Stuxnet-Related APTs used to create New 'Gossip Girl' Threat
 The infamous family of industrial sabotage malware, known as Stuxnet, is now considered to be the likely work of a so-called 'Gossip Girl' group of individuals. Gossip girl is believed to be busier and larger than expected, at least according to researchers Silas Cutler and Juan Andres Guerrero Saad.
The infamous family of industrial sabotage malware, known as Stuxnet, is now considered to be the likely work of a so-called 'Gossip Girl' group of individuals. Gossip girl is believed to be busier and larger than expected, at least according to researchers Silas Cutler and Juan Andres Guerrero Saad.
In Singapore, at the Security Analyst Summit in 2019, Saad and Cutler shared their suspicions that the APT groups and developers behind Flame, Duqu and the Equation Group (previously linked to the NSA) now have a fourth collaborator behind it, known as Flowershop. The researchers reached this conclusion after uncovering an element of the early Stuxnet they named 'Stuxshop'.
They also opened up about the other research regarding Gossip Girl, the discovery of Duqu 1.5, which now shows an unknown middle stage of the development of the malware's code. They also shared the discovery of a new variant of the Flame malware, one dubbed Flame 2.0, which shows that the code was brought back after seemingly not being used anymore. All the while Flame 2.0 was active between 2014 and 2016.
Looking for the connections between all of these threats, Cutler and Saad claim there is evidence of the existence of a modular framework of development that is overseen by a group of 'apex threat actors' they now dubbed Gossip Girl. Looking at the connections between different APTs offered more perspective on the threat actor and how it may affect the online community.
Table of Contents
Stuxshop
Stuxnet was known for its use against Iran's nuclear industry back in 2011. The old Stuxnet components were found by the two researchers to share code with Flowershop. This was an older spyware threat used as far back as 2002. It was used to attack targets in the Middle East, with it first discovered in 2015 due to Kaspersky Lab researchers. It gained its name due to the mention of the word 'flower' in the associated domains of its command and control server infrastructure.
The older code that was discovered had four specific points of overlapping with Flowershop. The analysis showed three of them have an implementation of functionality to search for infection markers in registry keys, as well as looking for internet proxy settings. The fourth function overlap is a reuse of the code that evaluates the OS version. The fact that the code is only shared by Stuxshop and Flowershop samples shows the reuse of a closed source code, according to the researchers.
These findings place Flowershop alongside Equation, Duqu, and Flame as teams who worked on the different phases of developing Stuxnet since the early 2006. According to Saad, the recent finding shows that yet another team has its own malware platform used in the early development of Stuxnet. It also proves that Stuxnet is part of a modular development that allows collaboration between threat actors.
Duqu 1.5
The code researchers are calling Duqu 1.5 is known to share code with Stuxnet, with the researchers mentioning the main Stuxnet kernel drivers have shared development links with the Duqu 'Tilde-D platform', one that involves this threat actor in the active development of central components to Stuxnet. Where Stuxnet is now infamous for its damage and industrial sabotage capability, Duqu was mostly used as spyware on companies across the Middle East, Africa and Europe. Despite its heightened activity in 2011, it went under the radar until it resurfaced again in 2015, when Kaspersky discovered its 2.0 version.
This new version was overhauled to work almost completely in memory, meaning away from the detection capability of most security software, according to Cutler and Saad. It has an almost worm-like capability to spread across networks. It was discovered in the venues hosting the P5+1 negotiations regarding the Iranian nuclear program, according to Kaspersky.
The benefits of this approach make it so incident responders have to be at a site of infection to identify and check for this seemingly innocent file. If the parent malware ends up analyzed this alone will not give researchers the chance to retrieve the submodules and to see more of the scope of the attacker's actions.
The most important conclusion, according to the two researchers, is that the people behind Duqu were ready and willing to completely change the way their malware works after it was discovered. They went the extra mile to do this in a way that shows a new, collaborative approach to malware development, which they see as the signs of the Gossip Girl supra group.
Flame 2.0
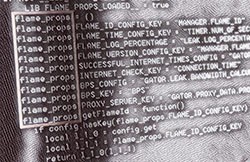
The researchers also found a new version of the cyberespionage toolkit Flame, one that also shares code overlapping with Stuxnet, something Kaspersky found in 2012 with an older version of Stuxnet that included a Flame plugin called Resource 207. This turns out to be an important hint, as the older versions of Flame's command and control servers started sending off updates that turned on a self-deletion command to the remaining Flame infections, thus burning their operations and destroying any signs of their tracks. The side effect of this was that the research community was able to get a full list of components and directories used by the previous version of Flame. According to Cutler and Saad, that was the death of that malware.
It turns out that was a ruse, as a subset of timestamped compilation dates all the way back to February 2014, nearly two years after Flame operations were believed to be abandoned were recently discovered.
Although the malware was built with the Flame source code, it now includes new countermeasures against meddling by researchers, which makes working on understanding Flame 2.0 more difficult. The hopes are announcing the findings at such an early stage will push the threat intelligence space to pull an equally collaborative effort to stand against it.
When Stuxshop, Flame 2.0 and Duqu 1.5 are put next to each other, a better picture of the whole emerges, rather than separate groups, researchers see ties to Stuxnet that very likely continue in secret on separate projects. According to Saad and Cutler, Gossip Girl isn't the first supra threat actor discovered by the community, but it is the first to be described in a more comprehensive way.