Browsingsafety.net
Infosec analysts have classified Browsingsafety.net as a fake search engine. Unlike legitimate platforms, it does not generate its own search results. Instead, it forwards user queries to third-party websites. During examinations, it redirected searches to search.yahoo.com; however, this behavior is not guaranteed to remain consistent.
Because Browsingsafety.net merely acts as a middleman, it may also route traffic to other destinations, including unsafe or misleading pages. This redirection-based operation places users at risk of being funneled toward websites designed to exploit trust, harvest information, or promote deceptive content.
Table of Contents
The Multimedia Search Browser Hijacker Explained
Browsingsafety.net is promoted by the Multimedia Search extension, which operates as a browser hijacker. Once present, this hijacker alters critical browser settings, such as the homepage, default search engine, and new tab address, forcing users to interact with the fake search engine.
Multimedia Search may also employ mechanisms that make reversing these changes difficult, creating persistence that frustrates users attempting to restore their preferred settings. This type of interference is a hallmark of browser hijackers and signals that the software's goals do not align with user interests.
Privacy at Risk: Data Monitoring and Potential Misuse
Beyond altering browser configurations, Multimedia Search is capable of accessing browsing-related information. This means it may observe visited websites, search queries, and general online activity. Such monitoring introduces clear privacy concerns.
Data gathered in this manner could be repurposed for aggressive advertising, profiling, or more malicious objectives. When browsing habits become a commodity, users lose control over how their digital footprint is used and shared.
The Hidden Dangers Behind Redirects
Relying on Browsingsafety.net exposes users to an unpredictable browsing experience. Redirected searches might lead to pages crafted to imitate legitimate services, solicit sensitive details, pressure visitors into fraudulent payments, or distribute questionable software.
Even when redirections land on well-known engines, the fake search site still functions as an unnecessary and potentially dangerous gateway. Its presence serves no genuine benefit and introduces avoidable risk.
How PUPs Get In: Questionable Distribution Tactics
PUPs rarely announce themselves openly. Instead, they rely on deceptive and opportunistic distribution methods, including:
Software bundling: Freeware and shareware installers often include additional components. When users rush through setup processes without reviewing 'Advanced' or 'Custom' options, they unknowingly agree to install browser hijackers and similar threats.
Misleading advertisements: Fake update alerts, download buttons, and sensational banners on shady websites frequently promote unwanted extensions.
Untrustworthy sources: Unofficial app stores, peer-to-peer networks, third-party download portals, and intrusive pop-ups are common channels used to push these programs.
Social engineering: Pages may present intrusive tools as 'recommended,' 'security-related,' or 'essential,' exploiting fear or curiosity to encourage installation.
These tactics are designed to blur the line between legitimate software and intrusive add-ons, ensuring many users install them without realizing what they have accepted.
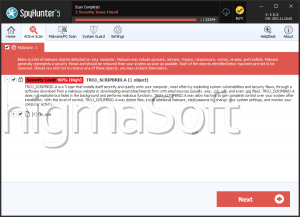
Why Immediate Removal Is Essential
If a browser repeatedly opens Browsingsafety.net, it strongly suggests that Multimedia Search is present. Both the fake search engine and the hijacker should be removed as soon as possible. Leaving them active may prolong exposure to privacy invasion, unwanted redirects, and further system modifications.
Final Thoughts: Regaining Control Over the Browser
Browsingsafety.net and the Multimedia Search hijacker illustrate how easily browsing environments may be manipulated. By staying alert during software installations, avoiding suspicious download sources, and promptly addressing unexpected browser changes, users significantly reduce their exposure to PUP-driven threats. In cybersecurity, prevention and early action remain the most effective defenses.