Dealio Toolbar
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 7,763 |
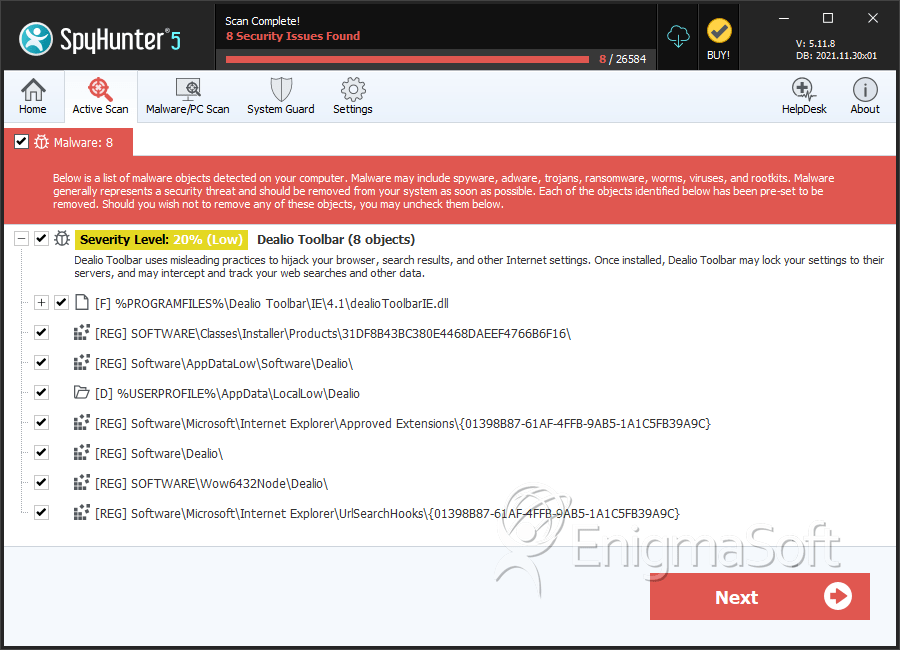
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 5,724 |
| First Seen: | July 24, 2009 |
| Last Seen: | June 8, 2026 |
| OS(es) Affected: | Windows |
Dealio Toolbar is an add-on for popular web browsers that may display repeated and annoying advertisements attempting to offer deals and coupons on online shopping. Dealio Toolbar is known for also changing the default search engine page and default home page of popular web browsers. The installation of Dealio Toolbar may come from various bundled programs downloaded on file sharing sites and those that offer freeware and shareware applications. When loaded, Dealio Toolbar may also attempt to offer other internet services through shortcut buttons. The Dealio Toolbar is not a virus by itself but has the tendency to be a serious annoyance for computer users who want to restore their internet settings to load their preferred home page by default. The removal of Dealio Toolbar and its components may involve using an updated antispyware tool.
Table of Contents
Aliases
5 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| Sophos | Dealio Installer |
| McAfee | Artemis!4AC870C6DA03 |
| NOD32 | Win32/Adware.Toolbar.Dealio |
| McAfee+Artemis | Artemis!DF13B8F5A476 |
| Comodo | Unclassified Malware |
SpyHunter Detects & Remove Dealio Toolbar
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | iobitToolbarIE.dll | d6e6c591e43f17981cd32eeb792742a3 | 741 |
| 2. | WidgiHelper.exe | 77b1b2b4bacd122a78bb58ac56f897ed | 98 |
| 3. | file.exe | b32ca052601c77a68056c5f342f8f6f2 | 8 |
| 4. | Dealio Deskbar.exe | df13b8f5a476b1022c5730eec66b4515 | 2 |
| 5. | free-msn-emoticons-pack-01-ingles.exe | 4ac870c6da035d325b14f8325101ae5b | 2 |
Registry Details
Directories
Dealio Toolbar may create the following directory or directories:
| %ProgramFiles%\Dealio Toolbar |
| %ProgramFiles(x86)%\Dealio Toolbar |
| %USERPROFILE%\AppData\LocalLow\Dealio |
| %USERPROFILE%\Application Data\Dealio |
Analysis Report
General information
| Family Name: | Dealio Toolbar |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
7ab56e258740eb951eae6f28f588bc6a
SHA1:
cd01b618616ddb1596bbacf1552be35e9f1d9432
SHA256:
B75AD9FC24D8E737C9FB9035C9E5ADD878489EAB3212A2341AC12A484753AEF4
File Size:
2.39 MB, 2391415 bytes
|
|
MD5:
5d736ed41ade0080627738865924d35c
SHA1:
e0d4ebfd0d27f312ca26ee87054509a21698e79f
SHA256:
B5B7EAA3351BF81CEDA43016953B0E6A6834EF02377FCAD9633FC08E3F2A4636
File Size:
9.05 MB, 9049552 bytes
|
|
MD5:
a0109806f86c0e3e9426493f0222b69f
SHA1:
9606127a39654246e978864eb6a1aecda48c5920
SHA256:
A7BD724E73CA6A39128DDDE1C9944AF2B9D5805965FD487D919E72EC71C911AC
File Size:
4.18 MB, 4175089 bytes
|
|
MD5:
1bebf3f7ffdce057fbf3aba6944e3017
SHA1:
c909c7321d60ae2297e046ea9018ab19354f4c86
SHA256:
7C1AA7FBDC350C1415CCFD2ECE058B1C98CCA78E00F58E4BD018326AF70DBA74
File Size:
7.06 MB, 7056272 bytes
|
|
MD5:
ff2a09860a0be80a2660fa2642bf96b1
SHA1:
57a3cdb46740f158e70735de7f533ecb2caa298d
SHA256:
597C2D673814CFE3094CCB65FE64D480885F178BF11B94DED450C461A2D9A9C8
File Size:
3.09 MB, 3086482 bytes
|
Show More
|
MD5:
b33b30f0766b5bcf2908f94622336f5d
SHA1:
64a73db3b210abeac5ef18efc240099740cc0eed
SHA256:
EF9F8C83B6A4CB487570346BEBE78192A74D2EBCEE74A00DEB664695A7BB7E60
File Size:
2.73 MB, 2734800 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments |
|
| Company Name |
|
| File Description |
|
| File Version | 2.5.0.0 |
| Legal Copyright |
|
| Product Name | Free Video Converter |
| Product Version | 2.5.0.0 |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| AVSOFT CORP. | VeriSign Class 3 Code Signing 2010 CA | Self Signed |
File Traits
- HighEntropy
- Installer Manifest
- Installer Version
- WriteProcessMemory
- x86
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| \device\namedpipe\gmdasllogger | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\dealio_install02.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\dealiotoolbar-stub-1.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\dvdmmg.sys | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\iod.ini | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsg232a.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
| c:\users\user\appdata\local\temp\nsg232b.tmp\dealio_install.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsg232b.tmp\installoptions.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsg232b.tmp\iospecial.ini | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\nsg232b.tmp\iospecial.ini | Generic Write,Read Attributes |
Show More
| c:\users\user\appdata\local\temp\nsg232b.tmp\modern-wizard.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nshbc9b.tmp\langdll.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\installoptions.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\iod.ini | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\iod.ini | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\iospecial.ini | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\iospecial.ini | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\modern-header.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\modern-wizard.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\security.ini | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\nsm15d1.tmp\security.ini | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsw15c0.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
| c:\users\user\appdata\local\temp\wizesupp.dll | Generic Write,Read Attributes |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Process Manipulation Evasion |
|
| Anti Debug |
|
| User Data Access |
|