d67b236b4bcc84
SHA256:
731F4E310A36044587209AF68677E8A85BC766694003173CC76881E62F8ED523
File Size:
1.31 MB, 1309448 bytes
|
|
MD5:
30c79893c19e1d585e72c1793b19af9d
SHA1:
ada3b62dc0a45b299edb5bda3d1f62bc7fc3f052
SHA256:
E3F894CA1868D4DD9C8A0CF03BD00BB4268359B05FEAABAC640F753F7EF980BA
File Size:
1.31 MB, 1309448 bytes
|
|
MD5:
a959be687e6065f97d72fe7b76cbb014
SHA1:
4beca9a0f025e83eaa5748004f26e5e0817a57c2
SHA256:
B1331F69782149D175C966381BF03B656570A1FCB6F2854F7B9FDADA72588A97
File Size:
1.31 MB, 1312008 bytes
|
|
MD5:
312746de805dc64b1ab7fcf9f4c0f1ec
SHA1:
23f28f0abc2227177f8fce565c02ec2f50ec744b
SHA256:
473032C443307738FA01A2DC1D636C81F7B2DEF5D48D0DDE91B0B896230BC83B
File Size:
1.31 MB, 1311600 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have relocations information
- File is .NET application
- File is 64-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Assembly Version | 1.0.0.0 |
| Comments | Solara V3 UI |
| Company Name | CMD Softworks |
| File Description | Solara V3 |
| File Version | 3.0.0.0 |
| Internal Name | Solara.exe |
| Legal Copyright | Copyright © CMD Softworks 2026-2027 |
| Original Filename | Solara.exe |
| Product Name | Solara V3 Interface |
| Product Version | 3.0.0.0 |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| CMD Softworks | CMD Softworks | Self Signed |
| CMD Softworks LLC | SSL.com Code Signing Intermediate CA RSA R1 | Self Signed |
File Traits
- .NET
- x64
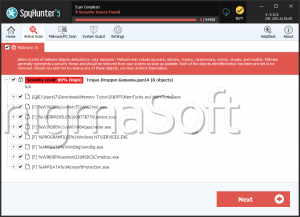
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 216 |
|---|---|
| Potentially Malicious Blocks: | 68 |
| Whitelisted Blocks: | 133 |
| Unknown Blocks: | 15 |
Visual Map
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
0
0
0
?
x
0
?
0
0
x
0
0
0
?
0
0
x
x
x
0
0
0
x
x
x
x
0
x
0
0
x
x
0
0
0
0
x
0
0
0
x
0
x
?
x
0
0
0
x
x
0
0
0
0
x
0
0
0
0
?
?
0
0
0
0
x
0
x
0
x
x
x
x
x
x
x
0
0
x
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
x
0
x
?
0
x
?
0
0
0
0
x
0
0
x
0
0
0
0
0
0
0
0
x
0
?
0
?
0
x
0
x
?
0
0
0
0
0
0
x
0
0
?
0
x
0
x
0
?
0
x
0
x
0
x
0
x
0
x
0
0
0
x
x
x
?
0
x
0
?
0
x
0
x
0
x
0
0
0
x
0
x
0
x
0
x
0
0
x
0
x
0
x
0
x
0
x
0
x
0
x
0
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- DllInject.FSA
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| User Data Access |
|
| Encryption Used |
|
| Anti Debug |
|