Emotet Malware Uses US Election Campaign as Bait
 The notorious malware distribution vehicle Emotet has been back in business for a little over two months following a long break earlier this year. The subject line of one of the latest waves of Emotet emails is "Team Blue Take Action" and that’s also the name of the malicious file attachment.
The notorious malware distribution vehicle Emotet has been back in business for a little over two months following a long break earlier this year. The subject line of one of the latest waves of Emotet emails is "Team Blue Take Action" and that’s also the name of the malicious file attachment.
The body of the email contains texts taken word for word from pages on the website of the Democratic National Committee. The only original content is a line asking the reader to open the attachment.
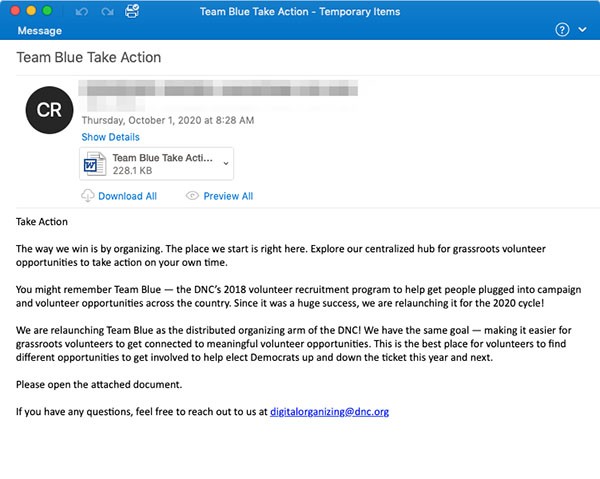
Example of malicious email with Emotet-infected attachment - Source: Proofpoint.com
The file is a word document containing a malicious macro. If the recipient tries to open it, they will be prompted to enable macros unless macros have been previously enabled. Once macros are allowed to run Emotet will be downloaded and it will infect the device. This Emotet campaign seems to carry Qbot "partner01" and The Trick as next stage payloads.
Researchers from Proofpoint have also observed other subject lines with corresponding attachment file names used in the current Emotet campaign:
- Valanters 2020
- Detailed information
- List of works
- Volunteer
- Information
The main infection vector for Emotet has always been phishing campaigns leveraging hot topics of the day. So seeing the cybercriminals use the presidential election campaign as bait directly following the first debate shouldn’t come as a surprise, except Emotet hadn’t used political themes in phishing campaigns before.
Emotet's operators took a five month break from March to July 2020. Since they've been back Emotet has been the dominant tool for malware distribution. This frantic activity has attracted a lot of attention from the cyber security community. At least five national computer emergency response teams from around the world have issued warnings about Emotet in the past couple of months. Emotet is not showing any signs of slowing down in the foreseeable future.