Beware: UPS Delivery Notification Tracking Number Spam Campaigns on the Rise
With the holidays here, there will be a major influx of the number of shipments through many services like UPS. During this time, it is not uncommon to see an increase in shipment notification emails circulating as people want to receive their packages in a prompt and unharmed manor. Cybercrooks know this very thing and have ramped up their efforts to circulate UPS Delivery Notification Tracking Number-themed spam messages laced with malicious attachments.
According to Panda Security, there are two primary delivery mechanisms that hackers are using when sending out bogus UPS Deliver Notification Tracking Number messages, the use of a link and an attached file. Both methods have proven to be effective as the malicious link included with this specific spam campaign email is one that redirects users to download a malicious file. In the case of an attachment within the spam message, the attachment contains virtually the same malware threat that the link takes you to for download.
Figure 1. Example of UPS Delivery Notification Tracking Number Spam message - Source: Bart Blaze
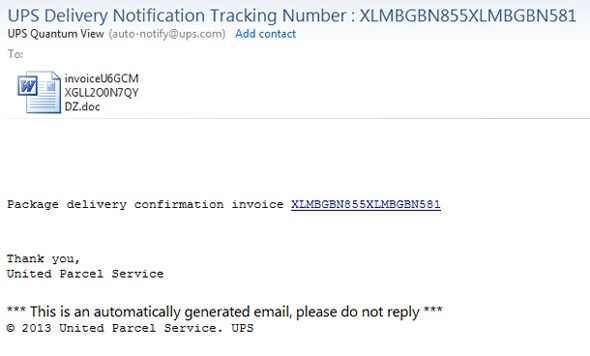
Digging deep into the spam UPS Delivery Notification Tracking Number email messages, as demonstrated in figure 1 above, the file appears to be a harmless Microsoft Office document at first glance. In reality, behind the file is that it is actually a maliciously crafted .rtf file that exploits a vulnerability within Microsoft Office. The vulnerability has been identified as CVE-2012-0158 and CVE-2010-3333.
When the file is executed, it will then crash Microsoft Word while other processes are created and another component is dropped into the vulnerable system, thus infecting it with malware.
Security experts have found where this particular malware associated with UPS Delivery Notification Tracking Number spam campaign messages, contacts various domains including the following:
- customer.invoice-appmy.com
- customers.invoice-appmy.org
- customer.appmys-ups.orgfeed404.dnsquerys.org
- feed.queryzdnsz.org
- feeds.nsupdatedns.com
- feed404.dnsquerys.com
- static.invoice-appmy.com
Some network administrators who may see traffic directed through the domains listed above as a simple DNS query or request and would not be the wiser for suspecting malware contacting the domains. The payload of the malware associated with this spam campaign is one similar to the famous Zeus or Zbot infections, which leads us to believe that this emerging spam campaign may become a serious epidemic.