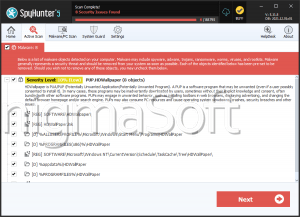
PUP.Somoto.A
Table of Contents
Analysis Report
General information
| Family Name: | PUP.Somoto.A |
|---|---|
| Signature status: | Self Signed |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
869c8bd31d784bb9a642f6e62430fef9
SHA1:
e833ec5e5f8909402d1020e17972cea82627122c
SHA256:
6D0D911CB3FCC3744CF418E414FD3DCD00E351847E71BA715F9A4C0104E3491E
File Size:
132.20 KB, 132203 bytes
|
|
MD5:
ee13a94f2b410bb6d2e7e933ef77887c
SHA1:
29fefb03e803e6430d7d0eaa47324a3691ca13f8
SHA256:
F1668B0851CA074893FF8FA2924910269FCFCFC3CBBD627F6B67ACFBB748CDAA
File Size:
125.41 KB, 125408 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | Somoto Ltd. |
| Company Website | www.FileBulldog.com |
| File Description | Powered by BetterInstaller |
| File Version |
|
| Product Name |
|
| Product Version | 1.0 |
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| DSNR | VeriSign Class 3 Code Signing 2010 CA | Self Signed |
File Traits
- Installer Version
- x86
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\nsha719.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
| c:\users\user\appdata\local\temp\nsha72a.tmp | Synchronize,Write Attributes |
| c:\users\user\appdata\local\tempdir\betterinstaller.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\tempdir\config.ini | Generic Write,Read Attributes |
| c:\users\user\appdata\local\tempdir\config.ini | Synchronize,Write Attributes |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
"C:\Users\Lbqhdndy\AppData\Local\TempDIR\betterinstaller.exe" /affid "etype" /id "etype" /name "eType"
|