Malware & Chinese Open-Source Tool is at the Heart of the Second DNC Hack
Hackers Used a Decade Old Protocol to Spark a Massive DNC Scandal
 On June 15, the Democratic National Committee (DNC) announced that its computer network had been the target of not one, but two cyber attacks in the span of less than a year. The first one started in 2015, and it gave hackers access to communication between party officials. In April, people looking for a research file on Donald Trump compromised the Democrats' system once again. A great deal of sensitive information was released to the public, which led to quite a lot of tension within the Democratic party. Certain people lost their jobs, and others accused the DNC of favoring Hillary Clinton over Bernie Sanders.
On June 15, the Democratic National Committee (DNC) announced that its computer network had been the target of not one, but two cyber attacks in the span of less than a year. The first one started in 2015, and it gave hackers access to communication between party officials. In April, people looking for a research file on Donald Trump compromised the Democrats' system once again. A great deal of sensitive information was released to the public, which led to quite a lot of tension within the Democratic party. Certain people lost their jobs, and others accused the DNC of favoring Hillary Clinton over Bernie Sanders.
Naturally enough, security experts were quickly called in to investigate the breach and find out what had happened exactly. The focus was put on the perpetrator. First, a research firm called CrowdStrike said that COZY BEAR and FANCY BEAR, two groups of hackers linked to the Russian government, stand behind the attacks. Then, a rogue hacker who calls himself Guccifer 2.0 (believed to be from Romania) announced that he was responsible. Later, experts said that there might be a link between Guccifer 2.0 and Russia's intelligence. Despite all the speculation, nobody can say with absolute certainty whether Russia really is involved in the attacks. That's why, when another security firm called Invincea started investigating the breach from April, they decided to focus on the malware itself rather than on its creator.
The experts found out that the hackers used a spyware program called X-Agent to infiltrate the system and then employed a custom-built piece of software codenamed X-Tunnel to pump out the all important data. X-Tunnel is a pretty nasty program. It uses a file called vmupgradehelper.exe, which is less than 2MB in size. Invincea said that it can:
- Open SSH connections
- Steal passwords
- Download and upload files
- Capture mouse movements
X-Tunnel is capable of doing many other things, but according to Invincea, its characteristics suggest that its main goal is data exfiltration. The malware's impressive capabilities meant that the damage it caused was huge. What is interesting, however, is that it didn't employ some state-of-the-art technology. Instead, it used a protocol that is now more than ten years old.
Image 1. X-Tunnel PortMap
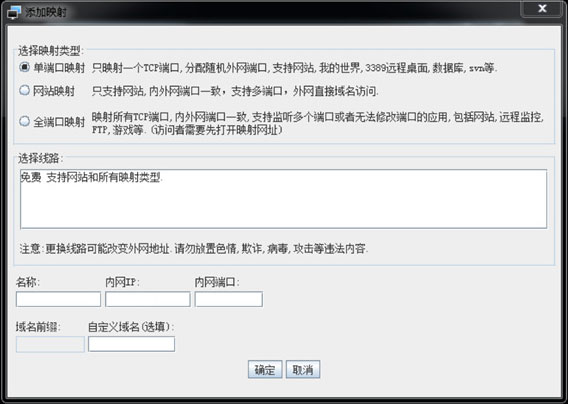
X-Tunnel was named after the XTunnel protocol, which came into existence for all the right reasons. Back in 2004, when VoIP communication was coming into its stride, applications like Skype were looking for available connection ports and were being blocked by Firewalls. This meant that administrators were forced to manually open ports, which was a lot of work. XTunnel eliminated the need for human intervention. It would establish a connection by checking all the ports and hooking up with the first available one. Researchers at Invincia reckon that the X-Tunnel malware is a modified version of Xtunnel PortMap – an open-source project that used the aforementioned protocol and was developed by a Chinese company called Xten.
This simple yet robust technology made the lives of many people easier back in 2004. Twelve years later, it made the detection of the X-Tunnel malware extremely difficult, and it led to a scandal of epic proportions.