Anomaly Ransomware
In an era where digital threats continue to evolve, protecting devices from threatening software is more important than ever. Ransomware attacks can lead to devastating data loss, financial harm, and operational disruption. Among the latest threats, Anomaly Ransomware stands out as a harmful encryption-based attack that forces victims to pay for the recovery of their files. Understanding how this ransomware operates and adopting proactive security measures is essential in minimizing its impact.
Table of Contents
What is the Anomaly Ransomware?
The Anomaly Ransomware is a recently discovered encryption-based threat derived from the Chaos Ransomware family. Once executed on a compromised system, it encrypts stored data and demands a ransom in exchange for decryption. Unlike some ransomware variants that use a fixed extension, Anomaly appends four random characters to affected files. For instance, '1.jpg' may become '1.jpg.gsvo,' while '2.pdf' could be renamed '2.pdf.xlzj,' making it difficult to identify or restore files manually.
Ransom Demands and Threats
Following encryption, the Anomaly Ransomware modifies the desktop wallpaper and generates a ransom note titled 'read_it.txt.' This message warns victims that their files are locked and can only be recovered by purchasing a decryption key from the attackers. The ransom demand is set at 0.05 BTC (Bitcoin), which, depending on market fluctuations, can amount to thousands of dollars.
The note also includes a vague threat that delaying payment may result in permanent data loss, a common psychological tactic used to pressure victims into complying. However, cybersecurity professionals strongly discourage paying, as nothing is guaranteeing that cybercriminals will provide the necessary decryption tool even after receiving payment.
Data Recovery and Risks of Paying the Ransom
In most ransomware infections, recovering files without the attackers' involvement is impossible unless the ransomware contains encryption flaws. Unfortunately, the Anomaly Ransomware does not exhibit such vulnerabilities. The only reliable method of restoring affected files is through pre-existing backups that remain unaffected by the attack.
The ransom payment not only fails to guarantee file recovery but also fuels further cybercrime. Attackers use ransom payments to develop more sophisticated threats, targeting additional victims. Additionally, some ransomware operators may attempt follow-up attacks, assuming that victims who paid once might be willing to pay again.
How the Anomaly Ransomware Spreads
Like many ransomware threats, Anomaly is distributed through a variety of deceptive tactics, including:
- Fraudulent email attachments and links: Spam emails containing infected documents, compressed archives, or executable files may trick recipients into launching the ransomware unknowingly.
- Drive-by downloads: Visiting compromised or unsafe websites can trigger the automatic execution and download of ransomware without user interaction.
- Fake software updates and installers: Fraudulent update notifications or software download sources often bundle ransomware with legitimate-looking programs.
- Pirated software and key generators: Unauthorized software cracks frequently contain hidden malware that activates upon execution.
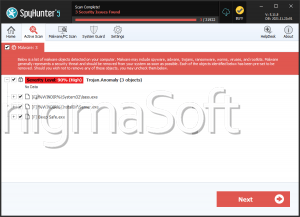
- Trojan infections: Some backdoor or loader-type trojans silently install ransomware once they infiltrate a system.
- Self-propagation methods: Certain ransomware variants spread across local networks or external storage devices, infecting multiple systems.
Best Security Practices to Prevent Ransomware Attacks
The most effective defense against ransomware like Anomaly is a proactive cybersecurity strategy. Implementing the following security measures can significantly reduce the risk of infection:
- Maintain Secure Backups: Regularly back up important files and save them in various locations, such as external hard drives and cloud-based services. Ensure that backups are disconnected from the primary system when not in use to prevent ransomware from encrypting them.
- Exercise Caution with Emails: Avoid opening unexpected email attachments or accessing links from unknown senders. Even legitimate-looking emails can contain unsafe payloads, so verify their authenticity before interacting with them.
- Keep Software Renovated: Ensure that your operating system, applications, and security software are regularly updated. Fraudsters frequently exploit vulnerabilities in outdated software to deliver ransomware.
- Use Robust Security Software: Install and maintain a reputable security suite that includes ransomware protection. Behavior-based detection can identify and block suspicious activity before encryption begins.
- Restrict Macros and Scripts: Disable macros in Microsoft Office documents and prevent unauthorized execution of JavaScript or PowerShell scripts unless absolutely necessary. Malicious macros are a standard infection method used in phishing attacks.
- Enable Network Security Controls: Firewalls, intrusion detection systems and network segmentation can help limit ransomware propagation within an organization.
- Avoid Untrusted Software Sources: Only download software from official vendors or verified sources. Avoid torrent sites, pirated software, and third-party download platforms.
- Educate Users on Cybersecurity Best Practices: Ransomware often exploits human error, so training individuals to recognize suspicious emails, links, and software can prevent infections before they occur.
The Anomaly Ransomware is a sophisticated encryption threat that locks files and demands a ransom payment in Bitcoin. While attackers claim to offer decryption in exchange for payment, there is no guarantee that victims will regain access to their data. The best course of action is to avoid paying and instead rely on secure backups for recovery.
By implementing strong cybersecurity practices, users can significantly reduce their exposure to ransomware threats. Regular backups, cautious browsing habits, software updates, and endpoint protection are key pillars of an effective defense strategy. In an ever-changing threat landscape, staying informed and proactive is the best way to mitigate the risks posed by ransomware attacks.