igHome.com
Protecting devices from intrusive and untrustworthy PUPs (Potentially Unwanted Programs) is essential for maintaining digital privacy and system stability. Applications that appear harmless at first glance often introduce unwanted changes, expose users to unreliable content, and compromise browsing security. One example is igHome.com, a dubious search engine that is typically promoted through an intrusive browser hijacker.
Table of Contents
igHome.com: A Search Engine in Name Only
Cybersecurity analysis of igHome.com reveals that it functions as a fake search engine. Although it presents itself as a legitimate search provider, it does not generate independent search results. Instead, when users submit a query, they are redirected to search.yahoo.com, a well-known and legitimate search engine. This behavior indicates that igHome.com serves primarily as an intermediary rather than a genuine search service.
While redirection to a legitimate provider may appear harmless, the involvement of a suspicious intermediary raises serious concerns. igHome.com may also reroute users to unreliable search engines or other questionable websites depending on various factors, such as location or browsing profile. Such redirections increase exposure to deceptive pages that promote shady software, phishing schemes, fraudulent services, or malware-laden downloads.
Exposure to Misleading Content and Privacy Risks
Beyond its lack of original search functionality, igHome.com presents additional risks related to data tracking and online safety. Fake search engines of this kind may collect browsing-related information, including search queries, visited URLs, IP addresses, and other technical details. This harvested data could be used for targeted advertising, shared with third parties, or potentially exploited for malicious purposes.
Moreover, users redirected through igHome.com could encounter pages designed to harvest sensitive data such as login credentials or financial information. These sites may also display deceptive advertisements, promote fake technical support services, or attempt to convince visitors to purchase unnecessary products. As a result, continued interaction with igHome.com significantly increases the likelihood of falling victim to scams or other cyber threats.
The Role of Browser Hijackers
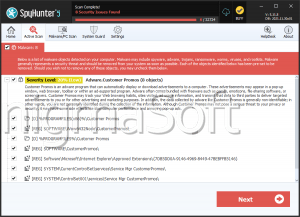
igHome.com is commonly distributed and enforced through browser hijackers, intrusive extensions or applications designed to manipulate browser settings. Once installed, such hijackers typically alter the default search engine, homepage, and new tab address to ensure that traffic is routed through the promoted site.
These modifications may not be easily reversible. Browser hijackers are often engineered to restrict access to certain settings or automatically reapply unwanted changes after manual attempts at restoration. As long as the hijacker remains active, users may find themselves repeatedly redirected to igHome.com despite efforts to remove it. This persistence underscores the intrusive nature of such PUPs.
If igHome.com or a related hijacker is detected within a browser, prompt removal is strongly advised to prevent ongoing data exposure and unwanted redirections.
Questionable Distribution Tactics Behind PUPs
PUPs associated with igHome.com rely on deceptive distribution strategies to infiltrate devices. One of the most prevalent techniques is software bundling. In these cases, the hijacker is packaged alongside free or questionable programs and installed silently when users proceed with default installation settings. The option to decline additional components is often hidden within 'Advanced,' 'Custom,' or similarly labeled setup configurations, which many users overlook.
Intrusive applications may also be spread through misleading pop-ups, fake system alerts, and deceptive advertisements hosted on untrustworthy websites. These messages frequently claim that urgent updates or security tools are required, prompting users to download software that introduces the hijacker instead.
Additional distribution channels include unofficial application stores, peer-to-peer networks, third-party download managers, unreliable browser notification prompts, and counterfeit websites imitating legitimate services. These sources may disguise intrusive software as useful tools, increasing the chances of accidental installation.
Final Assessment
igHome.com is a deceptive search engine that fails to provide authentic search results and instead redirects users to external providers. Its association with browser hijackers, potential data collection practices, and exposure to unreliable or malicious websites make it untrustworthy. Since intrusive PUPs may alter browser settings, track browsing activity, and promote deceptive content, their presence should be addressed without delay. Removing igHome.com and any related hijacking components is a necessary step toward restoring secure and private browsing conditions.