ONFIND Browser Extension
Installing browser hijackers unknowingly can expose users to significant risks, compromising their browsing experience and online security. These unsafe extensions often alter browser settings and redirect users to deceptive websites, posing threats to privacy and exposing users to potentially harmful content.
Table of Contents
A Review of ONFIND: A Browser Hijacker Analysis
ONFIND, identified by information security researchers, operates as a browser hijacker upon installation. It manipulates browser settings to promote findflarex.com, a fake search engine. Despite claims of enhancing the browsing experience, ONFIND undermines user trust by redirecting searches to unreliable sources.
Findflarex.com, the promoted search engine by ONFIND, does not deliver genuine search results. Instead, it redirects users to boyu.com.tr, a dubious search engine known for unreliable and potentially unsafe content. This includes links to sites offering shady products, adult content, technical support tactics, and misleading information.
- Potential Exposure to Untrustworthy Content: Search results from boyu.com.tr may lead users to websites hosting additional browser hijackers, adware or even malware. These results often feature misleading advertisements, further jeopardizing user security and privacy. Trusting such search engines can lead to inadvertent exposure to harmful software and fraudulent schemes.
- Data Privacy Concerns with ONFIND: ONFIND not only manipulates browsing behavior but also collects sensitive user info, including browsing history, search queries and frequently visited websites. This data harvesting raises significant privacy concerns as it may be sold to third parties or utilized for targeted advertising, exacerbating the risks associated with using the extension.
- Impact on Browser Management: Adding ONFIND may enable the 'Managed by your organization' feature in browsers, indicating external control over browser settings. This capability can restrict access to certain websites, compromise user privacy, and lead to unintended interactions with other extensions. Such control enhances the potential for security vulnerabilities and undermines user autonomy online.
Distribution Tactics of Potentially Unwanted Programs (PUPs)
PUPs utilize a variety of cunning strategies to infiltrate user systems, often catching unsuspecting individuals off guard. These distribution tactics are carefully designed to exploit common user behaviors and technical weaknesses, facilitating their unauthorized access to browsers and compromising user security and privacy.
- Bundling with Free Software: One of the most prevalent methods used by PUPs is bundling with legitimate free software downloads. When users download and install popular software from trusted sources, PUPs piggyback onto these installations unnoticed. Often, the bundled PUPs are included in the installation package with misleading or buried opt-out options, tricking users into unintentionally agreeing to their installation.
- Misleading Advertisements: PUPs also distribute using misleading advertisements. These advertisements can appear legitimate and promise useful software updates, system optimizations, or free tools. Clicking on such ads may lead users to websites that automatically initiate downloads of PUPs, exploiting user curiosity or desire for enhanced functionality.
- Disguised Download Links on Websites: On websites that offer downloads for software, media, or other content, PUPs may camouflage their download links to mimic legitimate options. Unsuspecting users may inadvertently click on these disguised links, thinking they are downloading the desired content, only to end up with PUPs being installed on their systems instead.
- Exploiting User Trust: PUPs often exploit user trust in reputable brands or well-known software developers. They may create fake websites or impersonate legitimate software providers, convincing users to download and install their malicious software under the guise of obtaining trusted applications or updates.
Mitigating the Risks
To mitigate the risks associated with PUPs, users should adopt proactive measures:
- Exercise Caution When Downloading Software: Always download software from official websites or trusted sources. Read all installation prompts carefully and opt out of any additional software bundled with the desired program.
- Be Cautious of Ads and Pop-ups: Avoid clicking on suspicious advertisements or pop-ups offering free downloads or system optimizations. Before downloading any software, verify the legitimacy of the source.
- Keep Software Updated: Regularly update software and operating systems to patch known vulnerabilities that PUPs might exploit. Enable automatic updates where possible to ensure timely security fixes.
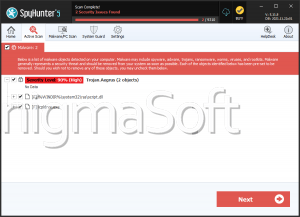
- Use Security Software: Install reputable anti-malware software that can detect and block PUPs before they can infiltrate your system. Regularly scan your system for potential threats.
By remaining vigilant and informed about the tactics used by PUPs, users can better protect their systems and personal data from these intrusive and potentially harmful programs.