At Least 500 WordPress and Joomla Sites Compromised by Aggressive Shade Ransomware Campaign
 Security researchers recently discovered a hidden HTTP directory that appears to allow attackers to use WordPress and Joomla to install the Shade ransomware.
Security researchers recently discovered a hidden HTTP directory that appears to allow attackers to use WordPress and Joomla to install the Shade ransomware.
The campaign of ransomware managed to compromise hundreds of online properties, potentially aiming at thousands, according to Zscaler. Victims of the attack were fooled by phishing emails with an attached ZIP file containing a JavaScript. The script downloaded and executed the Shade ransomware on the infected machines.
What targets are likely to be a target of phishing?
WordPress and Joomla are currently one of the most used content management systems. The current threat posed by the Shade ransomware is most likely to affect websites that run outdated plugins, themes, and software. The most vulnerable websites are likely to be running WordPress versions 4.8.9 to 5.1.1.
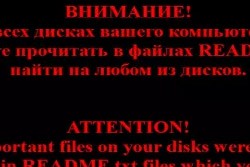
Using a directory means that the people behind these attacks can hide a number of files, such as the Shade ransomware from the admins of Joomla and WordPress. Once the payload of the threat gets executed, the wallpaper on a victim's machine is changed to show a ransom note in both English and Russian.
The attackers have also taken steps to use phishing pages that happen to imitate some of the commonly used productivity tools, such as Dropbox, Gmail and OneDrive. There were pages made to specifically imitate company and banking websites such as those of DHL, Bank of America and so forth. This likely means the threat actors were after usernames, passwords and sensitive personal data.
How the Shade Ransomware campaign operates
While the source of the current issues with Shade against Joomla and WordPress users is not known at this time, security teams and users are advised to react fast to limit the potential spread of these phishing attacks.
The Shade ransomware, also known under the name Troldesh, is a typical representative of the cryptovirus type threats seen gaining popularity these days. What it does is encrypt a number of important or commonly used files on a victim's computer using an AES-256 encryption method. Once this task is complete, it drops a ransom note in a visible place so users can see it. The threat appends the filenames with the .ID_of_infected_machine.crypted000007 extension, making them unusable unless they're decrypted.
Shade uses two ways to deliver the ransom money back to the people behind its spread: Tor server and email. In the first case users are directed to access the anonymous browser and to follow the transfer instructions to pay the ransom. No matter what kind of data it is, there is no guarantee that the people behind the Shade ransomware will unlock the files again, so users and companies are advised to avoid paying any ransom at all.
The cybercriminals have made improvements to the Shade ransomware, so it may be possible it may install a remote access tool (RAT) when it installs itself onto a victim's computer. The ransomware appears to check for any documents that indicate the computer was used in departments of Russian-speaking organizations.
Once documents like that are detected, it installs a Teamspy trojan instead. This specific trojan drops a modified version of NirCmd utility, TeamViewer, 7ZIP and the RDP Wrapper Library on the infected computer. With the help of this set of tools, the cybercriminals may attempt to modify the operating system and to take control of an infected PC by remote.