Getfastbrowser.download
Protecting your devices from intrusive and untrustworthy applications is no longer optional, it is essential. Potentially Unwanted Programs (PUPs) may seem harmless at first glance, but they could interfere with browser settings, expose you to deceptive content, and weaken your overall security posture. One recent example raising concerns is Getfastbrowser.download, a dubious page frequently associated with intrusive browser hijacker activity.
Table of Contents
What Is Getfastbrowser.download?
Getfastbrowser.download is a suspicious webpage that typically appears when a user's browser session has been tampered with. If Google Chrome suddenly begins redirecting new tabs, or even well-known websites, to this domain, it strongly suggests the presence of a browser hijacker.
The page commonly displays a message implying that your current browser is outdated or unsupported. It then funnels visitors toward downloading another browser, often promoting Opera. In many cases, the site mimics a compatibility warning and may even interrupt login sessions, creating a false sense of urgency.
While the promoted browser itself may be legitimate, the method used to push it is highly questionable. Legitimate software vendors do not rely on forced redirects or deceptive compatibility alerts.
Why Chrome Is Targeted – Signs of a Compromised Profile
If major websites open normally in Incognito mode or in another browser such as Microsoft Edge, but redirect in regular Google Chrome sessions, this typically indicates a modified Chrome profile.
In most cases, the issue stems from:
- A rogue browser extension
- Manipulated site permissions
- Altered notification settings
- Corrupted or hijacked browser configuration files
Reinstalling Chrome alone often does not resolve the problem. Chrome profiles sync data across devices, meaning unwanted settings could return after reinstallation if synchronization remains enabled. Persistent profile modifications may continue triggering redirects even after a fresh install.
How PUPs Spread – Deceptive Distribution Tactics
One of the most concerning aspects of PUP-related threats is how they infiltrate systems in the first place. These programs rarely rely on transparent installation methods. Instead, they exploit manipulative distribution strategies, such as:
Software Bundling
Free software packages downloaded from third-party platforms frequently include optional components pre-selected for installation. Users rushing through setup without reviewing advanced or custom options may unintentionally authorize additional applications.
Fake Update Prompts
Deceptive pop-ups claiming that your browser or media player is outdated may redirect to pages like Getfastbrowser.download. These prompts may appear convincing but often originate from malicious advertising networks.
Misleading Compatibility Warnings
Some hijackers inject scripts that display fabricated 'unsupported browser' alerts. These messages could interrupt normal browsing and create urgency, pushing users toward unnecessary downloads.
Notification Permission Abuse
Certain websites trick users into clicking 'Allow' on notification requests. Once granted, these permissions may be abused to generate intrusive redirects, persistent pop-ups, or misleading system alerts.
Collectively, these tactics blur the line between user consent and manipulation, allowing PUPs to embed themselves into browsers without clear authorization.
How to Remove Getfastbrowser.download Redirects
If you are experiencing forced redirects in Chrome, follow these structured steps:
- Inspect Chrome Extensions
Type the following into your address bar:
chrome://extensions
Carefully review installed extensions and remove anything unfamiliar or suspicious.
- Clear Suspicious Notification Permissions
Navigate to:
Settings → Privacy and Security → Site Settings → Notifications
Under the 'Allowed' section, remove unknown or suspicious entries. In many cases, clearing rogue notification permissions immediately stops redirect loops.
- Reset Chrome Settings
If the issue persists:
Settings → Reset settings → Restore settings to their original defaults
This action reverts startup pages, search engines, pinned tabs, and other modified configurations.
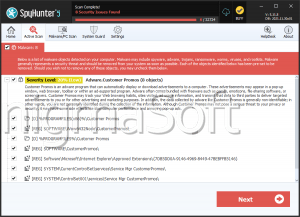
- Run a Reputable Security Scan
A full system scan using trusted security software is strongly recommended. Browser hijackers may leave behind residual components or registry modifications that manual removal does not address.
Prevention: Avoiding Future Browser Hijacks
To reduce the risk of encountering similar threats:
- Download browsers and software only from official vendor websites or trusted app stores.
- Avoid interacting with sudden 'unsupported browser' or urgent update pop-ups.
- Choose 'Custom' or 'Advanced' installation modes when installing freeware.
- Regularly audit installed extensions and notification permissions.
- Keep a reliable security solution active and updated.
Final Thoughts
Getfastbrowser.download is not a legitimate system requirement but rather a symptom of browser manipulation. While it attempts to present itself as a helpful compatibility solution, its behavior aligns with intrusive PUP-driven redirect schemes.
Users who remain vigilant about installation practices, browser permissions, and system hygiene significantly reduce their exposure to these disruptive and potentially risky threats.