Claim GFOX Tokens Scam
Engaging with cryptocurrency offers requires utmost caution due to the prevalence of tactics and fraudulent activities. Recently, an examination of the page (galaxyfoxclaim.pages.dev) revealed it to be a fraudulent website imitating the legitimate Galaxy Fox platform (galaxyfox.io). This deceptive site, known as the Claim GFOX Tokens scam, aims to deceive unsuspecting users into financial losses through cleverly crafted tactics.
Table of Contents
Mimicking a Legitimate Platform
The fake website galaxyfoxclaim.pages.dev closely mimics the appearance and functionality of the authentic Galaxy Fox platform (galaxyfox.io). This includes replicating the design, features, and even the cryptocurrency associated with it, such as the Galaxy Fox token ($GFOX). Fraudsters use this deception to lure visitors into believing they are interacting with the real platform.
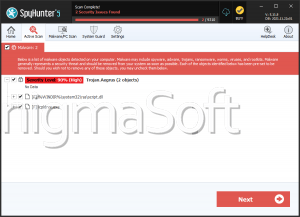
Activation of Cryptocurrency Drainer
Upon visitors connecting their cryptocurrency wallets on galaxyfoxclaim.pages.dev, a harmful cryptocurrency drainer is activated. This sophisticated tool is designed to automatically transfer cryptocurrency from the victim's wallet to the fraudster's account without the victim's knowledge or consent. This unsafe act can result in significant financial losses for the victim.
Irreversible Consequences and Recovery Challenges
It's crucial to understand that transactions involving cryptocurrency, once executed, are typically irreversible. Suppose the funds are sent to a mistaken address or collected through tactics like the fake Galaxy Fox website. In that case, recovery is exceedingly difficult or impossible without the cooperation of the recipient. Victims often find themselves unable to retrieve lost cryptocurrency, leading to severe financial consequences.
Importance of Verifying Platform Authenticity
Given the risks associated with cryptocurrency transactions, users must verify the authenticity of platforms before connecting their wallets or engaging in financial transactions. This involves conducting thorough research, checking domain names, scrutinizing website URLs and ensuring the legitimacy of the entities behind the platforms. Users should only interact with well-established and reputable platforms to safeguard their assets and avoid falling victim to tactics.
Risks in the Crypto Sector
The cryptocurrency sector presents vast opportunities for investment, innovation, and financial growth, but it also harbors significant risks that users must navigate carefully. One of the most prevalent dangers is the existence of fraudulent websites and tactics, exemplified by incidents like the Claim GFOX Tokens scam. These tactics often capitalize on the anonymity and irreversible nature of cryptocurrency transactions to deceive users and collect their funds.
- Understanding the Risks: Cryptocurrency tactics can manifest in various forms, from fake ICOs (Initial Coin Offerings) and Ponzi schemes to phishing websites and unsafe software targeting crypto wallets. The Claim GFOX Tokens scam, for instance, exploited the trust users place in legitimate platforms by creating a convincing replica of the Galaxy Fox platform. Such tactics aim to trick users into divulging sensitive information or unwittingly transferring cryptocurrency to scammers' wallets.
- Importance of Platform Verification: Verifying the authenticity of cryptocurrency platforms is paramount. Users should conduct thorough due diligence before interacting with any platform, especially when it is related to financial transactions or connecting wallets. Key verification steps include checking domain names for slight variations or unusual extensions, scrutinizing website security features (such as SSL certificates), and researching the reputation and history of the platform and its operators.
Mitigating Risks and Ensuring Security
To protect themselves from tactics in the crypto landscape, users should adopt stringent security measures and best practices:
- Stay Informed: Regularly update knowledge about current tactics and new tactics used by fraudsters. Being aware of emerging threats enhances preparedness.
- Verify Transactions: Double-check wallet addresses and transaction details before proceeding with any cryptocurrency transfer. Once a transaction is initiated, it is typically irreversible, making verification crucial.
- Use Secure Wallets: Store cryptocurrencies in reputable wallets that offer powerful security features, such as two-factor authentication (2FA) and encryption. Avoid using online wallets or exchanges as permanent storage for large amounts of crypto.
- Beware of Phishing: Exercise caution with emails, messages, or websites that request sensitive information or prompt urgent actions. Verify the legitimacy of communications directly through official channels.
- Enable Security Features: Utilize browser extensions or add-ons that enhance security, such as ad-blockers, anti-phishing tools, and pop-up blockers to prevent interactions with unsafe websites.