Almaricus Application
Protecting devices from intrusive and untrustworthy software is no longer optional, it is essential. Potentially Unwanted Programs (PUPs) often disguise themselves as harmless utilities while quietly undermining system stability and privacy. These applications may hijack browsers, flood screens with intrusive advertisements, consume excessive system resources, and in some cases open the door to more serious security threats. The presence of suspicious software such as Almaricus Application or similar variants highlights how easily performance issues can escalate into broader security concerns.
Table of Contents
What Is Almaricus Application?
Almaricus Application is tracked as an intrusive program that operates under the guise of a legitimate or benign utility. Although it may present itself with friendly branding elements, its behavior suggests otherwise. Systems affected by this application often experience overheating, sluggish performance, and unusually high CPU consumption.
One of the most noticeable indicators is a background process consuming significant processing power. Users may observe system fans running at full speed, delayed response times when clicking, and video playback stuttering. In Task Manager, suspicious entries such as AlmaricusApplication or similarly named executables may appear at the top of the CPU usage list.
Performance Impact and Hidden Activity
The primary concern with Almaricus Application is its excessive resource consumption. Reports indicate behavior consistent with hidden cryptocurrency mining activity. When mining operations run silently in the background, they continuously utilize processor resources, leading to:
- Persistent high CPU usage
- Increased GPU strain in some cases
- Overheating hardware components
- Reduced overall system lifespan
- Noticeable lag and system instability
In addition to performance degradation, the application may establish persistence mechanisms. These can include the creation of background services such as AlmaricusService, startup entries, or scheduled tasks designed to relaunch the program after reboot.
Such persistence tactics make manual removal challenging and increase the risk of reinfection if remnants remain.
Security Risks Beyond Performance Issues
While high CPU usage is disruptive, the broader security implications are more concerning. Intrusive applications of this type may:
- Modify browser settings
- Inject unwanted advertisements
- Redirect search queries
- Collect browsing-related data
- Open pathways for additional malware
Even if initially classified as a PUP rather than outright malware, the system modifications and data exposure risks caused by Almaricus Application justify serious attention.
How Almaricus Application Gets Installed
One of the most problematic aspects of PUPs is their deceptive distribution strategy. Almaricus Application rarely appears through transparent, standalone downloads. Instead, it often infiltrates systems using questionable tactics such as:
Software Bundling
Freeware installers frequently include optional components pre-selected by default. Users who rush through installation steps without reviewing advanced or custom settings may unknowingly approve the installation of additional programs.
Pirated and Cracked Software
Unofficial software distribution platforms are a common source of bundled threats. Modified installers may include hidden payloads that deploy intrusive applications during setup.
Fake Download Pages
Imitation websites that mimic legitimate software portals can trick users into downloading tampered installers. These pages may advertise updates or performance tools that actually deploy unwanted programs.
Misleading Prompts and Ads
Aggressive pop-ups claiming that a system is outdated or infected may push users to download 'optimization' utilities. These downloads frequently contain bundled PUPs.
Such tactics rely heavily on user inattention and misleading design rather than explicit consent.
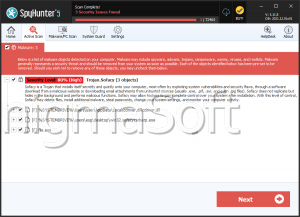
Why Professional Security Tools Are Recommended
Manually removing intrusive applications can be complicated and risky. Leftover files, registry entries, or hidden tasks may allow the program to reinstall itself silently. Security professionals strongly recommend using reputable anti-malware solutions capable of:
- Detecting persistence mechanisms
- Removing associated services and tasks
- Cleaning residual files and registry modifications
- Blocking related variants in the future
Automated security tools significantly reduce the chance of reinfection and ensure a more thorough cleanup process.
Final Thoughts
Almaricus Application demonstrates how seemingly harmless programs can quietly undermine system performance and security. Persistent CPU spikes, overheating hardware, and unexplained slowdowns should never be ignored. Intrusive applications often signal deeper issues and may expose systems to additional threats.
Maintaining updated security software, avoiding unofficial download sources, and carefully reviewing installation steps remain the most effective defenses against PUPs and similar intrusive software.