PUP.2144FlashPlayer.A
Table of Contents
Analysis Report
General information
| Family Name: | PUP.2144FlashPlayer.A |
|---|---|
| Signature status: | Root Not Trusted |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
e400395470358a98935615d36ff68088
SHA1:
c9ad86855849e5031a12d959df892bb97ceaf077
SHA256:
AECC18AB0E4D5D5F3292E104AC04E59245C8567AB223EC0108E910D383FE4B23
File Size:
6.69 MB, 6689696 bytes
|
|
MD5:
577d1687c0ba42b08453946ceee63528
SHA1:
0520cdad71ee5118841803acd9c65f217dff813f
SHA256:
FFC40AB507D20EF5A190F2C984E7DBD622543DD6D7D41FC4F5224C6EBB6C63C6
File Size:
6.68 MB, 6681504 bytes
|
|
MD5:
2d10cfbb37f45212f312fe82243f4f53
SHA1:
1c9b0b7a4e9bc9c2451dcfdbcfa20f17baa29358
SHA256:
808626210FB548383C598343B8F36108921ADDB37C95927F3421613519E45C15
File Size:
2.32 MB, 2317384 bytes
|
|
MD5:
085bbfb993d30c00437e5f2fbec155c6
SHA1:
afb6c31ac4e38fec6f31af992031b532f0c86e17
SHA256:
426CE23414045C93004161F73A05E650D447F69A5317DF613E905441D1F2B149
File Size:
6.69 MB, 6689696 bytes
|
|
MD5:
835fa8ee21cc5584c3cc587182cc7c9b
SHA1:
5eea4fa2decfb737ea45edb0af06c05e361830d6
SHA256:
F0BF6115F97EB8F15CEAF5AA210DAB38C97AB0199760A66DEEE0B2106F53CF25
File Size:
6.68 MB, 6681504 bytes
|
Show More
|
MD5:
723d375c5d7cdcfb86c3077ffabe745d
SHA1:
9499116098698e2a5a957aba811ccfa1caf0534d
SHA256:
EC45F58DC204A5D3693BC881CA277B47A2A46BE12CD161D59809C933312B3B36
File Size:
6.68 MB, 6681504 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File has been packed
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | Adobe Inc |
| File Description | Adobe Download Manager |
| File Version |
|
| Internal Name | Adobe Download Manager |
| Legal Copyright |
|
| Original Filename | Adobe Download Manager |
| Product Name | Adobe Download Manager |
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Adobe Inc. | DigiCert Trusted G4 Code Signing RSA4096 SHA384 2021 CA1 | Self Signed |
| Chongqing Zhongcheng Network Technology Co. Ltd. | DigiCert Trusted G4 Code Signing RSA4096 SHA384 2021 CA1 | Self Signed |
| Chongqing Zhongcheng Network Technology Co. Ltd. | DigiCert Trusted Root G4 | Root Not Trusted |
| Chongqing Zhongcheng Network Technology Co. Ltd. | DigiCert Trusted Root G4 | Root Not Trusted |
File Traits
- 2+ executable sections
- Adobe Installer
- HighEntropy
- packed
- PECompact v2.20
- WriteProcessMemory
- x86
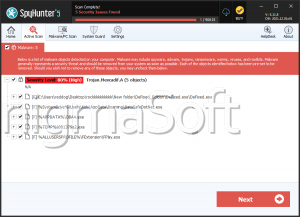
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 10,007 |
|---|---|
| Potentially Malicious Blocks: | 574 |
| Whitelisted Blocks: | 9,303 |
| Unknown Blocks: | 130 |
Visual Map
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
x
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
x
x
x
x
x
0
0
x
x
x
x
x
x
x
x
x
x
x
x
0
x
?
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
x
x
x
x
0
x
0
x
x
x
x
x
x
0
0
x
x
x
0
0
x
0
0
x
x
x
0
x
x
0
x
x
x
x
x
x
x
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
x
x
0
x
x
0
0
0
x
0
0
0
0
1
0
0
0
x
0
0
0
0
x
?
0
0
0
x
x
x
0
0
x
0
0
x
x
0
x
x
x
x
0
x
x
x
x
0
x
x
x
x
x
0
0
0
0
x
x
x
x
x
x
x
x
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
0
x
x
0
0
0
0
0
x
0
x
x
0
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
x
?
0
0
x
x
x
0
x
x
x
0
0
x
x
0
0
x
x
0
0
0
0
0
0
0
0
x
?
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
0
x
x
x
x
x
x
x
x
x
x
x
x
x
0
x
x
0
x
x
x
0
x
x
x
x
x
0
?
x
x
x
x
x
?
?
x
?
0
x
x
x
0
0
x
0
0
x
0
x
x
?
?
?
?
?
x
x
x
x
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
?
0
0
0
0
0
0
0
0
0
0
?
x
?
0
x
?
x
x
x
x
x
x
x
x
x
x
x
0
0
0
0
0
x
0
x
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
x
0
?
0
?
0
x
?
x
?
x
x
0
x
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
x
0
0
0
0
0
?
?
0
0
0
0
0
0
0
x
0
x
x
x
0
0
x
0
0
x
x
x
0
0
0
x
x
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
x
0
0
0
0
0
x
0
0
?
0
?
x
x
x
x
x
x
x
x
x
0
0
x
x
x
x
0
x
x
x
x
x
x
x
x
x
x
x
0
x
x
x
0
?
?
x
x
0
x
x
x
x
x
0
x
x
x
0
x
x
x
0
x
x
x
0
x
x
0
0
0
0
0
0
0
x
0
?
0
0
0
0
0
0
0
0
x
x
x
x
x
x
x
0
x
x
0
x
x
x
x
0
x
x
0
x
x
x
x
0
x
0
x
x
?
?
x
x
x
?
?
x
0
x
0
?
x
0
0
x
x
x
0
0
0
0
0
0
0
0
0
0
x
0
x
x
x
x
x
x
0
x
x
0
x
x
x
0
x
x
x
x
x
x
0
x
x
x
x
x
x
x
x
?
?
x
x
x
x
0
x
0
x
0
0
x
0
0
0
0
0
0
?
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
x
1
x
0
0
x
x
x
?
x
0
0
0
x
0
0
0
0
0
0
0
0
0
0
x
0
0
x
x
x
x
x
x
x
x
x
x
0
x
0
x
x
x
x
0
?
x
0
x
0
?
x
?
?
?
0
0
?
?
x
?
0
x
0
x
?
x
0
0
0
0
x
?
x
x
x
x
x
x
x
x
x
0
x
x
?
x
x
x
x
x
?
?
x
0
?
x
x
0
?
?
0
0
x
?
0
x
?
x
x
?
0
x
?
x
?
x
?
x
x
0
?
x
x
x
x
x
x
x
?
x
x
0
x
x
x
x
x
x
x
x
x
?
?
?
?
?
x
0
0
x
?
x
x
0
x
?
x
?
0
x
x
x
x
x
x
x
0
x
0
x
x
0
x
0
0
0
x
0
0
x
?
?
x
x
x
x
x
0
x
0
x
?
x
x
x
x
x
?
?
x
?
?
0
x
x
x
?
x
x
x
x
x
?
x
x
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
0
x
x
x
0
0
0
x
0
0
x
0
0
0
x
x
0
0
0
0
0
x
0
x
0
x
x
0
0
x
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
x
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
x
0
x
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
x
x
x
0
0
0
0
0
0
0
0
x
x
x
0
0
0
x
x
x
x
x
0
x
0
x
x
0
x
x
0
x
0
x
0
0
0
0
x
x
0
0
x
x
0
0
0
0
x
0
x
x
x
0
0
0
x
0
x
x
0
x
x
0
0
x
x
0
0
x
x
0
x
0
x
x
x
x
0
x
0
0
0
x
0
x
0
0
x
0
0
0
x
0
0
x
x
x
x
0
x
x
0
x
x
x
x
x
x
x
0
x
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
x
0
0
0
x
x
x
0
0
x
0
x
x
x
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
x
0
x
0
0
x
0
x
0
x
0
0
0
0
x
x
0
0
x
x
0
0
0
x
x
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
x
x
x
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
1
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
x
0
x
0
x
x
x
0
0
x
0
0
0
0
0
x
0
0
x
x
0
0
0
x
x
x
x
0
x
0
0
x
0
0
x
0
0
x
x
0
0
0
0
0
0
0
0
0
0
?
?
?
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
...
Data truncated
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- 2144FlashPlayer.A
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\adobe_cdmlogs\adobe_cdm.log | Generic Write,Read Attributes |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Anti Debug |
|
| User Data Access |
|
| Other Suspicious |
|